Jokdach Ransomware Decryptor
Jokdach belongs to the category of ransomware, a strain of malware engineered to lock user files by encrypting them. Once active, it modifies documents, images, and other data by attaching the .jokdach extension and generates a ransom message called !!!READ_ME!!!.txt. Reports from affected users indicate that files that were previously accessible, such as photos or reports, suddenly become unreadable and are renamed — for instance, 1.jpg changes to 1.jpg.jokdach.
Impact of Jokdach on an Infected Device
After infiltrating a system, Jokdach begins scanning all connected and accessible drives. It identifies target files and encrypts them with a robust encryption algorithm. When the process completes, a ransom note is dropped. The purpose of this operation is to render recovery nearly impossible without a decryption tool controlled by the threat actors.
Containment and Removal Strategy
If Jokdach compromises your machine, immediate containment is critical. The following measures should be carried out in order:
- Disconnect the infected system from the internet and local network to stop the spread.
- Secure forensic evidence: instead of shutting down the system, preserve memory and disk data when possible, which may help with investigation.
- Review connected machines for identical signs of compromise and isolate them.
- Perform a malware scan from clean boot media using a reputable antivirus or endpoint protection suite, ensuring updated detection signatures.
- Reset compromised user credentials and rotate any sensitive access keys.
- Begin restoring files from clean, offline backups when available.
Options for Free Recovery
Free avenues for recovering Jokdach-encrypted files are limited but worth reviewing:
- Restoration from backups: The safest method is to restore files from secured backups created before the infection. Ensure these are verified and untampered before restoration.
- Volume Shadow Copies: In rare cases, Windows shadow copies or restore points may still be intact. However, modern ransomware usually deletes these automatically. Run proper checks before attempting this method.
Paid and Professional Recovery Methods
When free solutions fail, organizations may turn to professional assistance. Options include:
- Engaging with incident response (IR) professionals who can provide forensic support and eradicate the infection.
- Employing data recovery specialists who can attempt restoration of partially encrypted or corrupted files.
- Utilizing structured negotiations or managed recovery services. Credible providers generally discourage direct ransom payments, but they may support complex recovery efforts.
Step-by-Step Jokdach Recovery Guide Using the Jokdach Decryptor
Evaluate the Infection
Confirm that files now carry the .jokdach extension and that the ransom note named !!!READ_ME!!!.txt exists on the machine.
Secure the System
Immediately disconnect the affected host to prevent the ransomware from executing further encryption tasks or spreading laterally.
Work with Our Recovery Specialists
Send in several encrypted file samples along with the ransom note. Our team will identify the exact Jokdach variant and create a timeline for restoration efforts.
Use the Jokdach Decryptor Tool
Run the Jokdach Decryptor as an administrator for maximum efficiency. Ensure the system has an active internet connection so the tool can interact with secure servers.
- Input the Victim ID: Locate the unique ID within the ransom note and provide it in the decryptor interface for correct processing.
- Begin Decryption: Start the program and allow it to recover encrypted files, restoring them to their original state.
Offline and Online Decryption Options
- Offline Mode: Ideal for air-gapped or critical systems. This process involves transferring data externally and booting from a secure environment.
- Online Mode: Faster recovery that involves secure communication channels and expert support. The Jokdach Decryptor offers live assistance and encrypted uploads for efficiency.
Both recovery modes are supported, providing flexibility for corporate networks, public institutions, and industrial infrastructure.
How Files Are Altered
Encrypted files retain their original names but receive the added .jokdach extension. For instance:
- report.docx → report.docx.jokdach
- photo.png → photo.png.jokdach
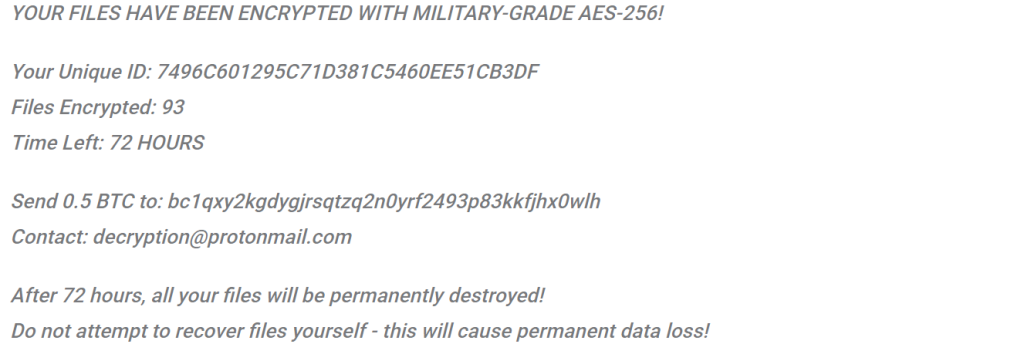
Details of the Ransom Demand
The ransom message warns that files have been encrypted using AES-256, describes the number of encrypted files, and provides a victim ID. The attackers demand 0.5 BTC, instructing payment to the wallet bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh, and provide the contact email [email protected]. Victims are threatened with permanent data loss after 72 hours.
