Lamia Loader Ransomware Decryptor
Lamia Loader is a dangerous form of ransomware engineered to encrypt valuable files on compromised systems and demand payment for their restoration. Once deployed, it renames files by appending the extension “.enc.LamiaLoader” and drops a ransom message instructing the victim to transfer cryptocurrency in return for decryption.
Post-Infection Behavior
During controlled analysis in a lab environment, Lamia Loader was observed encrypting multiple file formats and renaming them. For example, a file originally called “image.jpg” was converted into “image.jpg.enc.LamiaLoader,” while “notes.png” was changed into “notes.png.enc.LamiaLoader.” After finishing its encryption process, the malware generated a ransom note titled “LamiaLoader.txt” inside affected folders.
Urgent Response Checklist
When dealing with an active Lamia Loader infection, immediate containment is critical. Security teams and individuals should:
- Isolate the infected endpoint from the network and disconnect any removable storage.
- Preserve the ransom note and save at least one encrypted sample file separately for investigation.
- Generate a forensic image of the affected drive and only work from copies.
- Confirm the ransomware family via ID Ransomware or vendor identification services.
- Perform a comprehensive antivirus scan (such as with Combo Cleaner) to eliminate the live malware before testing decryption attempts.
Data Recovery Strategies for Lamia Loader (.enc.LamiaLoader)
Free Recovery Options – First Steps
The most reliable free option is restoring files from backups created before the compromise, provided they were stored offline or in an isolated cloud account. If such backups do not exist, check for Windows Volume Shadow Copies — these system snapshots can sometimes restore earlier file versions, but many ransomware variants attempt to delete them.
Vendor Decryptor Repositories – Where to Look
Victims should always check trusted repositories before exploring paid services. Platforms such as No More Ransom, Avast, Kaspersky, and Emsisoft periodically release free decryptors for known ransomware families. Before using any tool, confirm the ransomware type by submitting a ransom note and encrypted file to ID Ransomware or equivalent vendor services.
Confirming the Variant – Why It Matters
Accurate identification of the ransomware is mandatory to prevent errors during decryption. Using the wrong decryptor could damage encrypted files permanently. To avoid this, submit both the ransom note and at least one encrypted file to online services like ID Ransomware for verification.
Leveraging Shadow Copies, Cloud Storage, and Restore Points
If Lamia Loader failed to delete shadow copies, the Windows Previous Versions feature or tools like ShadowExplorer may assist in recovering files. Cloud storage services such as Google Drive and OneDrive often keep older file versions, which can be restored directly. Although System Restore cannot bring back encrypted documents, it may help roll back certain system changes.
File Recovery Utilities – Partial Results Expected
Utilities like Recuva, PhotoRec, or other commercial recovery programs may be able to restore files that were deleted during the ransomware’s execution. However, they cannot decrypt locked files. Recovery with these tools is unpredictable and should always be performed on an image copy of the original drive to avoid further damage.
Paid Recovery Options – Alternatives to Paying Threat Actors
Why Direct Payment is Risky
The ransom demand, set at 500 EUR in Monero (XMR), does not guarantee results. Many victims have paid attackers only to receive no functional decryptor in return. Beyond the risk of losing money, payment also funds further cybercrime operations. Security professionals and law enforcement universally discourage meeting ransom demands.
Professional Forensic & Recovery Assistance
A safer path is hiring a professional recovery team. These services typically:
- Create a forensic image of the compromised drive.
- Analyze the ransom note and sample encrypted files.
- Attempt controlled recovery methods on duplicates of the data.
- Maintain evidence for legal or incident response processes.
This route is particularly recommended for enterprises, hospitals, or organizations with mission-critical data.
Our Specialized Decryptor Service
As an alternative to sending funds to criminals, our recovery service provides a controlled decryption process. The procedure generally involves:
- Submission of one encrypted file, the ransom note, and the system’s HWID if available.
- Imaging the infected drive to work exclusively on forensic duplicates.
- Conducting a small-scale test decryption on sample files before proceeding.
- Expanding to full recovery if successful, with client approval at every stage.
This structured workflow reduces the risks associated with random tools or criminal contact, while documenting each step for transparency.
Pricing & Guarantees
Every case is unique, so costs vary depending on file volume and system complexity. While no legitimate service can promise 100% recovery, this method significantly improves chances compared to paying the attackers. Clients receive a full technical report regardless of outcome, along with recommendations for next steps.
The Ransom Demand Note
The ransom note warns victims that their files will be permanently lost, their systems corrupted, and stolen data auctioned if payment is withheld. The attackers specify a 500 EUR Monero ransom and provide both an email contact and wallet address. The note states:
Hello, looks like you got a little snake problem.
