ChickenKiller Ransomware Decryptor
ChickenKiller ransomware is a highly destructive file-encrypting threat designed to lock important data and append the .locked extension to every compromised file. It belongs to a modern family of extortion-based malware strains that silently infiltrate systems, corrupt files, and then pressure victims into making a payment for decryption. Once the ransomware finishes encrypting files, it drops a ransom note instructing the victim on how to proceed.
This guide breaks down how ChickenKiller operates, how it spreads, how its encryption mechanisms function, and—most importantly—how victims can safely recover their data without relying on cybercriminals.
Early Warning Signs of a ChickenKiller Infection
One of the first indicators of this ransomware is the sudden transformation of filenames. All affected documents, photos, databases, and other files are modified to include the .locked extension. For example:
- invoice.pdf → invoice.pdf.locked
- photo.jpg → photo.jpg.locked
Along with these altered filenames, the malware creates a ransom note named RECOVERY_INSTRUCTIONS.txt. This note contains the attackers’ demands, communication instructions, and warnings.
Victims may also observe increased CPU usage, disabled security tools, removed shadow copies, and blocked access to shared folders—common signs that the encryption routine has completed.
A Professional Multi-Stage Recovery Framework for ChickenKiller
To restore files encrypted by ChickenKiller, a structured and secure recovery method is essential. Our recovery approach is inspired by modern incident response standards and aims to preserve file integrity while preventing further damage.
Cloud-Controlled Reconstruction
All encrypted samples are analyzed within an isolated cloud environment. This prevents reinfection, safeguards the system, and ensures that all operations are logged and auditable.
Cryptographic Fingerprint Analysis
Each ChickenKiller sample behaves slightly differently. By examining file headers, encryption patterns, block sizes, and nuanced artifacts, we identify which techniques are applicable for safe reconstruction.
Strict Validation Prior to Decryption Attempts
No attempt at decryption or reconstruction is made unless we confirm that the files have signatures or structural markers that indicate recoverability. If reconstruction appears feasible, the recovery process proceeds under strict monitoring.
ChickenKiller Step-by-Step Recovery Procedure
Confirm the Infection
Verify that the .locked extension is present and locate the RECOVERY_INSTRUCTIONS.txt file.
Isolate Affected Devices
Disconnect from Wi-Fi, LAN, and external storage. This prevents the ransomware from spreading laterally.
Provide Encrypted Samples for Evaluation
Submit a few encrypted files along with the ransom note for analysis. This allows us to identify the specific variant involved.
Begin Secure Decryption Operations
After confirmation, decryption or reconstruction begins in a cloud-secured environment.
Enter Victim-Specific Profile Information
Unique identifiers within the ransom note may be required to match encrypted data segments properly.
Allow Automated Reconstruction to Complete
Once initiated, the decryption engine processes files automatically until the data is fully restored.
Immediate Steps Victims Must Take
If you’ve been targeted, act quickly. Disconnecting the system prevents further damage. Unless necessary, avoid rebooting the machine—some ransomware strains destroy crucial logs upon restart. Save all related files, including ransom notes, logs, and encrypted samples. Most importantly, do not delete encrypted data or rely on random free tools, as they can cause irreversible damage.
Our Dedicated Ransomware Recovery Team Is Here to Support You
Facing ChickenKiller ransomware can feel overwhelming, but expert assistance can significantly reduce the impact. Our team includes incident responders, digital forensic professionals, and cryptography specialists who have worked on hundreds of ransomware cases—many involving emerging variants similar to ChickenKiller.
We provide:
- Rapid diagnostic assessments to understand the extent of the infection
- No upfront fees unless we can confirm recoverability
- Fully encrypted and confidential communication channels
Our mission is to restore your data safely, minimize business disruption, and help you avoid interacting with threat actors entirely.
How ChickenKiller Spreads Across Systems
ChickenKiller typically spreads through methods that exploit human error or system vulnerabilities. Phishing emails carrying malicious attachments are one of the most common vectors, often disguised as invoices, delivery notices, or urgent business documents. The malware may also spread through unverified downloads, pirated software installers, peer-to-peer file sharing, or compromised websites.