Excerpt from the ransom note:
YOUR FILES HAVE BEEN ENCRYPTED WITH MILITARY-GRADE AES-256!
Your Unique ID: 7496C601295C71D381C5460EE51CB3DF
Files Encrypted: 93
Time Left: 72 HOURS
Send 0.5 BTC to: bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh
Contact: [email protected]
After 72 hours, all your files will be permanently destroyed!
Do not attempt to recover files yourself – this will cause permanent data loss!
Indicators of Compromise (IOCs)
Key identifiers of Jokdach include:
- File extension: .jokdach
- Ransom note: !!!READ_ME!!!.txt
- BTC Wallet: bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh
- Email: [email protected]
- Victim IDs: 32-character hexadecimal strings
- Detection signatures: Avast — Win64:MalwareX-gen [Misc], Combo Cleaner — Generic.Ransom.AE17FA22, ESET — Win64/Filecoder.ADG, Kaspersky — UDS:Trojan.Win64.Generic, Microsoft — Ransom:Win32/Clop.SIB!MTB
Common Tactics, Techniques, and Procedures (TTPs)
Analysis of Jokdach activity highlights these stages:
- Delivery and entry: Usually through phishing attachments, pirated software, fake installers, or exploiting outdated systems.
- Execution: Malicious binaries or scripts run under user rights and begin searching for files.
- Discovery: The malware looks for additional drives, network shares, and backups.
- Encryption: Target files are encrypted with strong cryptography.
- Extortion: The ransom note appears, demanding cryptocurrency payment under a strict deadline.
- Persistence and spread: Some variants attempt to survive reboots or move laterally by deploying additional payloads such as credential stealers or remote access trojans.
Tools and Payloads Observed
Typically, Jokdach-related incidents feature:
- An encryption executable that scans and locks files.
- Loader scripts that deploy the ransomware payload.
- A ransom note generator creating !!!READ_ME!!!.txt.