Pay us 500€ in XMR Monero and the snakes go away, forever.
Don’t pay and all files, every single byte becomes unusable, the entire system will be permanently corrupted and all data will be sold on our auction platform.
Be nice and pay us, don’t talk to anyone and keep quiet, we will handle the rest 🙂
Our XMR Wallet: 48pgNAez4CLUB4y4iAqbw742BP7Tuv8EM2xdBGsBxJDoQdk5bzVcA7NQrk5w4i3pUETrr5gr7xZ5f5EqoSDj98BYBhPkvU6
You have 72 hours to pay, after which we will permanently delete the decryption key.
To get your decryption key you need to contact us via email: [email protected]
Include your HWID and proof of payment.

Threat Overview
- Malware Family: Lamia Loader
- Category: Ransomware, crypto-malware
- Encrypted Extension: .enc.LamiaLoader
- Ransom Note: LamiaLoader.txt
- Ransom Amount: 500 EUR in Monero
- Attacker Email: [email protected]
- Wallet Address: 48pgNAez4CLUB4y4iAqbw742BP7Tuv8EM2xdBGsBxJDoQdk5bzVcA7NQrk5w4i3pUETrr5gr7xZ5f5EqoSDj98BYBhPkvU6
Technical Insights and TTPs
Lamia Loader is both a ransomware payload and malware loader, capable of dropping secondary threats such as spyware or password stealers. Its tactics mirror modern ransomware operations: initial infiltration, file encryption, ransom deployment, and persistence setup.
Common Tactics, Techniques & Procedures (MITRE ATT&CK)
- Initial Access: Phishing emails, fake software installers, malicious attachments.
- Execution: Victims launch malicious executables or scripts unknowingly.
- Persistence: Establishes registry edits and scheduled tasks.
- Defense Evasion: Employs obfuscation to bypass antivirus detection.
- Exfiltration: Data theft prior to encryption.
- Impact: File encryption with appended extension and ransom note creation.
Indicators of Compromise (IOCs)
- File Extension: .enc.LamiaLoader
- Ransom Note: LamiaLoader.txt
- Contact Email: [email protected]
- Wallet Address: 48pgNAez4CLUB4y4iAqbw742BP7Tuv8EM2xdBGsBxJDoQdk5bzVcA7NQrk5w4i3pUETrr5gr7xZ5f5EqoSDj98BYBhPkvU6
- Detection Labels:
- Avast – FileRepMalware [Inf]
- ESET – Win64/Filecoder.ACJ
- Kaspersky – Trojan-Ransom.Win32.Gen.btjj
- Microsoft – Trojan:Win32/Znyonm!rfn
- Avast – FileRepMalware [Inf]
Tools & Capabilities
- Built-in encryption algorithms for file locking.
- Loader-style modules for secondary payloads.
- Code obfuscation to avoid detection.
- Persistence through registry edits and scheduled tasks.
Infection Vectors
Lamia Loader is spread primarily through malspam campaigns, malicious attachments, pirated software, rogue installers, and drive-by downloads. It can also propagate within networks through removable media or unsecured shares, increasing its reach within corporate environments.
Consequences for Victims
Victims face complete inaccessibility of critical files such as business documents, medical data, or academic records. In addition to encryption, attackers employ double extortion by threatening to leak stolen data if ransom demands are ignored.
