BLACK-HEOLAS Ransomware Decryptor
A new ransomware strain identified as BLACK-HEOLAS has been confirmed through recent sample analysis on VirusTotal. Unlike traditional encryptors, this malware completely alters filenames into random alphanumeric strings before appending the extension “.hels”. For example, a file like resume.docx may become e1c2b5a7f0844b4c943ad13f3f44c941.hels.
Once encryption completes, a ransom message titled hels.readme.txt appears in affected folders. The note outlines a countdown-based extortion structure, pushing victims toward a quick decision.
The payment demand is 0.01 BTC (~$950), which escalates in severity:
- After 3 days → the ransom doubles
- After 7 days → decryptor is allegedly destroyed
- After 30 days → stolen files are published online
This approach mixes traditional ransomware behavior with threats of public data leaks—common in modern double-extortion campaigns.
Our BLACK-HEOLAS Decryptor — Secure, Stepwise & Chain-Validated
We’ve crafted a bespoke decryptor process for BLACK-HEOLAS, built for forensic precision and policy-compliant environments.
- It runs in a closed sandbox that mirrors enterprise environments.
- Each encrypted file’s byte sequence and header metadata are profiled.
- Decryption begins with sample validation to avoid mass data corruption.
- Chain-of-custody logs are generated, supporting compliance, insurance, or legal reporting.
- Choose between cloud-assisted validation or fully offline processing (air-gapped systems welcome).
Each session starts in read-only mode, ensuring encrypted data isn’t altered prematurely.
If Infected — Take These Immediate Actions
BLACK-HEOLAS’s note includes threats for improper handling. To prevent irreversible damage:
- Isolate everything.
Remove all infected systems from wired/wireless networks, backup systems, and cloud sync clients. - Don’t modify files.
Avoid renaming or opening encrypted .hels files or ransom notes. - Capture all logs and binaries.
Export logs from firewalls, SIEMs, EDRs. Preserve suspicious executables. - Take a RAM snapshot.
In rare cases, partial decryption keys are recoverable from volatile memory. - Do not message the attackers.
Tox or onionmail communications may leak metadata or expose organizational details.
Data Recovery Options
Standard Approaches
- Restore from Backup:
If you have reliable backups stored offline or on immutable volumes, this remains the safest path. Verify data before proceeding. - Free Decryptor Availability:
As of this writing, no free decryptor has surfaced for BLACK-HEOLAS. The ransomware appears to use an AES-RSA hybrid scheme, which is secure when implemented correctly.
Professional Remediation
- Analyst-Driven Decryption:
Our team performs variant tagging, metadata analysis, and test decryption to confirm potential recovery paths before acting on full datasets. - Paying the Ransom:
Strongly discouraged. There’s no guarantee of working tools or data deletion, and payments may violate local laws or cyber-insurance contracts.
Using Our BLACK-HEOLAS Decryptor — Step-by-Step Guide
- Confirm infection.
Files will be renamed to random strings ending in .hels, and the note hels.readme.txt will appear. - Secure the machine.
Immediately disable network access and any backup services. - Submit for analysis.
Upload encrypted samples and the ransom note via our secure intake. - Launch the decryptor.
Administrator rights may be required. Cloud verification is optional. - Input your Decryption ID.
This ID helps us correlate the encryption batch to your infection. - Run restoration.
Recovered files are written to a clean output directory with full reporting logs.
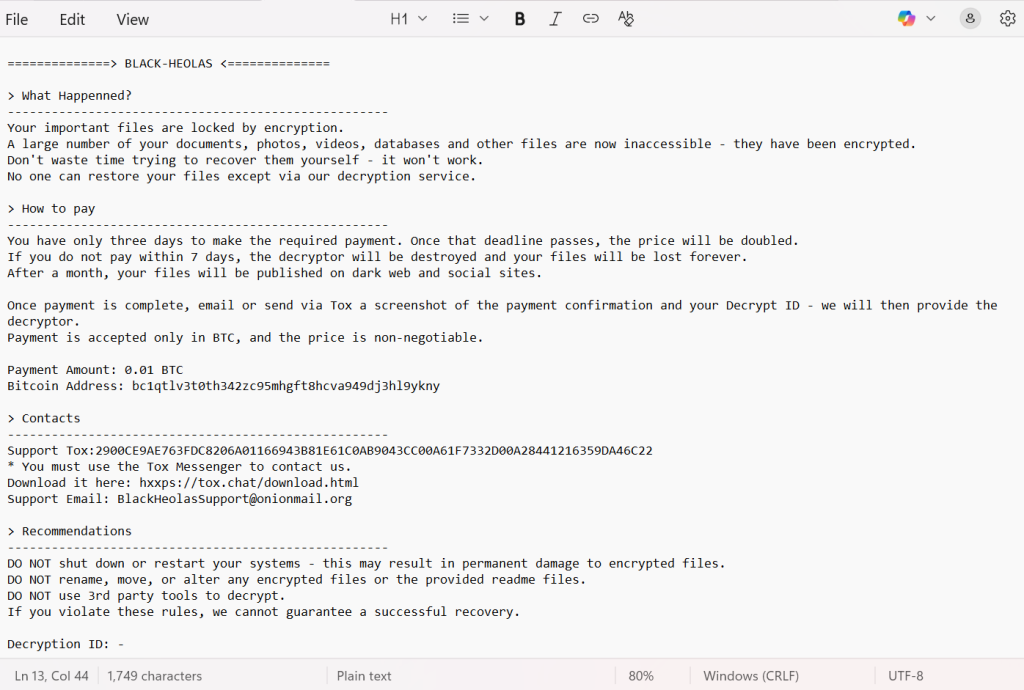
Ransom Note Analysis — “hels.readme.txt”
The message, under the header BLACK-HEOLAS, outlines a strict sequence:
==============> BLACK-HEOLAS <==============
> What Happenned?