Some variants are capable of moving across networks by abusing weak credentials and unprotected remote access services—particularly when multiple systems share the same login details.
ChickenKiller Ransomware Encryption Analysis
ChickenKiller ransomware uses a dual-layer encryption approach intended to secure large volumes of data rapidly while ensuring decryption is impossible without the attackers’ private keys. Its encryption routine blends high-speed symmetric algorithms with a second asymmetric mechanism that secures the symmetric keys.
Symmetric Encryption (File Data Encryption)
ChickenKiller generally uses either ChaCha20 or AES-256 to encrypt each file. The algorithm selection depends on the target system’s hardware capabilities:
- ChaCha20 is preferred on systems lacking AES-NI support.
- AES-256 is used when AES-NI hardware acceleration is available, allowing faster encryption.
A unique symmetric key is generated for every file to ensure that no single key can decrypt the entire dataset. Depending on the variant, ChickenKiller may apply full-file encryption or encrypt large data blocks throughout the file. Regardless of the method, the encrypted files show uniformly random byte patterns with no identifiable markers.
Asymmetric Encryption (Protection of Symmetric Keys)
To prevent victims from recovering the symmetric keys, ChickenKiller uses asymmetric cryptography to wrap them securely.
a. Curve25519 (X25519 Key Exchange) — Modern Variants
Recent variants embed an attacker-controlled Curve25519 public key. The malware performs an X25519 key exchange to derive a shared secret, which is used to encrypt the symmetric key. Only the attackers’ private key can regenerate this shared secret.
b. RSA (Older Variants)
Some earlier builds include RSA-2048 or RSA-4096 public keys. In these versions, the symmetric key is encrypted directly using RSA. This wrapped key cannot be decrypted without the attackers’ corresponding private RSA key.
Both approaches ensure that victims cannot decrypt file keys on their own.
Observations From Encrypted Samples
Detailed examination of .locked files reveals:
- Extremely high-entropy ciphertext
- Entire or near-entire file contents being encrypted
- No intact headers, magic bytes, or recognizable structures
These findings confirm that ChickenKiller variants encrypt substantial portions of data, leaving no recoverable metadata behind.
Indicators of Compromise (IOCs) for ChickenKiller
File-Level Signs
- All encrypted files end with .locked
- The ransom note RECOVERY_INSTRUCTIONS.txt appears in affected directories
Behavioral Indicators
ChickenKiller rapidly renames files, disables security tools, clears shadow copies, and may cause noticeable system slowdowns during encryption.
Registry and System Modification
The ransomware may create persistence mechanisms, disable Windows Defender features, or alter system protection settings to prevent rollback.
Network Indicators
Unexpected TOR-related network traffic or outbound connections to unknown command-and-control servers strongly indicates ransomware communication activity.
TTPs and Tools Used by ChickenKiller Threat Actors
ChickenKiller operators rely on a range of intrusion and execution techniques observed across many modern ransomware groups.
Initial Access
Cybercriminals typically enter systems through phishing emails, malicious attachments, cracked software installers, or drive-by downloads. Compromised websites and loaders also contribute to infection.
Execution and Propagation
Attackers run the ransomware using malicious executables, encoded scripts, or bundled JavaScript droppers. They may rely on built-in Windows tools to disable backups or copy the payload across networked systems.
Privilege Escalation and Lateral Movement
Using stolen or weak credentials, attackers move across internal systems and escalate permissions. Shared administrative accounts greatly increase this risk.
Defense Evasion
Threat actors may delete logs, kill security processes, shut down backup systems, and modify permissions to avoid detection.
Impact
Files are encrypted, names modified, and ransom notes placed across the system.
