H2OWATER Team Ransomware Decryptor
Our advanced H2OWATER decryptor framework has been engineered with insights from digital forensics and cryptographic research. The recovery process combines AI-driven entropy mapping with heuristic key analysis to maximize the probability of data restoration—without negotiating with cybercriminals.
This ransomware strain, developed in Go, encrypts files using AES-256 in CTR mode and secures encryption keys with RSA-2048. Because it does not append a visible extension to files, victims may initially overlook the compromise until files fail to open.
How Our H2OWATER Decryption Method Works
- AI-Powered + Blockchain Verification – Encrypted samples and ransom notes are evaluated against cryptographic markers. Integrity of recovery operations is verified through blockchain-linked audit trails.
- ID and Hash Correlation – While ransom note structures are not fully exposed yet, forensic identifiers such as SHA-1 case IDs uploaded by victims can help classify variants and build correlation maps.
- Universal Key Testing – In instances where the ransom note is missing, our premium toolkit inspects the AES-CTR randomization routines and RSA key usage. Any reuse of weak public keys may open a recovery path.
- Safe Execution Protocol – All file analysis occurs in a read-only environment first, ensuring that no further corruption happens during recovery attempts.
Requirements for Running the H2OWATER Decryptor
- Access to the ransom note (archived victim ZIPs indicate its presence, though text remains mostly undisclosed).
- Samples of encrypted files across different formats such as DOC, PNG, and JPG.
- Internet connection for cloud-based cryptographic processing.
- Administrative rights (local or domain) to deploy the decryption utilities.
Initial Response Checklist: What to Do After a H2OWATER Attack
Isolate the Environment
Immediately disconnect affected machines from networks. Since attackers are known to install this ransomware manually, leaving systems connected may invite re-encryption or further compromise.
Preserve Evidence
Keep ransom notes intact. Do not delete encrypted files, event logs, or traces. These are crucial for decryption testing and forensic analysis.
Power Down Securely
Instead of rebooting, which could trigger attacker scripts or data-wiping tasks, shut down compromised machines carefully. Create forensic images if possible.
Engage with Specialists
Avoid using unverified “free decryptors” found online. These often corrupt files. Instead, work with professionals who have reverse-engineered Go-based ransomware and understand advanced cryptographic failure points.
Decryption and Data Recovery Options for H2OWATER
H2OWATER is still a relatively new ransomware family, first reported in late 2025. Because intruders install it manually after breaching systems, off-the-shelf decryptors are not yet available. However, several options exist:
Free Recovery Options
Attempts to submit samples to ID Ransomware, NoMoreRansom, and Malcore have not produced results. At present, no universal decryptor exists.
Still, it is critical to archive encrypted files, as researchers may publish free decryption tools in the future if cryptographic flaws (such as AES-CTR nonce reuse) are discovered.
Restore from Backups
- The most reliable approach is restoring from clean, offline or immutable backups.
- Always validate snapshots against checksums before rollback.
- If shadow copies were deleted locally, investigate offsite storage or cloud-based immutable backups.
Virtual Machine Snapshots
If your infrastructure uses VMware ESXi, Proxmox, or Hyper-V, pre-attack snapshots may allow rollback of encrypted machines.
- Always confirm snapshot integrity before rolling back.
- Preserve hypervisor logs for forensic review.
Third-Party Research Tools
Currently, there are no open-source decryption scripts or brute-force projects available for H2OWATER. However, its Go-compiled static binaries could lead to detection rules (YARA, Sigma) or even key analysis projects in the future.
Paid Decryption (High Risk)
Paying the ransom should be considered a last resort, due to:
- No guarantee of receiving functional decryptors.
- Risk of hidden malware in attacker-provided tools.
- Potential legal liability under sanctions and compliance laws.
Professional Negotiation Services
Some organizations turn to negotiators to interact with attackers. Their role is to:
- Attempt ransom reductions.
- Validate decryptors through controlled test files.
- Keep executives shielded from direct communication.
This is costly and still risky, with no assurance of success.
Our Proprietary H2OWATER Decryptor
Our internal toolset is specifically tailored for ransomware families like H2OWATER that combine AES-256 CTR with RSA-2048.
- Reverse-Engineered Cryptographic Utilities – Detect weaknesses in Go’s CTR implementation, if present.
- Cloud Sandbox Environments – Decryption attempts occur securely, with integrity verified before data release.
- Fraud-Resistant Processing – Protects clients from fake decryptors by validating through trusted forensic pipelines.
Step-by-Step Guide to H2OWATER Data Recovery
- Assess Signs of Infection
- Files appear unchanged (no new extension) but fail to open.
- Look for ransom notes (name not yet publicly disclosed).
- Confirm attacker contact addresses: [email protected] and [email protected].
- Files appear unchanged (no new extension) but fail to open.
- Secure Compromised Systems
- Disconnect affected servers.
- Disable or reset compromised administrative accounts.
