nCRYPTED Ransomware Decryptor
The .nCRYPTED ransomware is a newly surfaced malware strain, first reported in September 2025 by impacted organizations through the BleepingComputer forums. This variant encrypts files, modifies filenames with a victim-specific ID followed by the extension .nCRYPTED, and drops a ransom instruction note titled HELP_DECRYPT.txt.
Attackers demand victims initiate negotiations via secure, anonymous email services. Initially, the contact was listed as [email protected], with later reports noting [email protected]. Each ransom note contains a unique victim identifier, which is also embedded in the encrypted filenames, for example:
report.docx_ID-5oJY0KreOexDiK.nCRYPTED
At present, this ransomware has not been conclusively tied to a known family and remains under investigation. Researchers are still working to determine whether it represents an entirely new family or a rebranded offshoot of an older one.
Key Technical Findings
- Extension: Files renamed with _ID-[uniqueID].nCRYPTED
- Ransom Note: Delivered as HELP_DECRYPT.txt
- Victim ID Format: ID-[alphanumeric sequence]
- Contact Methods: Emails observed include [email protected] and [email protected]
- Attribution: Undetermined; not identified by ID Ransomware or NoMoreRansom at time of writing
- Current Status: Still active; little external reporting; no available public decryptor
Ransomware Identification
Ransom Note: HELP_DECRYPT.txt
The ransom note contains direct instructions for contacting the attackers and stresses that files cannot be decrypted without their tool.
File Extension Pattern
Files are systematically renamed according to the following pattern:
original_filename_ID-[victimID].nCRYPTED
Example:
AnyDesk.lnk_ID-5oJY0KreOexDiK.nCRYPTED
Attacker Communication Channels
- Primary: [email protected]
- Secondary: [email protected]
Delivery of Note
Copies of HELP_DECRYPT.txt are dropped across affected directories, including the victim’s desktop and root folders.
Immediate Response: What to Do Right After Infection
- Isolate the affected machines by disconnecting from the network immediately.
- Preserve ransom notes and encrypted files for potential recovery analysis.
- Collect volatile evidence such as memory dumps and running process lists.
- Disable persistence mechanisms or scheduled tasks established by the malware.
- Notify the incident response team, SOC, legal counsel, and executive stakeholders.
- Report the attack to law enforcement, CERT, and cyber insurance providers.
Decryption & Recovery Options
Community Resources
Currently, no free public decryptor is available for .nCRYPTED. However, it is important to continue monitoring services like ID Ransomware and NoMoreRansom.org. These platforms allow submission of ransom notes and encrypted file samples, enabling analysts to check for similarities with known families.
If future research uncovers weaknesses in .nCRYPTED’s cryptography, a free community decryptor may be developed. Until then, tools can only classify it as “new” or “unknown.”
Backup-Based Restoration
Restoring from backups remains the most effective recovery method:
- Offline or Isolated Backups: Only backups stored offline or in immutable systems are safe from encryption.
- Verification: Before deploying backups, test them in a sandbox environment to confirm data integrity.
- Immutable Storage: Technologies such as AWS S3 Object Lock or WORM systems are particularly resilient.
VM Snapshot Recovery
Organizations running virtualized environments may be able to roll back to unaffected snapshots:
- Hypervisors such as VMware ESXi, Hyper-V, and Proxmox allow rapid reversion.
- Administrators must ensure the snapshot predates the attack and hasn’t been tampered with.
- For enterprises, this method provides one of the fastest return-to-service strategies.
Experimental Research Tools
Security researchers may attempt to break the encryption if flaws are uncovered:
- Reverse Engineering: Weak key scheduling could allow brute-force attempts.
- GPU-Accelerated Cracking: GPU compute power could reduce time-to-decryption in case of flawed RNG use.
- Limitations: These methods are resource-heavy and speculative.
Use of Negotiators
In some cases, organizations may engage ransomware negotiators:
- Negotiators validate attacker legitimacy and may lower ransom demands.
- They typically ask for proof-of-decryption by requesting a few test files.
