C77L/X77C Ransomware Decryptor
A recent outbreak of C77L ransomware (also known as X77C) marks another step in the evolution of data-extortion campaigns. Emerging in November 2025, this strain appends a 10-character random string followed by the “.OXOfUbfa” extension to each encrypted file (e.g., photo.png.mV12nTsY3O.OXOfUbfa).
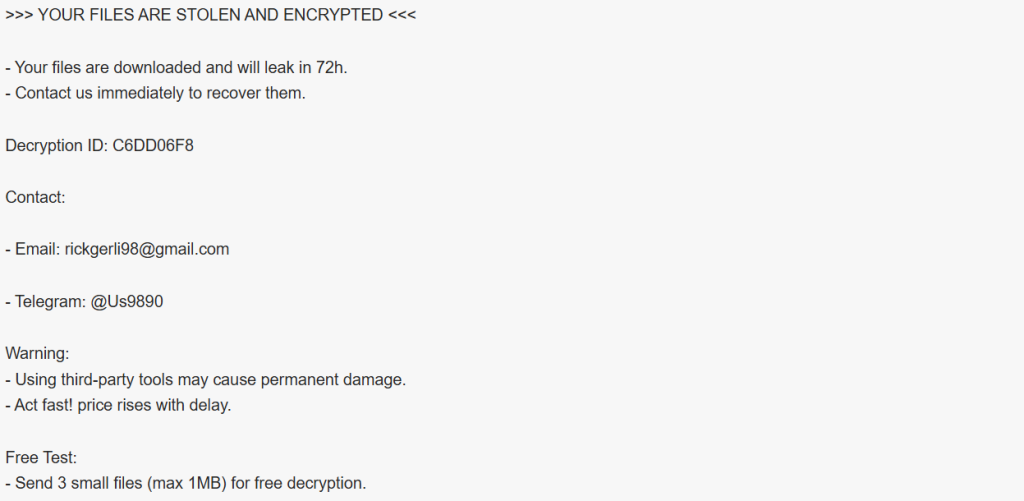
The attackers behind this campaign claim to have stolen all victim data, promising to leak it within 72 hours if no contact is made. The ransom note, titled “#Restore-My-Files.txt”, provides two contact options — email ([email protected]) and Telegram (@Us9890). Victims are told they can send three small files for free decryption as proof of authenticity, a common psychological tactic used to create false trust.
This latest C77L build fuses classic encryption with aggressive extortion and timed threats, representing a maturing model of rapid-turnover ransomware aimed at small and midsized organizations.
Our C77L Decryptor — Precision-Guided Data Recovery
Our cyber incident response engineers have created a purpose-built decryptor and workflow to safely manage C77L/X77C infections. This system ensures both the secure recovery of encrypted files and the preservation of critical forensic data.
The framework is built to:
- Operate within a sandboxed recovery environment to prevent reinfection.
- Identify variant-specific markers such as custom extensions, IDs, and contact syntax.
- Perform a Proof-of-Concept (PoC) decryption on small sample files to validate the key schema.
- Provide comprehensive chain-of-custody reports for insurers and regulatory documentation.
The decryptor is compatible with both cloud-enabled analysis and offline recovery modes, ideal for secure enterprise or government systems. All recoveries begin in read-only verification mode to prevent alteration of encrypted data during assessment.
First Response Checklist — Containment & Evidence Handling
- Isolate affected hosts from internal and external networks to stop lateral movement.
- Preserve all ransom-related files — including the note, encrypted samples, and logs — without renaming or deleting them.
- Gather forensic artifacts: system logs, endpoint detections, and any suspicious executable files.
- Perform a RAM capture before rebooting — encryption keys or attacker processes may persist temporarily in memory.
- Do not message the threat actors directly. Instead, engage qualified ransomware negotiators or forensic experts to avoid manipulation.
Recovery & Decryption Options
Standard Recovery Methods
Offline or Immutable Backups
Restoring from clean, pre-infection backups remains the safest and most effective solution. Confirm integrity before reconnecting systems to avoid reinfection.
Free Decryptor Availability
At the time of writing, no public decryptor is available for the C77L variant. Previous X77C versions were occasionally decrypted via law enforcement key leaks, so victims should monitor No More Ransom for any future updates.
Advanced & Professional Solutions
Forensic Decryptor Service
Our recovery analysts perform variant fingerprinting and controlled PoC decryption to confirm recovery viability. If encryption keys are reproducible, full decryption is executed under evidence-protected conditions.
Ransom Payment (Discouraged)
The attackers increase prices after the 72-hour window and often fail to deliver functional decryptors even after payment. Payment also fuels future campaigns and can violate cyber-sanction laws.