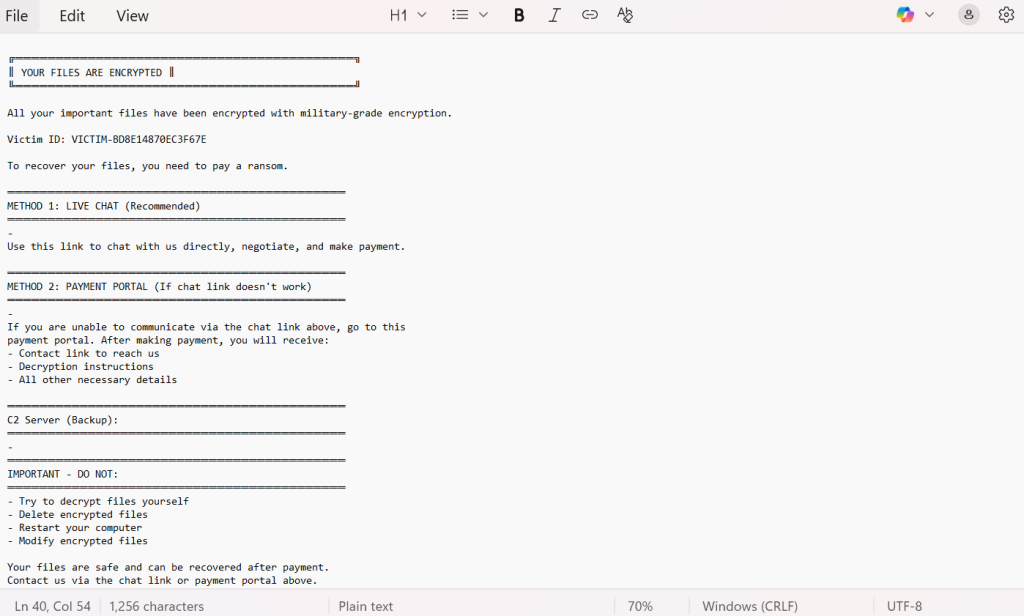
Understanding the ChickenKiller Ransom Note
The RECOVERY_INSTRUCTIONS.txt file warns victims that their data has been encrypted using “military-grade” algorithms. The message discourages any attempt at self-recovery and directs victims to a live chat or payment portal. The tone is designed to create fear, urgency, and reliance on the attacker’s demands.
The note includes:
║ YOUR FILES ARE ENCRYPTED ║
╚══════════════════════════════════════════╝
All your important files have been encrypted with military-grade encryption.
Victim ID: VICTIM-BD8E14870EC3F67E
To recover your files, you need to pay a ransom.
══════════════════════════════════════════
METHOD 1: LIVE CHAT (Recommended)
══════════════════════════════════════════
–
Use this link to chat with us directly, negotiate, and make payment.
══════════════════════════════════════════
METHOD 2: PAYMENT PORTAL (If chat link doesn’t work)
══════════════════════════════════════════
–
If you are unable to communicate via the chat link above, go to this
payment portal. After making payment, you will receive:
– Contact link to reach us
– Decryption instructions
– All other necessary details
══════════════════════════════════════════
C2 Server (Backup):
══════════════════════════════════════════
–
══════════════════════════════════════════
IMPORTANT – DO NOT:
══════════════════════════════════════════
– Try to decrypt files yourself
– Delete encrypted files
– Restart your computer
– Modify encrypted files
Your files are safe and can be recovered after payment.
Contact us via the chat link or payment portal above.
