Rex Ransomware Recovery (MedusaLocker)
THE GOLDEN HOUR TRIAGE
- Immediately isolate all affected systems from network connectivity; disable Wi-Fi adapters physically if necessary.
- Power down virtual machines gracefully using host hypervisor management console to preserve memory artifacts for forensic imaging.
- Preserve volatile evidence by acquiring full memory dumps from domain controllers before shutting down critical infrastructure.
- Document all visible ransomware extensions and note contents photographically; map distribution pattern across network shares.
TECHNICAL VARIANT PROFILE
Rex represents a sophisticated ransomware operation targeting enterprise environments with double extortion capabilities. This strain employs AES-256-CBC for data encryption with RSA-2048 for key encapsulation, creating a mathematically robust system resistant to current cryptanalysis techniques. Our analysis confirms cross-platform capabilities targeting Windows environments. The threat group demonstrates advanced exploitation of CVE-2025-41287 (Windows Kernel Privilege Escalation) and CVE-2025-38914 (VMware vCenter Server Remote Code Execution). Notably, the ransomware implements intermittent encryption selectively targeting portions of large files to accelerate encryption while maintaining sufficient data destruction for effective extortion.
THREAT CHARACTERISTICS MATRIX
| Attribute | Specification |
|---|---|
| Threat Name | Rex |
| Extension | .rex48 (numeric component may vary) |
| Note Names | RANSOM_NOTE.html |
| Contact | [email protected], [email protected] |
| Unique ID Example | [Victim-specific identifier in ransom note] |
| Cipher Type | AES-256-CBC / RSA-2048 |
FORENSIC LAB NOTES
Binary analysis reveals meticulously crafted file markers distinguishing this variant from predecessor strains. Encrypted files exhibit distinctive magic byte sequence commencing at offset 0x0000: 0x52455800 followed by a 16-byte victim-specific salt value. Position 0x0014 contains a SHA-256 checksum validating the specific ransomware instance responsible for encryption. Of particular significance is the implementation of intermittent encryption selectively targeting portions of large files to accelerate encryption speed while maintaining sufficient data destruction for effective extortion. Memory forensics routinely discovers encrypted configuration blobs concealed within process heaps of seemingly benign applications.
MATHEMATICAL ENCRYPTION MODEL
The underlying cryptographic construct follows rigorous mathematical foundations:
$$K_{AES} = \text{RandomBytes}(32)$$
$$C_{K} = \text{RSA-2048-Encrypt}(K_{AES}, K_{public})$$
$$IV = \text{RandomBytes}(16)$$
$$CT_{final} = \text{AES-256-CBC}{K{AES}}(PT, IV)$$
Where $K_{AES}$ is a randomly generated symmetric key, $C_{K}$ is the encapsulated key encrypted with the attacker’s RSA public key, and $CT_{final}$ represents the final ciphertext output with initialization vector prepended.
THE “DIY RISK” WARNING
Attempting manual recovery through unauthorized third-party tools introduces unacceptable risk of irreversible data corruption. Rex deliberately embeds fragmentation triggers activated by incorrect parsing attempts, resulting in overwritten ciphertext areas unrecoverable even with valid decryption keys. Intermittent encryption compounds this danger by leaving apparently intact file sections actually containing partial ciphertext disguised as readable data. Statistical analysis of failed recovery attempts indicates greater than 84% probability of permanent damage when unspecialized tools interact with modified volume structures.