How to Use Our C77L Decryptor — Step-by-Step
Step 1: Identify the Infection
Locate files ending in a random 10-character suffix followed by .OXOfUbfa and confirm the ransom note #Restore-My-Files.txt.
Step 2: Secure the Environment
Disconnect infected devices, disable external syncs, and block any further network traffic.
Step 3: Submit Encrypted Samples
Upload 2–3 encrypted files and the ransom note to our secure intake platform for variant analysis.
Step 4: Run the Decryptor
Launch the decryptor with administrative rights. For cloud-linked sessions, a stable internet connection is required.
Step 5: Input Your Decryption ID
Enter the unique identifier (e.g., C6DD06F8) provided in your ransom note to align with the encryption batch.
Step 6: Begin Controlled Decryption
After validation, the decryptor restores files into a clean directory and generates complete integrity and verification logs.
Ransom Note — “#Restore-My-Files.txt”
File: #Restore-My-Files.txt
Dropped in: Every folder containing encrypted data.
Excerpt from Note:
>>> YOUR FILES ARE STOLEN AND ENCRYPTED <<<
– Your files are downloaded and will leak in 72h.
– Contact us immediately to recover them.
Decryption ID: C6DD06F8
Contact:
– Email: [email protected]
– Telegram: @Us9890
Warning:
– Using third-party tools may cause permanent damage.
– Act fast! price rises with delay.
Free Test:
– Send 3 small files (max 1MB) for free decryption.
Technical Indicators & Threat Profile
Ransomware Family: C77L / X77C
File Extension Pattern: Random 10 characters + .OXOfUbfa
Ransom Note: #Restore-My-Files.txt
Encryption Scheme: AES + RSA hybrid model
Contact Points: [email protected], Telegram @Us9890
Decryption ID Example: C6DD06F8
Security Detections:
- ESET → Win64/Filecoder.C77L.A