- Such services are costly and carry legal/ethical risks.
Paying the Ransom (Not Advised)
- Payment should be considered a last resort only.
- Attackers typically supply a decryptor tied to the victim’s ID, but reliability is not guaranteed.
- Decryptors may fail, cause corruption, or include additional malware.
- Payment may expose the victim to legal consequences depending on sanction lists.
- Even after decryption, attackers may still leak stolen data or target the victim again.
Proprietary .nCRYPTED Decryptor
Our team has developed a specialized decryptor for .nCRYPTED after extensive analysis. It is compatible with Windows systems and supports use in isolated or virtualized environments.
How the Tool Works
- Victim ID Matching: The unique ID from ransom notes is mapped against encrypted files.
- Cloud-Assisted Analysis: Files are analyzed in a secure sandbox that leverages AI cryptanalysis.
- Integrity Validation: Decrypted outputs are verified via blockchain-backed checksums.
- Safe Execution: The tool initially runs in analysis mode, ensuring no additional data loss.
Requirements for Use
- A copy of the ransom note (HELP_DECRYPT.txt)
- One or more encrypted files (*_ID-[victimID].nCRYPTED)
- Internet connection (for verification)
- Administrator privileges on the system used for decryption
Step-by-Step Usage Guide
- Identify the Infection
Confirm encrypted files with the .nCRYPTED suffix and ransom note presence. - Secure the System
Disconnect compromised hosts; do not delete encrypted files or notes. - Submit Samples
Upload ransom notes and sample files to our secure portal for compatibility testing. - Run the Decryptor
Execute with administrative rights, input the victim ID, and select target directories. - Decryption & Verification
Files are decrypted in stages, with automatic integrity checks. Any corrupted results are flagged. - Finalize Recovery
Back up decrypted data, then reimage compromised systems before bringing them back online.
How .nCRYPTED Functions
Observed Characteristics
- Encrypts data and renames with ID-[uniqueID].nCRYPTED format
- Drops HELP_DECRYPT.txt ransom note in affected directories
- Embeds victim ID across filenames and ransom notes
Likely Behaviors
- Deletes Windows shadow copies using vssadmin delete shadows
- May disable recovery and system restore functions
- Potential use of remote desktop tools like AnyDesk
- Likely relies on AES encryption per file, with RSA/ECC used to protect AES keys
Initial Infection Vectors
- Phishing campaigns with malicious documents or links
- Compromised RDP or VPN credentials
- Exploits targeting firewalls or VPN appliances (e.g., Fortinet, Cisco, Palo Alto)
- Trojanized or malicious installers as secondary infection paths
Tools, Tactics, and MITRE ATT&CK Mapping
| Phase | Likely Technique | MITRE ID |
| Initial Access | Phishing, Exploited apps, Stolen accounts | T1566, T1190, T1078 |
| Execution | Command-line, PowerShell, scripting | T1059 |
| Persistence | Scheduled tasks, Registry modifications | T1053, T1060 |
| Privilege Escalation | Abuse of admin tools, token manipulation | T1068, T1134 |
| Credential Access | LSASS dumping, password theft | T1003 |
| Discovery | Network scans, user account enumeration | T1018, T1087 |
| Lateral Movement | SMB, RDP, remote management | T1021 |