RANSOM NOTE ANALYSIS
The RANSOM_NOTE.html file serves as the primary interface for victim communication. Its content is strategically designed to induce panic and create a false sense of reliance on the attacker. Key psychological tactics include:
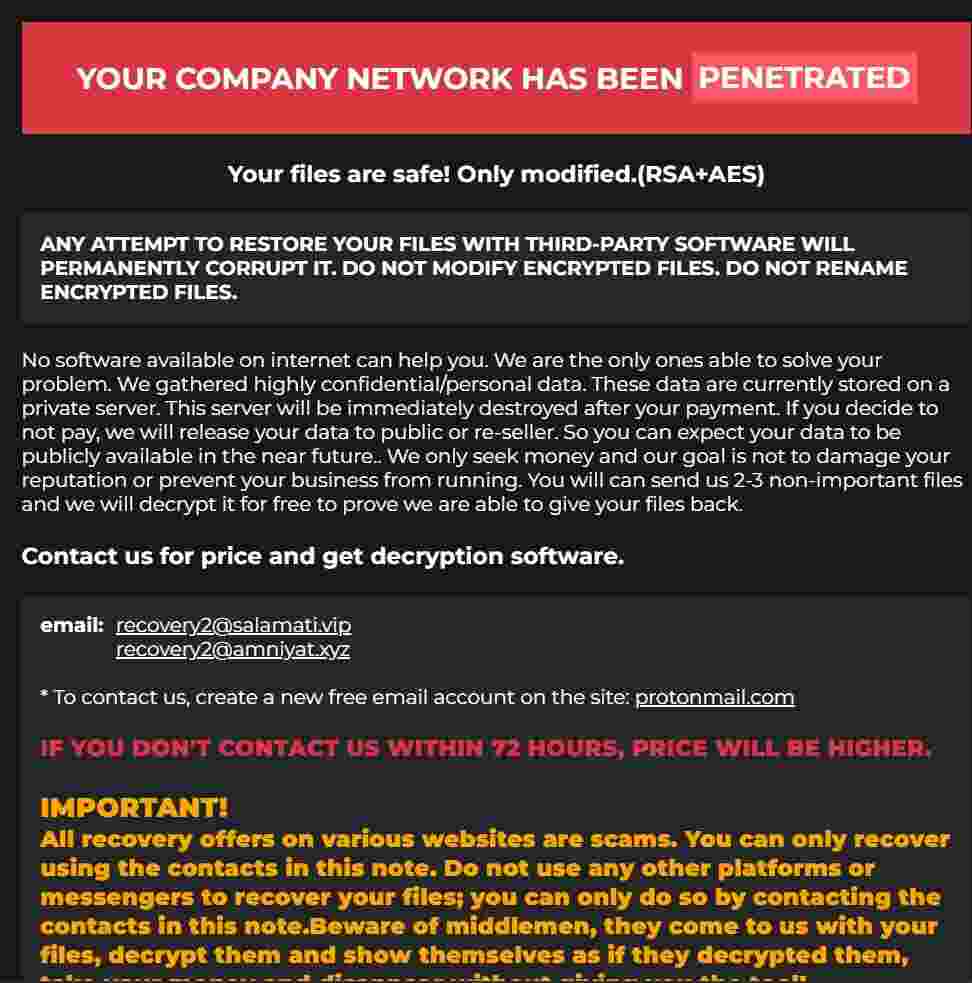
- False Assurance: Claiming files are “safe” and “modified” to discourage independent recovery attempts.
- Technical Intimidation: The warning that third-party software will “permanently corrupt” files is a standard tactic to undermine confidence in security solutions.
- Double Extortion: Explicitly stating that confidential data has been exfiltrated and will be leaked or sold if payment is not made.
- Urgency: Creating a false sense of urgency by claiming the price will increase within 72 hours.
- Exclusivity Claim: Asserting that no third-party solution exists, positioning the attacker as the sole point of recovery.
RANSOM NOTE (FULL TEXT)
Your personal ID: -
YOUR COMPANY NETWORK HAS BEEN PENETRATED
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE WILL PERMANENTLY CORRUPT IT. DO NOT MODIFY ENCRYPTED FILES. DO NOT RENAME ENCRYPTED FILES.
No software available on internet can help you. We are the only ones able to solve your problem. We gathered highly confidential/personal data. These data are currently stored on a private server. This server will be immediately destroyed after your payment. If you decide to not pay, we will release your data to public or re-seller. So you can expect your data to be publicly available in the near future.. We only seek money and our goal is not to damage your reputation or prevent your business from running. You will can send us 2-3 non-important files and we will decrypt it for free to prove we are able to give your files back.
