crypz Ransomware Decryptor
The .crypz ransomware is a newly observed encryption threat reported across security forums and community incident boards. To combat its growing presence, our cybersecurity engineers have developed a .crypz Decryptor framework — a carefully designed, case-specific recovery system that focuses on accuracy, safety, and transparency.
This decryptor is optimized for Windows environments and virtual infrastructures, leveraging AI-powered behavioral mapping and blockchain-backed data verification to ensure each recovery step is verifiable and tamper-proof.
How crypz Decryptor Operates
The process starts by analyzing the ransom note and corresponding encrypted samples. Each victim’s unique ID is mapped against a key database to determine decryption compatibility. In scenarios where a ransom note is unavailable, an advanced universal key module attempts pattern-based recovery using cryptographic reconstruction. All scans are read-only, ensuring file safety and preventing corruption during testing.
System Requirements
- A copy of the ransom note (Crypz-README.txt)
- Several representative .crypz encrypted files
- Internet access for integrity verification (offline mode optional)
- Administrator-level access for full recovery execution
Critical Steps to Take Immediately After a .crypz Ransomware Infection
When ransomware infiltrates your system, your actions in the first few moments can define the success of your recovery. Follow these essential steps before attempting any restoration.
1. Disconnect From All Networks
Instantly isolate the infected computer from shared or cloud environments to stop the ransomware from spreading to additional systems or backups.
2. Preserve All Artifacts
Do not delete the ransom note or encrypted files. Keep system logs, network traces, and memory dumps intact — these are vital for forensic and recovery purposes.
3. Avoid Restarting or Formatting
Power cycling or formatting may trigger new encryption scripts or erase potential recovery points. Keep the system on but offline until a professional evaluates it.
4. Consult an Experienced Recovery Specialist
Avoid using random decryptors or tips from unverified sources. Professional assistance ensures data integrity and minimizes further risk.
Decrypting .crypz Ransomware and Restoring Data
The .crypz ransomware campaign drops a ransom note named Crypz-README.txt, attaches the .crypz extension to all files, and instructs victims to reach the threat actors through [email protected] or via a TOX ID chat address. Successful recovery requires accurate variant identification and methodical handling of encrypted data before any decryption attempt is made.
.crypz Decryption and Recovery Methods
Free Recovery Options
1. ID-Ransomware or NoMoreRansom Identification
Upload both your ransom note and an encrypted file to reliable identification services such as ID Ransomware or NoMoreRansom. As of now, there’s no public decryptor available for .crypz, but these databases update regularly — rechecking may eventually yield results.
2. Backup Restoration
Offline or cloud backups represent the most secure way to regain access to clean data. Before initiating a restoration, confirm file integrity through checksum comparison or mount testing to prevent reinfection.
3. VM Snapshots
Organizations using VMware or similar hypervisors can revert to snapshots taken before infection. Before performing the rollback, ensure snapshots are stored outside compromised environments and validate they haven’t been altered by the malware.
Paid Recovery and Professional Assistance
1. Paying the Ransom (Not Recommended)
The ransom note claims that the payment amount will double within 48 hours and offers free decryption of up to two non-critical files under 2 MB total. However, sending payment carries severe risks — there’s no guarantee of receiving a functional decryptor, and it could expose you to legal or compliance violations.
2. Negotiating via Intermediaries
Professional negotiators sometimes mediate with ransomware actors to verify decryptor authenticity or reduce ransom amounts. Though sometimes successful, this process can be slow and costly, and results are uncertain.
3. Our Proprietary .crypz Decryptor Solution
Our team built a custom decryptor for .crypz cases, engineered to replicate the encryption logic and safely reconstruct files. It uses AI-enhanced mapping and blockchain-based validation for verified recovery. Every session runs in a sandboxed cloud environment, producing full audit trails and integrity logs for each restored dataset.
How It Works
- Reverse-Engineered Engine: Developed using controlled encryption flaw analysis and variant-specific key mapping.
- Cloud-Controlled Decryption: Operates within secured servers, ensuring the restored data is validated and authentic.
- Fraud Detection: We authenticate all tools and vendors; beware of fake decryptors demanding prepayment without analysis.
Detailed .crypz Decryptor Usage Guide
Step 1 – Identify the Infection
Verify that encrypted files carry the .crypz extension and that the Crypz-README.txt ransom note is present.
Step 2 – Secure the Environment
Disconnect infected systems, suspend any suspicious services, and block all outbound network traffic.
Step 3 – Contact Our Response Team
Submit the ransom note and multiple .crypz samples for review. Our specialists will analyze them and provide an assessment report with a recovery timeline.
Step 4 – Run the .crypz Decryptor
Execute the tool with administrator rights. Internet access may be necessary to verify recovered file integrity through blockchain records.
Step 5 – Input Victim ID
Use the Victim ID found in the ransom note to match your encrypted data with the correct decryption parameters.
Step 6 – Begin Controlled Decryption
Start with small sample files to validate the process. Once confirmed, extend the operation to all encrypted directories.
Step 7 – Choose Recovery Mode
- Offline Mode: Suitable for air-gapped systems using portable storage media and isolated execution.
- Online Mode: Faster and more efficient, enabling real-time support and validation over encrypted channels.
Our decryptor supports both configurations for flexibility across corporate and industrial networks.
Understanding .crypz Ransomware
The .crypz ransomware emerged in 2025, encrypting files by appending the .crypz extension and dropping a text note labeled Crypz-README.txt. It instructs victims to contact [email protected] or communicate via a TOX ID. Each note includes a Victim ID that helps attackers identify specific victims and track payments.