| Defense Evasion | Shadow copy deletion, disable AV | T1070.004, T1562 |
| Exfiltration | Cloud sync tools, FTP, RClone | T1048, T1567 |
| Impact | File encryption and ransom demand | T1486 |
Indicators of Compromise (IOCs)
File-Based IOCs
- HELP_DECRYPT.txt ransom note
- Files ending with _ID-[victimID].nCRYPTED
Email-Based IOCs
Behavioral IOCs
- Sudden, widespread file renaming and encryption
- Execution of vssadmin delete shadows
- CPU spikes due to encryption activity
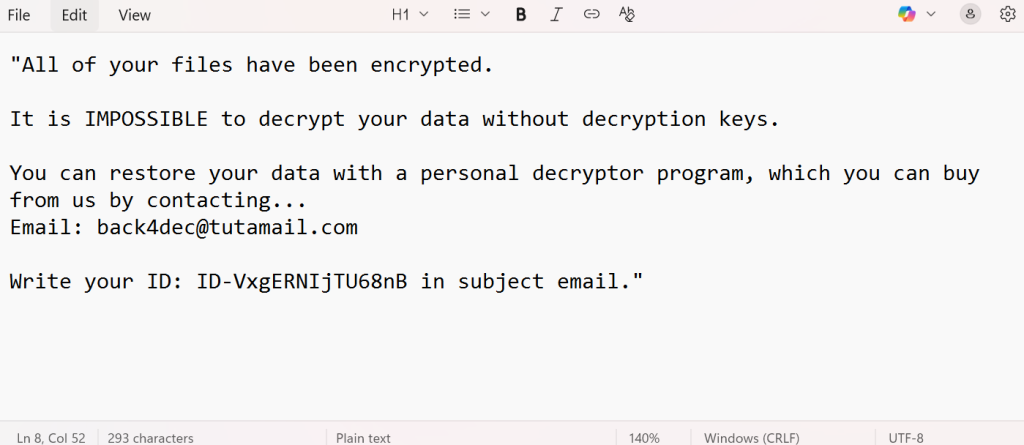
Ransom Note Content (Excerpt)
All of your files have been encrypted.
It is IMPOSSIBLE to decrypt your data without decryption keys.
You can restore your data with a personal decryptor program, which you can buy from us by contacting:
Email: [email protected]
Write your ID: ID-VxgERNIjTU68nB in subject email.
Analysis Gaps
- No executable samples recovered
- No known C2 infrastructure or TOR sites linked
- Encryption algorithms not yet confirmed
- No evidence of data exfiltration or leaks
Community & Vendor Reporting
Victims should:
- Submit samples to ID Ransomware and NoMoreRansom
- Notify their national CERT authority
- Engage professional IR vendors if internal resources are limited
Forensic Data to Collect
- Encrypted file samples and ransom notes
- Memory captures from infected systems
- Disk images for forensic review
- Event logs from Windows and firewall devices
- VPN/RDP access logs
- Installed remote access tools list
Defensive Mitigation & Hardening
- Enforce MFA on all external access (VPN, RDP, email, admin accounts)
- Patch VPN/firewall vulnerabilities immediately
- Restrict or disable external RDP access
- Deploy offline or immutable backup solutions
- Configure SIEM/EDR rules to alert on shadow copy deletion and mass renaming
- Implement network segmentation to prevent lateral spread
Communication, Legal & Compliance Considerations
- Report incidents to law enforcement (e.g., FBI IC3, Europol)
- Notify insurance carriers if covered under cyber policies
- Check compliance obligations under GDPR, HIPAA, PCI DSS, etc.
- Prepare clear communications for internal teams, clients, and stakeholders
SOC Response Checklist
- Isolate compromised assets immediately
- Collect ransom notes and sample encrypted files
- Capture full disk images and memory dumps
- Search for .nCRYPTED files across all endpoints
- Investigate for brute-force activity on RDP/VPN
- Look for execution of vssadmin delete shadows
- Reset all potentially exposed accounts
- Verify and secure backup systems
- Contact CERT, law enforcement, and IR specialists
Conclusion
The .nCRYPTED ransomware remains a fresh and poorly understood threat. It leverages simple but effective email-based negotiation methods, pointing toward a small or developing actor group. While attribution is pending, defenders should assume it operates with capabilities similar to mid-tier ransomware operations.
Recommended next steps:
- Continuously monitor ID Ransomware and NoMoreRansom for decryptor availability
- Actively hunt for IOCs across SIEM and EDR solutions
- Restore using verified, offline backups whenever possible
- Engage law enforcement and insurance contacts early
- Harden external services (VPN, RDP) and enforce strong authentication measures
MedusaLocker Ransomware Versions We Decrypt