Pay2Key Ransomware Decryptor
Mimic, also tracked under the name Pay2Key, has emerged as a dangerous ransomware family that encrypts data with the .Encrypt3 file extension. Businesses and government networks have been severely impacted, losing access to essential databases and executables. In response, our security team has created a dedicated .Encrypt3 decryptor designed to restore files without negotiating with criminals. This recovery tool has been thoroughly tested in enterprise environments such as Windows Server 2022 and VMware, delivering secure and consistent results.
How Mimic/Pay2Key Executes Its Encryption
Once deployed, Mimic ransomware scans for valuable files and renames them with the .Encrypt3 suffix. This includes databases, program executables, and even image files. After encryption, a ransom note is dropped on the system, containing a unique victim identifier and attacker contact information, commonly linked to addresses like [email protected].
The operators not only encrypt files but often engage in double extortion, exfiltrating sensitive information before locking systems. This increases pressure on victims and makes professional recovery services essential.
Functionality of Our .Encrypt3 Decryption Tool
Our decryption utility was built after a thorough reverse-engineering effort of Mimic/Pay2Key ransomware samples. The tool is regularly updated to stay ahead of new variants and offers secure recovery through a sandboxed process.
- ID Recognition and Mapping – Reads the decryption identifier in ransom notes and matches it with the correct encryption batch.
- Secure Verification – Scans affected files before decryption to ensure they are not corrupted.
- Blockchain Integrity Proof – Confirms file integrity after recovery using blockchain-backed verification methods.
- Universal Key Feature – Allows restoration even when ransom notes are missing or partially deleted.
System Requirements for Running the Decryptor
To maximize the chances of successful recovery, ensure the following are available before running the tool:
- A ransom note (commonly found as ILETISIM.txt)
- At least one encrypted file sample with the .Encrypt3 extension
- A steady internet connection for cloud-based validation
- Administrator privileges on the host system
Immediate Steps After a .Encrypt3 Infection
When a system is compromised by Mimic/Pay2Key, rapid action is essential to reduce further damage.
- Disconnect the affected machine from the network to contain the infection.
- Keep all evidence intact—do not delete encrypted files, ransom notes, or system logs.
- Check and preserve backups before attempting any recovery steps.
- Avoid communication with attackers, as sending files to them may further compromise security.
- Seek professional guidance to assess the attack and develop a structured recovery plan.
Decryption and Business Continuity
Mimic ransomware is infamous for precise attacks on corporate infrastructure, particularly servers. Since no legitimate free decryptor exists for .Encrypt3 variants, recovery usually depends on a combination of free methods and paid solutions. The success of these approaches depends heavily on how early the infection was detected and whether backups were preserved.
Options for Recovering .Encrypt3 Encrypted Files
Free Approaches
Backup Restoration – The most effective method when safe, offline backups exist. Administrators must validate these backups to ensure they are clean.
VM Rollback – If running VMware or other virtualization, snapshots created before the attack may be used to restore systems. Attackers may, however, attempt to delete or corrupt these snapshots.
Community-Driven Tools – Security projects like ID Ransomware, MalwareBazaar, and NoMoreRansom can provide identification and limited recovery assistance.
Paid Recovery Paths
Paying the Ransom – Victims may choose to pay in hopes of receiving a decryption key. This carries serious risks, including broken decryptors, hidden malware, or no response at all. Law enforcement agencies strongly discourage this option.
Negotiation Services – Some third-party firms specialize in negotiating with ransomware gangs. While they may reduce ransom costs, success is not guaranteed and fees are often high.
Professional .Encrypt3 Decryptor (Recommended) – Our tailored decryptor provides a reliable recovery path, unlike attacker-supplied tools. With built-in safety mechanisms, audit logs, and support for both online and offline environments, it ensures business continuity without empowering cybercriminal groups.
Guide to Using Our .Encrypt3 Decryptor
Our decryptor leverages the victim ID embedded in ransom notes (e.g., Yuru-OERMzNpTYffk0xdXUp7xgu7JBbMnxnLErVMv9LYH8hc*Encrypt3) to properly map encrypted data to the right keys.
Step 1 – Collect Necessary Files
Have a copy of ILETISIM.txt, one encrypted file (example: database.mdf.Encrypt3), and administrator access. Ensure internet connectivity for validation.
Step 2 – Install the Decryptor
Download and launch the decryptor package. Run as administrator and provide the ransom note plus one encrypted file for verification.
Step 3 – ID Extraction
The tool reads the unique identifier in the ransom note and matches it to our cloud decryption infrastructure.
Step 4 – File Integrity Check
A read-only scan verifies file states. A test decryption on a small set of files is performed before full recovery.
Step 5 – Full-Scale Decryption
Once validated, the decryptor restores all files to their original paths, removing the .Encrypt3 extension.
Step 6 – Post-Recovery Validation
An audit report is generated with file hashes. Security hardening recommendations are shared to reduce future exposure.
Mimic/Pay2Key: Attack Structure and Techniques
This ransomware family has been tied to advanced groups employing APT-style operations. Their tactics blend stealthy reconnaissance with aggressive encryption.