- Disconnect affected servers.
- Submit Samples
- Provide ransom notes and encrypted files to specialists for identification.
- Provide ransom notes and encrypted files to specialists for identification.
- Run the Decryptor
- If future tools are available, input case ID and proceed with administrator-level execution.
- If future tools are available, input case ID and proceed with administrator-level execution.
Offline vs Online Decryption: Key Differences
- Offline Approaches: Best for air-gapped or forensic investigations. Prevents further attacker contact but may slow down results.
- Online Methods: Provide faster recovery by using cloud AI decryptors, but require secure data transfer protocols.
What is H2OWATER Team Ransomware?
H2OWATER is an emerging ransomware family that surfaced in September 2025. Its design reflects professional coding practices and targeted enterprise compromises.
- Language: Written in Go, enabling cross-platform builds.
- Cryptography: AES-256 in CTR mode for files, RSA-2048 for key encryption.
- File Extensions: None applied to encrypted files, making infections stealthier.
- Deployment: Manually installed after attackers breach servers.
- Ransom Notes: Known to exist, though filenames are not yet confirmed.
- Contact Emails: [email protected], [email protected].
- Observed Targets: Corporate staging servers, with potential expansion to larger enterprise environments.
Tools, Tactics, and MITRE ATT&CK Techniques Linked to H2OWATER
Like other modern ransomware operations, H2OWATER demonstrates a clear pattern of targeted intrusion and deliberate execution rather than opportunistic “spray and pray” infections. Analysis to date shows alignment with several MITRE ATT&CK techniques.
- Attackers appear to rely on compromised credentials (T1078 – Valid Accounts) to gain entry.
- Remote desktop services and SSH endpoints are likely abused for login attempts (T1133 – External Remote Services).
- Evidence strongly suggests that operators manually deploy the ransomware binary after breaching servers.
- The threat is delivered as a large compiled Go binary, executed locally once attackers have a foothold.
- In enterprise environments, it may be launched remotely through PsExec, PowerShell scripts, or custom command shells.
- File data is secured with AES-256 in CTR mode, providing strong symmetric encryption.
- The AES keys themselves are locked with RSA-2048 public key encryption, preventing direct recovery without the attacker’s cooperation.
- No extension is added to files, which makes early detection more difficult.
- By avoiding the use of appended extensions, the malware reduces visibility.
- There is not yet confirmed evidence of shadow copy deletion or log wiping, but such actions are common in ransomware attacks and should be assumed possible.
- The primary observed technique is T1486 – Data Encrypted for Impact.
- As with most modern threats, the goal is to make data inaccessible and pressure victims into payment.
Indicators of Compromise (IOCs) for H2OWATER
- Attacker Contact Emails:
- Encryption Details:
- Algorithm: AES-256 CTR (file data)
- Key Protection: RSA-2048
- File Behavior: Encrypted files retain original names (no new extension)
- Algorithm: AES-256 CTR (file data)
- File Artifact:
- Reported case hash from ID Ransomware:
01553cb19cded56fde9d9389bf3460cf028856a4
- Reported case hash from ID Ransomware:
- Binary Characteristics:
- Likely compiled in Go
- May contain Go-specific build markers such as .gopclntab or go.buildid
- Likely compiled in Go
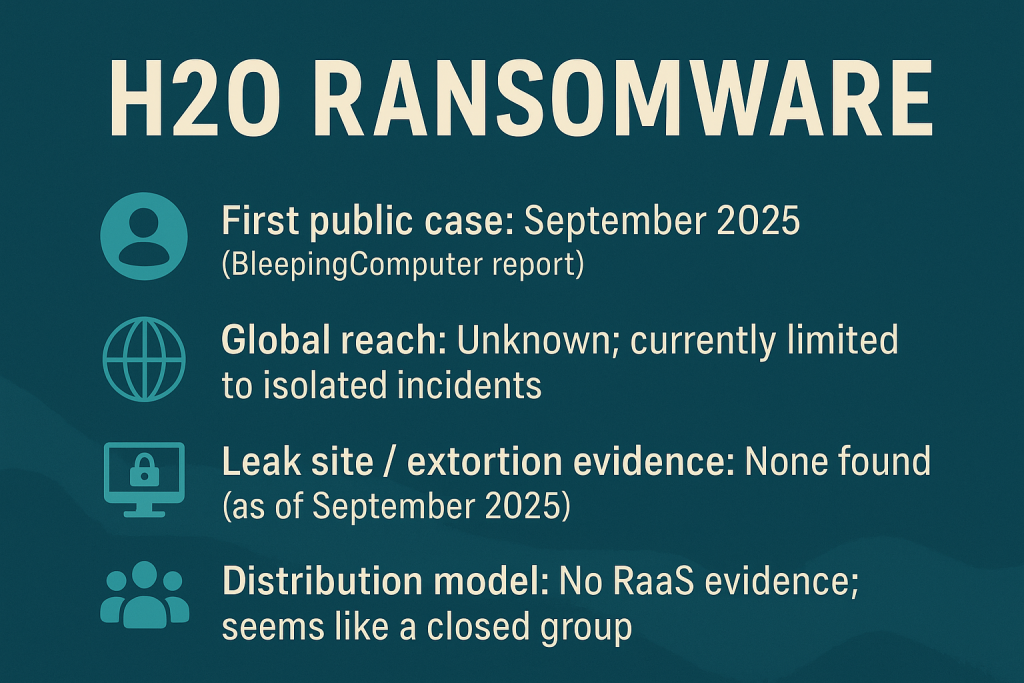
Key Facts and Current Statistics on H2OWATER
- First Publicly Reported Case: September 2025 (through BleepingComputer forum submissions).