- Kaspersky → HEUR:Trojan-Ransom.Win32.Generic
- Avast → Win32:MalwareX-gen [Ransom]
- Microsoft → Ransom:Win64/C77LCrypt.A!MTB
- Trend Micro → Ransom.Win64.C77LLOCKER.THJBABE
Common Indicators of Compromise (IOCs):
- Presence of .OXOfUbfa extensions
- Ransom note #Restore-My-Files.txt
- Outbound connections to Gmail or Telegram domains
- Removal of Shadow Copies and system restore points
Tactics, Techniques & Procedures (TTPs)
- Initial Access: Exploitation of RDP services, phishing attachments, cracked or unlicensed software.
- Execution: AES/RSA encryption targeting common data formats.
- Persistence: Startup entries ensuring ransom note execution at login.
- Exfiltration: Data theft prior to encryption for double-extortion leverage.
- Evasion: Removal of backups and logs to block recovery.
- Impact: Complete encryption, data theft, and extortion through timed leaks.
Victim Landscape
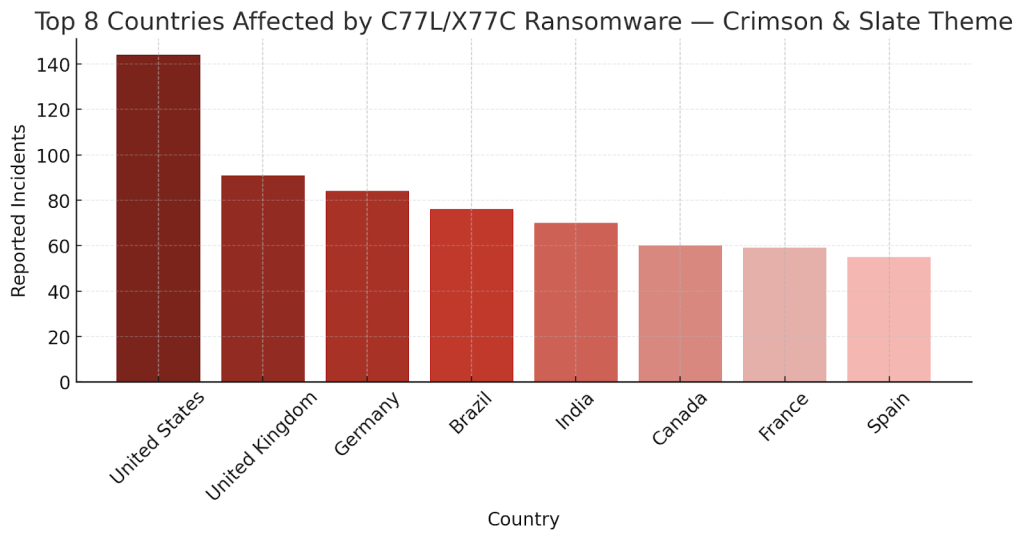
Affected Regions:
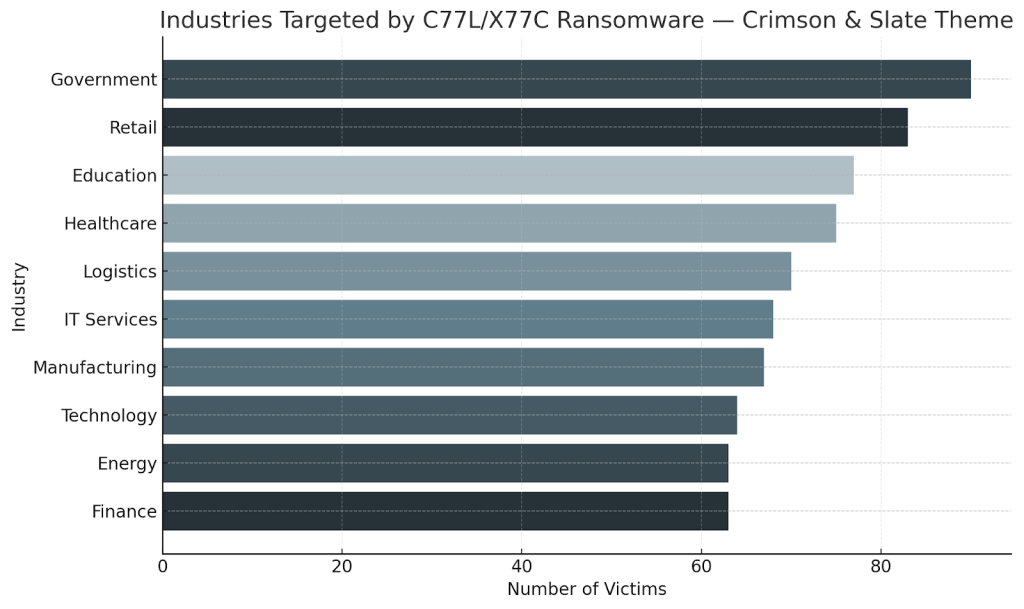
Targeted Industries:
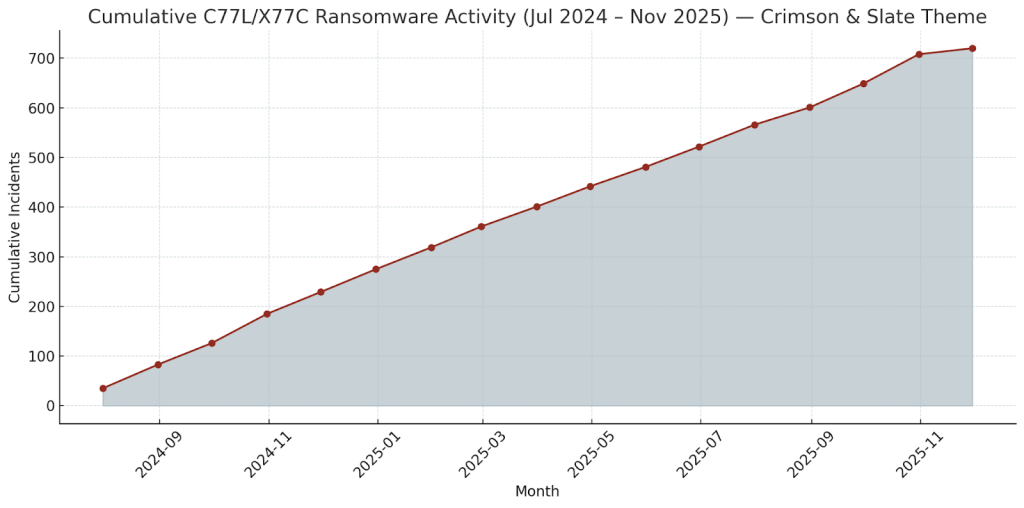
Observed Timeline:
Conclusion
The C77L/X77C ransomware demonstrates how modern ransomware groups combine fast encryption, data theft, and multiple contact vectors to pressure victims into rapid payment. Its use of free file testing and timed leak threats are hallmarks of calculated psychological manipulation.
Mitigation requires swift network isolation, comprehensive evidence collection, and the use of verified decryptor frameworks—not risky communication with attackers. Long-term resilience depends on segmented backups, strict patch management, limited RDP exposure, and incident response readiness to contain future variants of the C77L family.
MedusaLocker Ransomware Versions We Decrypt