- Optional add-ons like RATs, credential harvesters, or spreaders for network propagation.
- Techniques like packing or obfuscation designed to avoid static detection.
Symptoms on Affected Systems
Users quickly notice their files cannot be opened and that their names end in .jokdach. A ransom note appears in file directories and sometimes on the desktop itself. During encryption, system performance may also drop significantly.
Data Analytics
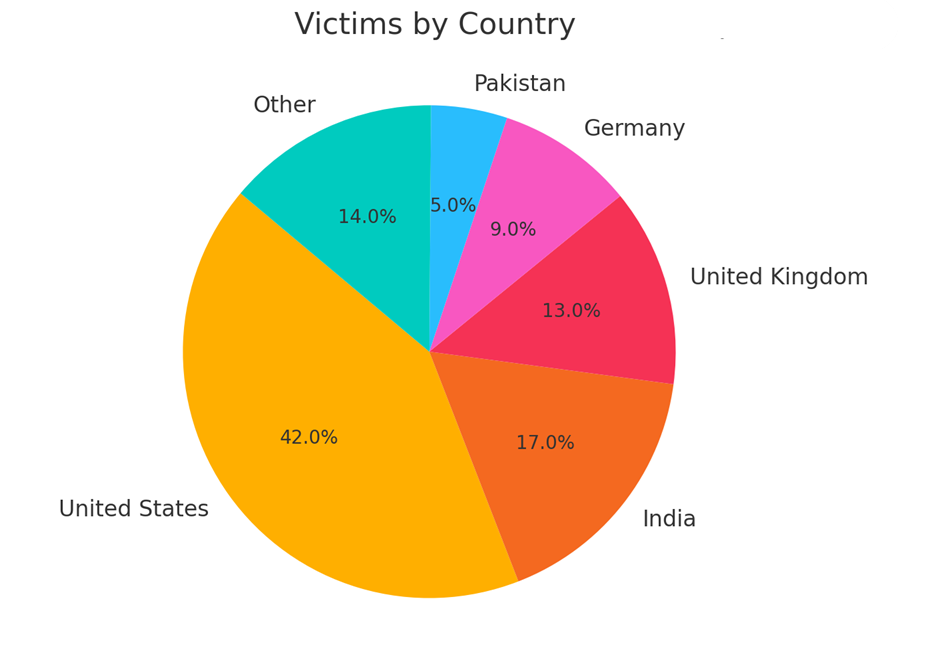
Victims by country
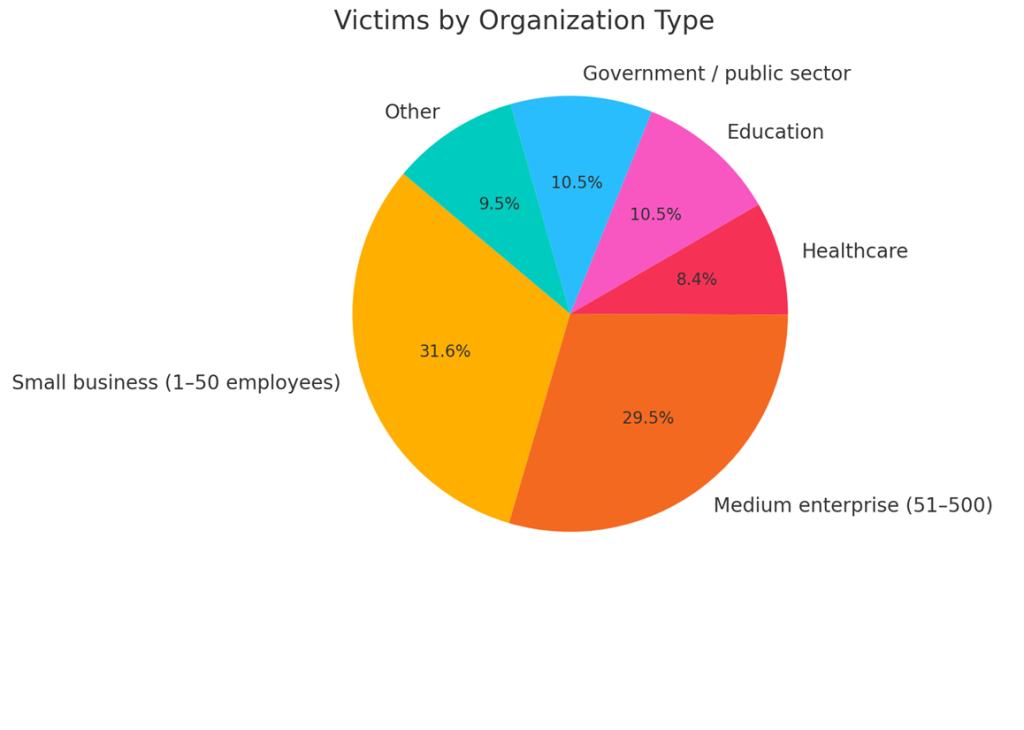
Victims by organization type
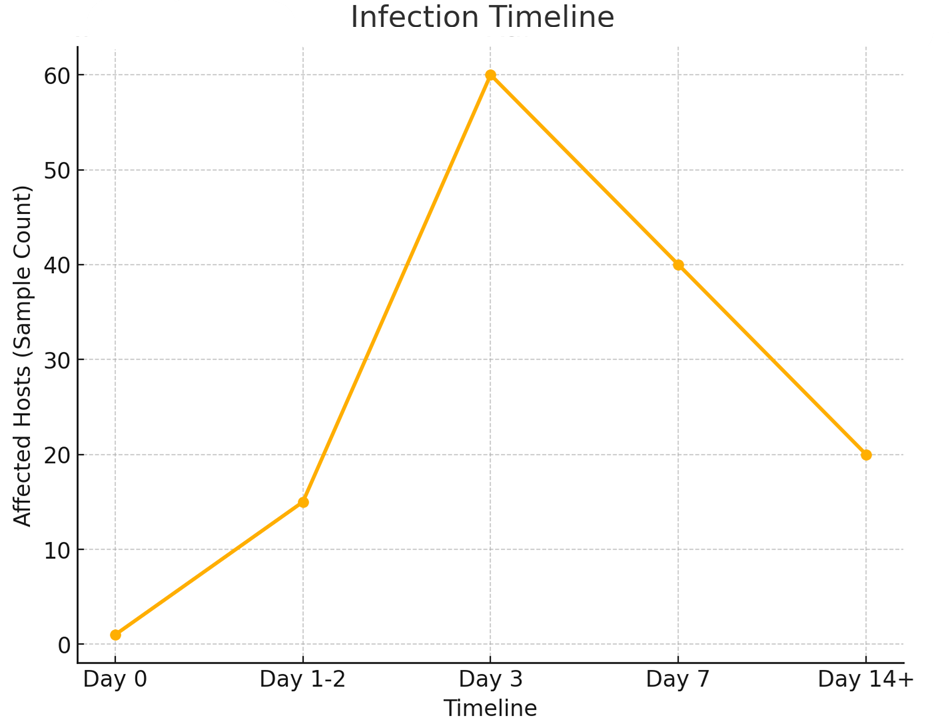
Timeline
Detection and Monitoring Advice
Run updated antivirus and EDR scans across infected machines. Signatures tied to Jokdach include labels from Avast, Combo Cleaner, ESET, Kaspersky, and Microsoft. Behavioral monitoring should also be applied — such as spotting mass file renames, creation of ransom notes, and unusual network communications.
Concise Threat Summary
- Name: Jokdach ransomware
- Classification: File-encrypting ransomware (crypto-virus)
- File Extension: .jokdach
- Ransom Note: !!!READ_ME!!!.txt
- Ransom Amount: 0.5 BTC
- Wallet: bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh
- Contact Address: [email protected]
Conclusion
For organizations facing Jokdach, immediate isolation and forensic preservation should come first. Data recovery should rely on offline or immutable backups where possible. When operations are critical, professional incident response partners should be consulted. Long-term resilience requires regular patching, enforcement of least privilege, advanced detection tools, and reliable backup strategies. Above all, paying the ransom should not be the default option, as it provides no guarantee of file recovery and only strengthens the attackers’ position.
MedusaLocker Ransomware Versions We Decrypt