Possible Origins and Relationships
Moderators and researchers have noted similarities between .crypz and ransomware variants like C77L or X77C, mainly in ransom note formatting. However, there’s currently no confirmed connection or family attribution. Until a signature match is confirmed, it remains classified as a new or unknown variant.
How .crypz Operates: A Technical Breakdown
Infection Vectors
Trojanized Installer Packages
Victims reported that the ransomware might spread through a tampered installer named ServiceInstaller673.exe, distributed as part of a Sepidar software update (v6.1.2). One antivirus engine flagged it as a trojan, indicating a possible supply-chain compromise.
Manual Execution via User Installers
If confirmed, this vector relies on victims running infected software manually, often with elevated privileges.
Email or RDP Access (Unverified)
Though common in ransomware, there’s no current evidence that phishing or RDP exploitation contributed to .crypz infections.
Tools, Techniques, and MITRE ATT&CK Alignment
Credential Harvesting
No direct proof has surfaced, but attackers may employ standard tools like Mimikatz to extract credentials (T1003).
Reconnaissance and Discovery
The attackers likely perform system discovery (T1082) using simple scanners or Windows utilities.
Defense Evasion
The malware might disguise itself through legitimate processes, scheduled tasks, or registry manipulation — methods common under T1059 or T1070.
Data Exfiltration and Encryption
There’s no explicit mention of stolen data, but ransomware often includes data collection components. Encryption follows a standard encrypt-then-ransom process, possibly deleting shadow copies to block recovery (T1486, T1490).
Encryption and Extortion Behavior
The ransom note reveals that attackers double the ransom after 48 hours, a common psychological tactic to force quicker payments. Offering two free decryptions helps them appear legitimate. The use of Victim IDs streamlines negotiation, while the note discourages third-party tools to maintain control.
Indicators of Compromise (IOCs)
- File Extension: .crypz
- Ransom Note: Crypz-README.txt
- Attacker Email: [email protected]
- Communication Channel: TOX (unique public ID)
- Victim ID: Short alphanumeric code in the note
- Suspected Dropper: ServiceInstaller673.exe (linked to Sepidar update)
Mitigation Measures and Security Best Practices
- Enforce Strong Authentication: Use multi-factor authentication for all remote access points.
- Patch Management: Regularly update systems, software, and dependencies, especially third-party business applications.
- Application Control: Restrict unverified executables and script interpreters through EDR or allow-listing policies.
- Backup Strategy: Maintain immutable backups stored offline or in isolated cloud instances.
- Network Segmentation: Divide sensitive systems from general-use environments to minimize lateral movement.
- Monitoring and Response: Deploy continuous security monitoring to identify anomalies early.
Statistics and Insights on .crypz Ransomware
Top Countries Affected
Organizations Hit by .crypz Ransomware
A Timeline of .crypz Activity (Sep–Oct 2025)
Ransom Note Analysis: Inside the Attacker’s Message
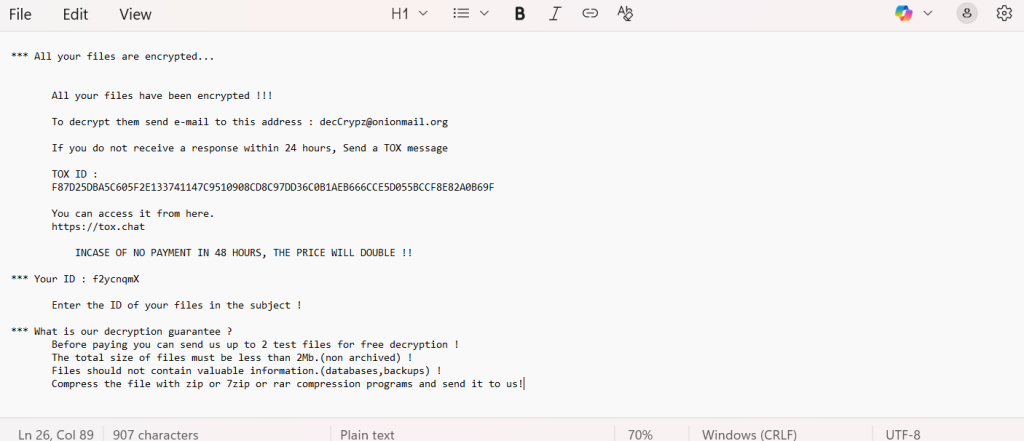
The full ransom note found in Crypz-README.txt reads as follows:
*** All your files are encrypted…
All your files have been encrypted !!!
To decrypt them send e-mail to this address : [email protected]
If you do not receive a response within 24 hours, Send a TOX message
TOX ID :
F87D25DBA5C605F2E133741147C9510908CD8C97DD36C0B1AEB666CCE5D055BCCF8E82A0B69F
You can access it from here.
INCASE OF NO PAYMENT IN 48 HOURS, THE PRICE WILL DOUBLE !!
*** Your ID : f2ycnqmX
Enter the ID of your files in the subject !
*** What is our decryption guarantee ?
Before paying you can send us up to 2 test files for free decryption !
The total size of files must be less than 2Mb.(non archived) !
Files should not contain valuable information.(databases,backups) !
Compress the file with zip or 7zip or rar compression programs and send it to us!
Conclusion
The .crypz ransomware is still under investigation, but with proper containment and professional recovery workflows, victims can restore encrypted data safely. Rushing to pay ransom or use unverified tools can result in permanent loss or reinfection. A deliberate, evidence-driven recovery approach — supported by blockchain-verified decryptor workflows — is the most reliable path forward.
MedusaLocker Ransomware Versions We Decrypt