- Victim Geography: Still unclear; only scattered incidents are known.
- Leak Site Activity: No associated data leak portal or extortion blog has been identified to date.
- Business Model: No signs of “Ransomware-as-a-Service” (RaaS). Instead, this appears to be a closed operation with direct attacker involvement.
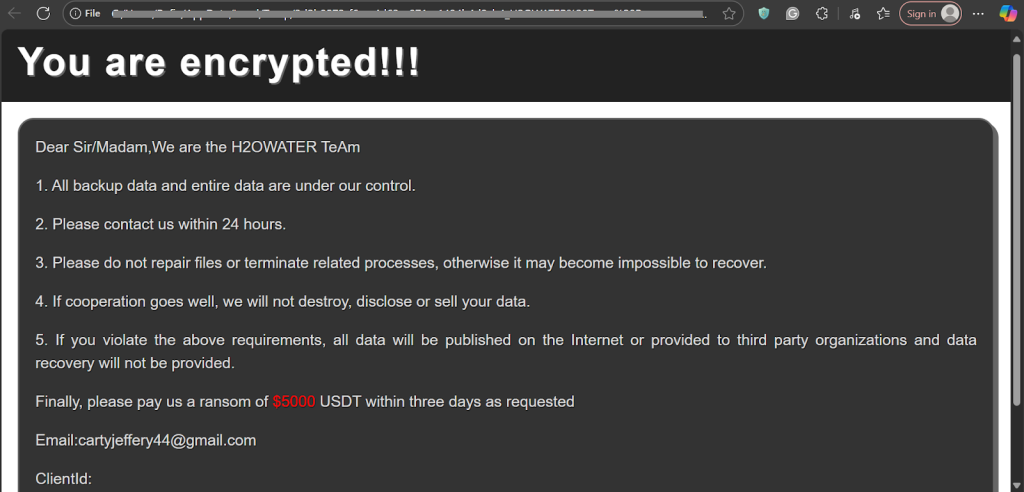
Examining the H2OWATER Ransom Note
While full ransom note samples remain scarce, reports indicate that its structure follows typical extortion templates. Based on shared fragments, it likely includes:
Dear Sir/Madam,We are the H2OWATER TeAm
1. All backup data and entire data are under our control.
2. Please contact us within 24 hours.
3. Please do not repair files or terminate related processes, otherwise it may become impossible to recover.
4. If cooperation goes well, we will not destroy, disclose or sell your data.
5. If you violate the above requirements, all data will be published on the Internet or provided to third party organizations and data recovery will not be provided.
Finally, please pay us a ransom of $5000 USDT within three days as requested
Email:[email protected]
ClientId:
VPMvKJ9hhsHEtXA1StanzGQUliPrhMDBLeUgosrnFvR2hJ+sHY0BsXZMWdXB/J++bxb/u5CLlM/Tr8I2Gz8ufz6PFFIvllTybqpNKNAcduAEcvvOpC9WIobo0qlOG26If5iHBmSeQddjLQ+4zcKdbGf9VH7Pg1cxgje5TyWP2YT8BowKFJLbuX8DeGQXlKUN9mWLV2bf/kYEG6st8EimHnLShjRB/6TIgjKRkqujW0PpbxcOcSNXMDuoJ124of+509ddDuRusjO09Ain++K9XiEGRb/9kVMaGopGitd2ORn5vFd3nrZuBBYl56XFY3qSt3wBUrVD/nJjn2ljB0O+3g==
Conclusion
H2OWATER ransomware is still in its infancy, but its use of robust encryption and stealthy no-extension strategy makes it dangerous. Since no public decryptor exists yet, prevention, early detection, and recovery planning are critical.
- Harden access to RDP/SSH and rotate credentials.
- Maintain immutable and offline backups.
- Preserve ransom notes and encrypted samples for future research.
- Engage professional ransomware response teams before attempting any decryption.
While attackers may demand payment, victims should weigh legal, financial, and ethical risks carefully. The best long-term defense is resilience—strong cyber hygiene, tested backups, and incident response readiness.
MedusaLocker Ransomware Versions We Decrypt