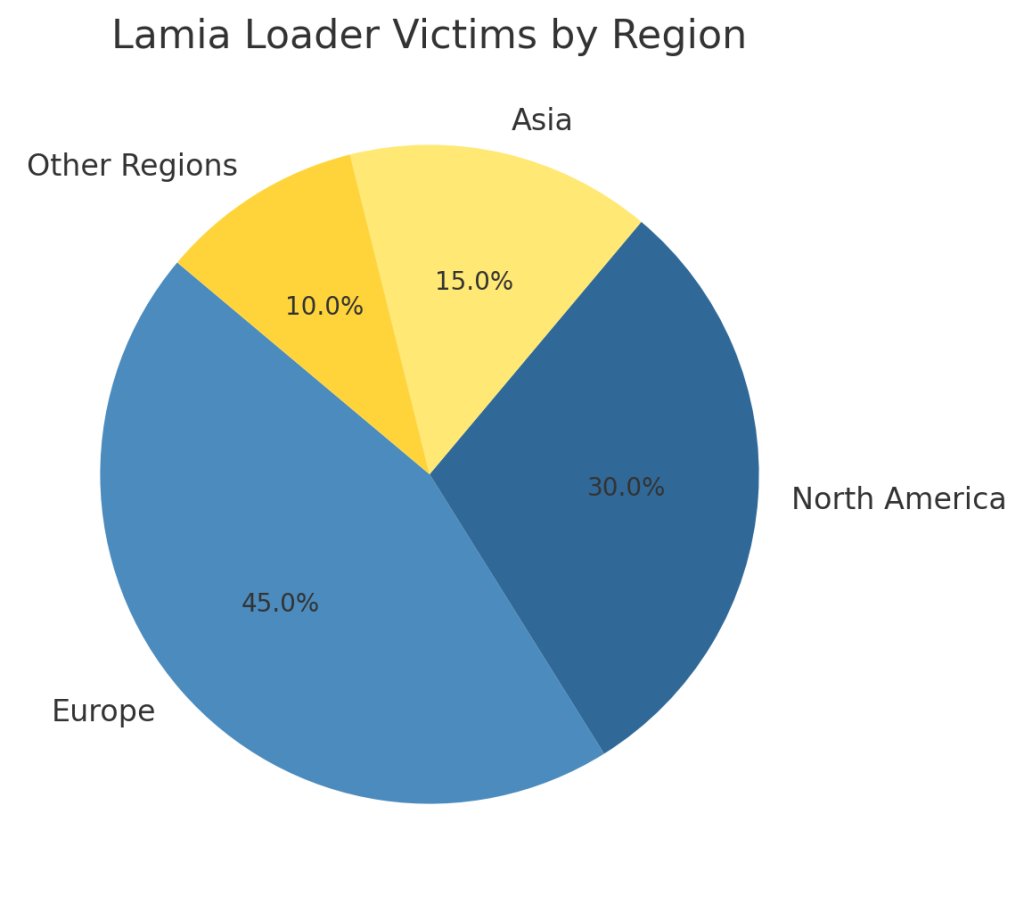
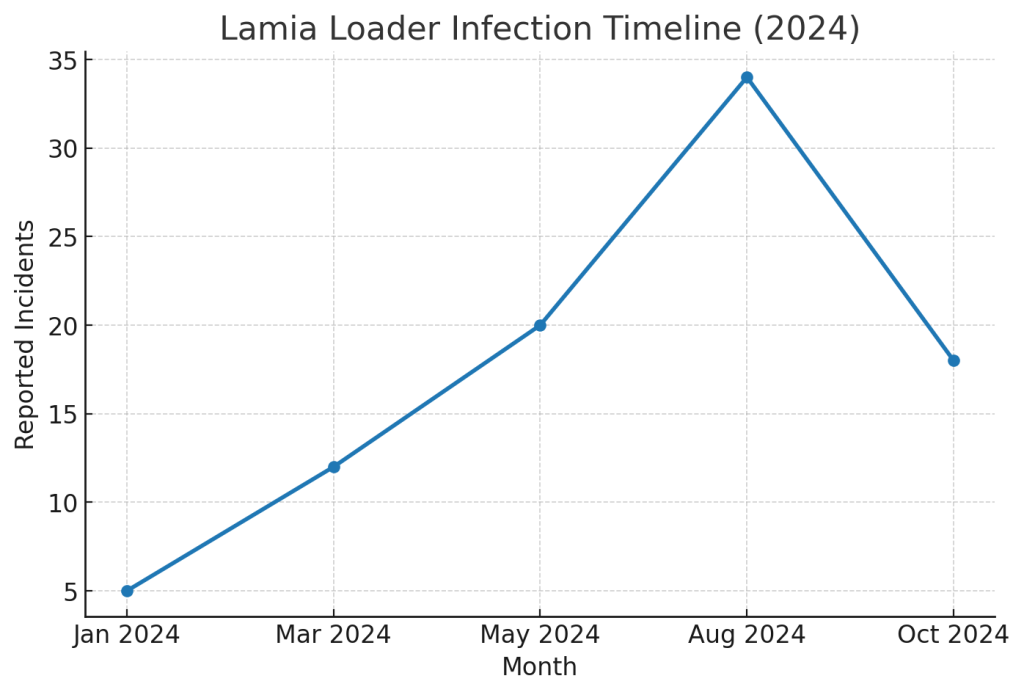
Victim Data & Global Trends
Lamia Loader has been detected worldwide, impacting both individuals and organizations.
Regions Impacted
Industries Targeted

Timeline Trends
Conclusion
Lamia Loader demonstrates how modern ransomware combines encryption with extortion and intimidation tactics. Recovery without a clean backup remains highly unlikely, but layered security practices, network isolation, and vetted recovery services reduce the damage. Directly paying ransom should always be avoided.
MedusaLocker Ransomware Versions We Decrypt