- Initial Access – Achieved through RDP brute force, VPN flaws, and phishing lures.
- Credential Theft – Use of Mimikatz and LaZagne to extract credentials.
- Lateral Movement & Recon – Network scanning with tools like Advanced IP Scanner and SoftPerfect Scanner.
- Privilege Escalation – Exploiting weak Active Directory settings.
- Data Exfiltration – Leveraging RClone, FileZilla, and WinSCP to steal data.
- Evasion – Hiding activity with tools such as Zemana and PowerTool.
- Encryption – Hybrid method combining speed (symmetric encryption) with strength (asymmetric keys).
- Cleanup – Use of vssadmin delete shadows to erase backups and prevent easy recovery.
Indicators of Compromise (IOCs)
- File Extension: .Encrypt3 (e.g., document.jpg.Encrypt3)
- Ransom Note: ILETISIM.txt
- Attacker Email: [email protected]
- Decryption ID: Randomized alphanumeric string ending in *Encrypt3
- Malware Hash Example: d1e3668635a3c594e9315eae78d23925533dbe1a
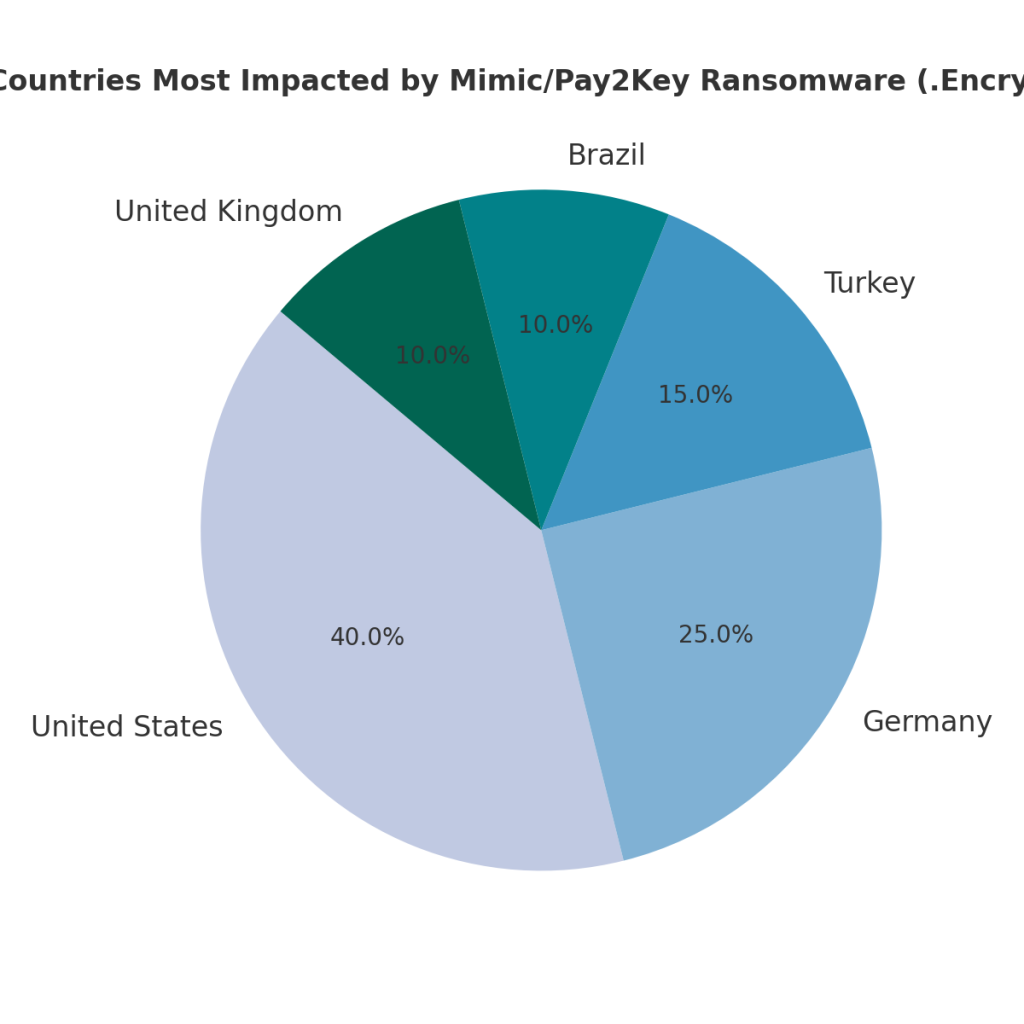
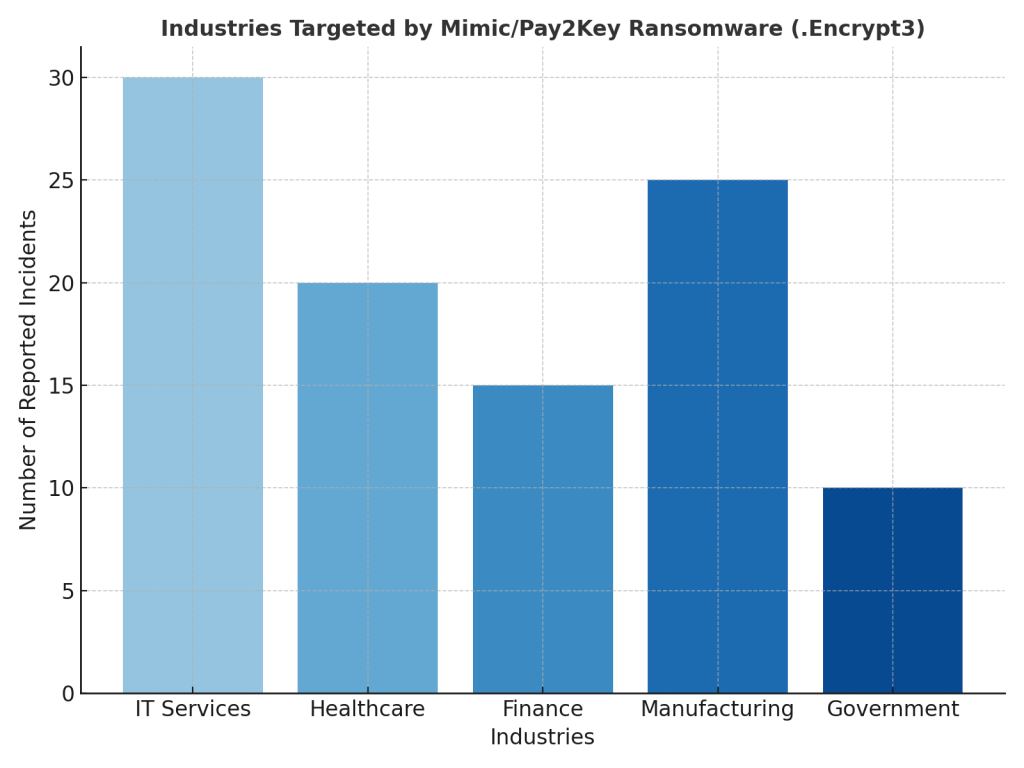
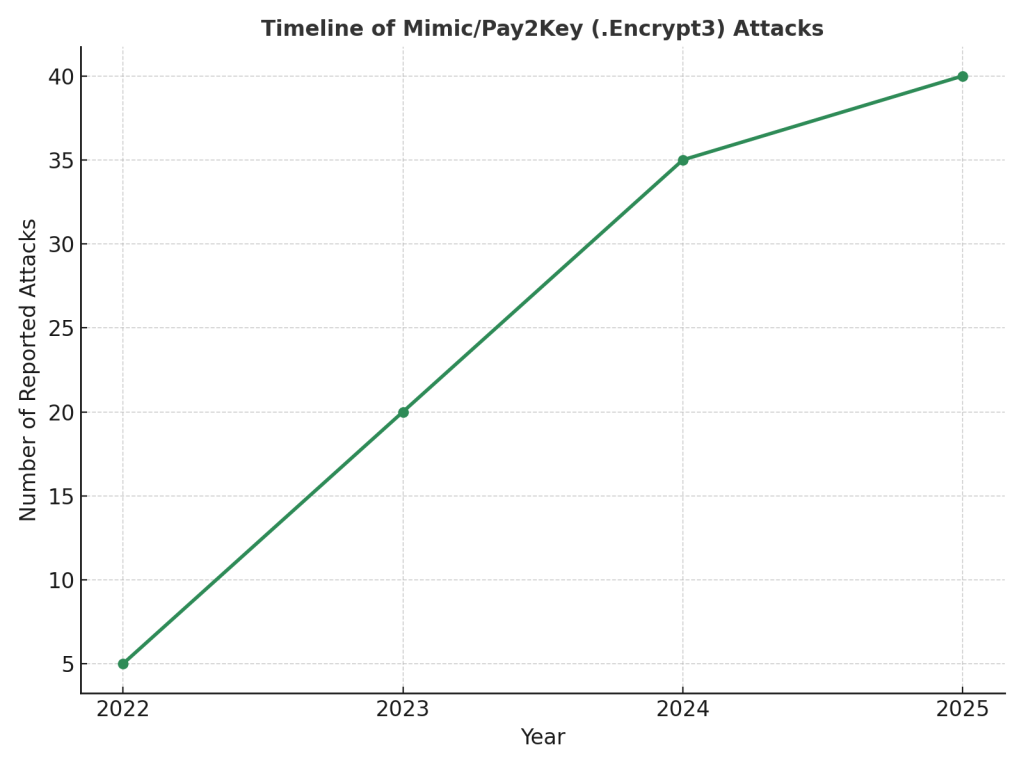
Global Victim Footprint
Mimic ransomware has been observed across different industries and geographies, especially in sectors where system downtime has devastating impacts.
Countries Affected
Industries Hit
Attack Timeline
Conclusion
A Mimic/Pay2Key breach involving the .Encrypt3 extension is highly disruptive, but not unrecoverable. Isolating infected hosts, preserving forensic artifacts, and working with trusted professionals form the foundation of an effective response. While free tools may provide partial relief, dedicated decryptor services remain the most secure option for regaining access to business-critical data.
MedusaLocker Ransomware Versions We Decrypt