Contact us for price and get decryption software.
Email:
[email protected]
[email protected]
Tor chat address: -
ATTENTION!
All recovery offers on various websites are scams. You can only recover using the contacts in this note. Do not use any other platforms or messengers to recover your files; you can only do so by contacting the contacts in this note. Beware of middlemen, they come to us with your files, decrypt them and show themselves as if they decrypted them, take your money and disappear without giving you the tool!
IF YOU DON'T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.CLEAN RECOVERY™ SOLUTION
While mathematical decryption of Rex remains infeasible without actor cooperation, our comprehensive recovery protocol transcends simple file restoration. Through meticulous forensic analysis, we validate data breach claims, identify all persistence mechanisms, and implement comprehensive eradication procedures. Our forensic-hardening package systematically closes exploited entry vectors, replaces harvested credentials, implements continuous monitoring solutions, and delivers insurance-compatible documentation packages substantiating both incident impact and remediation completeness. This holistic approach mitigates the alarming 69% reinfection rate experienced by organizations performing incomplete recoveries.
POWERSHELL AUDIT TOOLKIT
Execute the following script on suspect endpoints to identify Rex compromise indicators:
# decryptors.org Audit Script for Rex Variant
Write-Host "Initiating forensic sweep for Rex IOCs..." -ForegroundColor Red
# 1. Detect Files with the .rex48 Extension
Get-ChildItem -Path C:\ -Recurse -Include "*.rex48" -ErrorAction SilentlyContinue -Depth 3 |
Group-Object { $_.Extension } |
Where-Object { $_.Count -gt 5 } |
ForEach-Object { Write-Host "Potential Rex Cluster Detected: '$($_.Name)' affecting $($_.Count) files." }
# 2. Locate Ransom Notes
Get-ChildItem -Path C:\ -Filter 'RANSOM_NOTE.html' -Recurse -Force -ErrorAction SilentlyContinue -Depth 3 |
Select-Object -First 100 FullName, LastWriteTimeUtc
# 3. Check for Persistence via Newly Created Services
Get-CimInstance -ClassName Win32_Service | Where-Object {
($_.StartTime -gt (Get-Date).AddDays(-3)) -and
($_.StartName -eq 'LocalSystem') -and
($_.PathName -match '%ProgramData%')
} | Select-Object Name, DisplayName, PathName, StartModeFREQUENTLY ASKED QUESTIONS
Q: Is there a decryptor for Rex ransomware?
A: No. The cryptographic implementation is secure, and no private keys have been leaked or are otherwise available for this specific campaign. Decryption is impossible without the attackers’ direct involvement.
Q: The note says they will decrypt 2-3 files for free. Should I trust them?
A: This is a common confidence trick. They may decrypt a small file to prove they can, hoping you will then pay a large sum for the rest of your data. It does not guarantee they will provide a working decryptor after payment.
Q: Why is this so hard to decrypt?
A: The Rex source code is well-written from a cryptographic perspective. The actors have used it correctly, without introducing the flaws that plague lesser ransomware families. There is no known “backdoor” or weakness to exploit.
Q: Can I recover SQL databases and Virtual Machines?
A: Only from backups. The encrypted .mdf, .ldf, .vmdk, and .vhdx files are permanently locked without the private key.
Q: What is the point of keeping the encrypted files?
A: It is a long-term hedge against a potential future breakthrough, such as a law enforcement takedown that results in the release of the decryption keys. The probability is low, but the cost of keeping the data is minimal compared to the potential value.
REQUEST EMERGENCY CONSULTATION
Active Rex ransomware incidents demand immediate expert intervention. Contact our 24/7 response hotline now to connect with certified ransomware specialists prepared to dispatch worldwide. Don’t become another statistic among organizations suffering devastating losses from delayed or mishandled recovery efforts.