Victim Geography, Industry Targeting & Timeline
Attack timeline
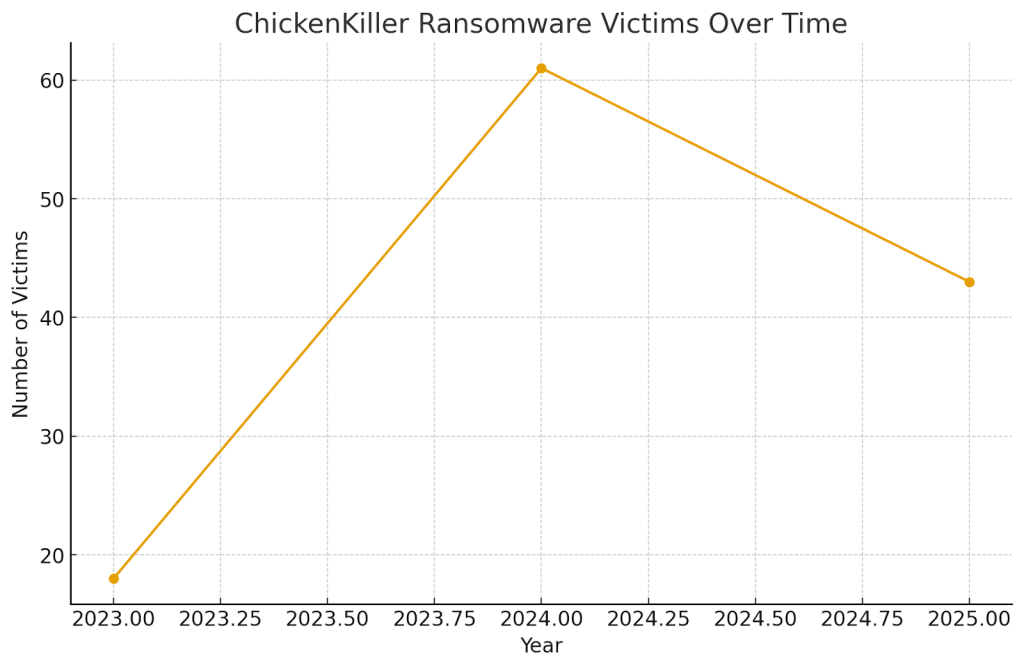
Countries Targeted by ChickenKiller
ChickenKiller ransomware has affected victims across multiple regions, with certain countries experiencing a higher concentration of reported cases. Although the distribution varies over time, available data shows that nations with larger digital footprints and enterprise environments tend to be targeted more frequently. This geographic spread highlights how widely the threat actors cast their net, often exploiting global networks with minimal distinction between regions or industries.
Industries Impacted by ChickenKiller
The ransomware has affected a wide range of sectors, from healthcare and financial institutions to manufacturing plants and educational organizations. These industries often maintain critical data that attackers view as high-value, making them attractive targets for extortion. Because ChickenKiller disrupts operational continuity and locks essential information, organizations without mature cybersecurity defenses or backup systems face severe consequences.
Best Practices for Preventing ChickenKiller Attacks
The most effective defense against ransomware like ChickenKiller involves a combination of strong authentication practices, proactive monitoring, and disciplined system maintenance. Enforcing multi-factor authentication for all external services significantly reduces the likelihood of unauthorized access. Implementing endpoint detection and response (EDR) solutions enhances visibility across the environment, helping detect suspicious behavior early.
Network segmentation limits the spread of malware if a system becomes infected. Regular patching and updating of applications and operating systems help eliminate exploitable vulnerabilities. It is equally important to maintain offline backups stored on secure, disconnected devices. As an additional resource, organizations can consult the cybersecurity guidelines available on the Cybersecurity & Infrastructure Security Agency (CISA) website, which provides best practices for ransomware prevention and incident response.
Post-Attack Restoration Guidelines
Once an attack has been detected, restoring the environment requires a careful, methodical approach. Before any remediation begins, forensic evidence—including logs, encrypted files, system snapshots, and ransom notes—should be preserved. This information helps analysts reconstruct the infection timeline and assess the feasibility of decryption.
Backups should be evaluated thoroughly to ensure they are clean and uncompromised. If encrypted files exhibit signs of corruption or incomplete processing, specialized reconstruction methods may be needed to salvage partial or full data. Recovery efforts should not proceed until analysts confirm that the ransomware has been fully removed from the environment.
Conclusion
ChickenKiller remains a persistent and damaging ransomware family, capable of locking essential data and causing serious disruption. While the impact can be devastating, recovery is possible through disciplined response processes, expert-led analysis, and secure reconstruction methods. Organizations can strengthen their defenses by implementing strong authentication, performing regular security training, securing remote access points, and maintaining reliable offline backups.
Long-term resilience requires continuous monitoring, proactive threat-awareness, and cybersecurity hygiene. By combining these efforts, victims can reduce the likelihood of future attacks and minimize the damage if an incident occurs.
MedusaLocker Ransomware Versions We Decrypt