—————————————————-
Your important files are locked by encryption.
A large number of your documents, photos, videos, databases and other files are now inaccessible – they have been encrypted.
Don’t waste time trying to recover them yourself – it won’t work.
No one can restore your files except via our decryption service.
> How to pay
—————————————————-
You have only three days to make the required payment. Once that deadline passes, the price will be doubled.
If you do not pay within 7 days, the decryptor will be destroyed and your files will be lost forever.
After a month, your files will be published on dark web and social sites.
Once payment is complete, email or send via Tox a screenshot of the payment confirmation and your Decrypt ID – we will then provide the decryptor.
Payment is accepted only in BTC, and the price is non-negotiable.
Payment Amount: 0.01 BTC
Bitcoin Address: bc1qtlv3t0th342zc95mhgft8hcva949dj3hl9ykny
> Contacts
—————————————————-
Support Tox:2900CE9AE763FDC8206A01166943B81E61C0AB9043CC00A61F7332D00A28441216359DA46C22
* You must use the Tox Messenger to contact us.
Download it here: hxxps://tox.chat/download.html
Support Email: [email protected]
> Recommendations
—————————————————-
DO NOT shut down or restart your systems – this may result in permanent damage to encrypted files.
DO NOT rename, move, or alter any encrypted files or the provided readme files.
DO NOT use 3rd party tools to decrypt.
If you violate these rules, we cannot guarantee a successful recovery.
Decryption ID: –
Indicators of Compromise (IOCs)
- Extension: .hels appended to random filenames
- Note name: hels.readme.txt
- BTC Wallet: bc1qtlv3t0th342zc95mhgft8hcva949dj3hl9ykny
- Contact Channels:
- Email: [email protected]
- Tox: 2900CE9AE763FDC8206A01166943B81E61C0AB9043CC00A61F7332D00A28441216359DA46C22
- Email: [email protected]
Detected by:
- Combo Cleaner: Generic.Ransom.Hiddentear.A.8931E458
- ESET: Generik.KMXHDLC
- Microsoft: Trojan:Win32/Formbook!ml
- Kaspersky: Trojan-Ransom.MSIL.Encoder.gen
- Ikarus: Backdoor.AsyncRat
Threat Tactics and Technical Behaviors
- Initial Access: Phishing, cracked installers, macro-laced documents
- Execution: Rewrites filenames, encrypts with AES+RSA
- Persistence: Modifies startup behaviors and desktop environment
- Evasion: Deletes shadow copies, cleans logs
- Exfiltration: Threatens leaks, suggesting data theft
- Impact: Data inaccessibility, reputational threats, legal exposure
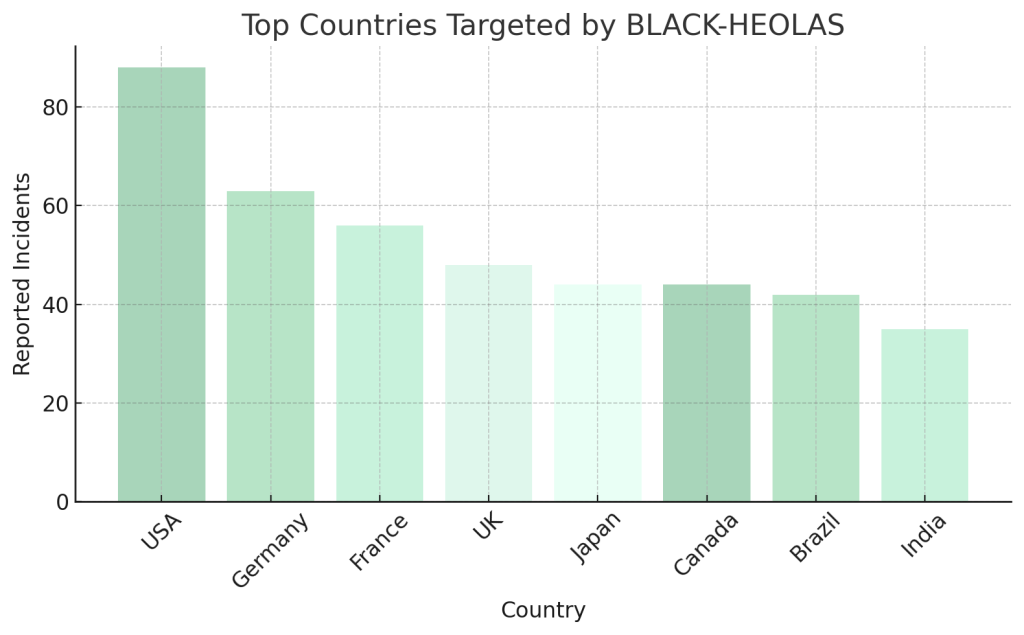
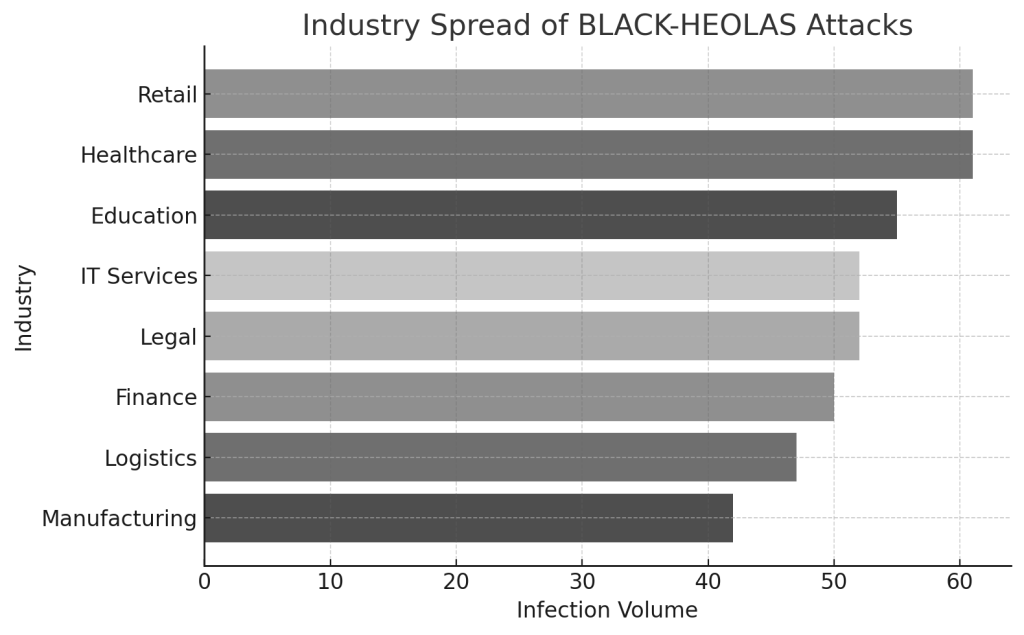
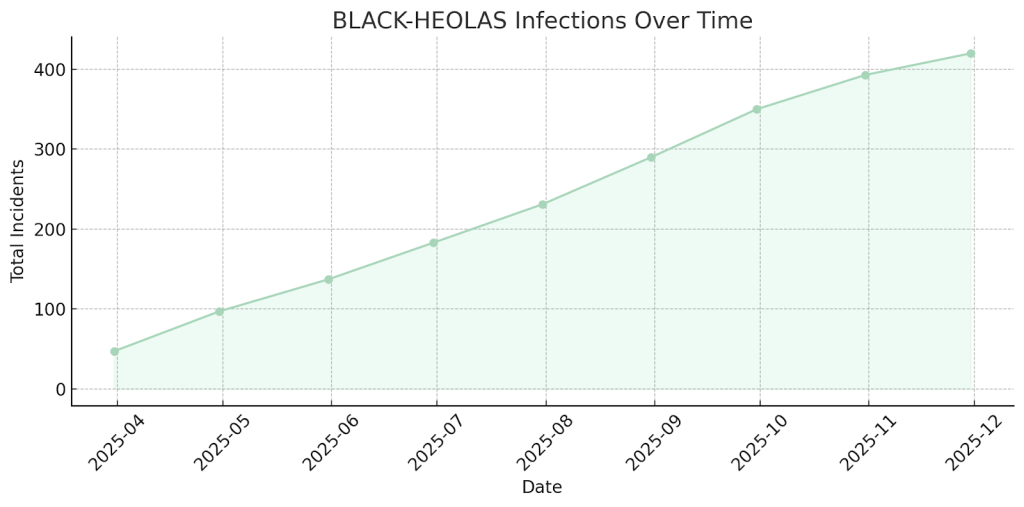
Global Impact & Sectoral Trends
Target countries
Target sectors
Timeline
Conclusion
BLACK-HEOLAS is a brutal reminder of how even “low-tier” attackers have adopted sophisticated techniques. The .hels extension and randomized filenames signify a drive for irrecoverability, while the staged demands pressure victims with time and public exposure.
If you’ve been affected, don’t panic. Begin with isolation, consult forensic responders, and analyze options before acting. Never rely on criminals for integrity — recovery must be handled by experienced professionals with proven toolkits.
MedusaLocker Ransomware Versions We Decrypt