Sinobi Ransomware Decryptor
Sinobi is a sophisticated ransomware group responsible for targeting critical infrastructure, including financial institutions. The group encrypts files using advanced cryptographic methods and demands ransom in cryptocurrency in exchange for a decryption key. Their tactics resemble those of the infamous REvil/Sodinokibi gang—particularly in file encryption patterns and ransom note structures.
On July 5, 2025, Hana Financial became a confirmed victim of a Sinobi ransomware attack. This incident marks one of the group’s most high-profile strikes to date.
Encrypted File Extensions Used by Sinobi
Sinobi uses a unique method to mark encrypted files:
document.docx.SINOBI
This behavior mirrors that of REvil, helping experts infer that Sinobi shares lineage or codebase similarities with REvil/Sodinokibi.
Sinobi Ransomware Chat Server Links
Below are confirmed .onion chat URLs used by the Sinobi group. Victims are typically directed to these pages via ransom notes. Use one for screenshots or further investigation.
http://sinobi7yuoppj76qnkwiobwfc2qve2xkv2ckvzyyjblwd7ucpptl62ad.onion/login
http://sinobi57mfegeov2naiufkidlkpze263jtbldokimfjqmk2mye6s4yqd.onion/login
Screenshot of one of the chat servers:
Case Study: Hana Financial Attack by Sinobi (2025)
Timeline:
- Attack Start: July 2, 2025
- Public Disclosure: July 5, 2025
- Ransomware Group: Sinobi
- Target: Hana Financial, a major U.S.-based financial institution
Impact:
- File encryption using .SINOBI extension
- Operational disruptions lasting multiple days
- Potential data exfiltration leading to regulatory exposure
- Access to Sinobi chat servers confirmed
This attack highlights the ransomware group’s ability to infiltrate and disrupt even highly secure environments.
Sinobi Ransomware Decryptor Tool
This specialized tool is designed to recover files encrypted by Sinobi without paying the ransom. It supports both Windows environments and QNAP/NAS systems, assuming the encrypted volume remains accessible.
Key Features:
- Targets extensions like .SINOBI
- Secure online decryption via dedicated servers
- No data loss during decryption
- Money-back guarantee if decryption fails
- User-friendly interface even for non-technical users
How to Use:
- Contact Support: Purchase the decryptor via WhatsApp or email
- Run as Admin: Launch with administrator access and internet connectivity
- Input Victim ID: Found in ransom note (e.g., README.txt)
- Begin Decryption: Start and let the tool restore your files
Targeted Platforms: Windows & VMware ESXi
Windows Servers
- Weaknesses exploited: RDP, unpatched services
- Encryption methods: AES for files, RSA for key protection
- Damage: Data loss, downtime, and reputational risk
VMware ESXi
- Sinobi deploys a version aimed at hypervisors, targeting virtual machines.
- Uses ESXi shell scripts to automate VM shutdown and encryption.
How to Detect Sinobi Infection
Warning Signs:
- Files renamed to .SINOBI or similar
- Appearance of README.txt in folders
Contents of the ransom note file:
Good afternoon, we are Sinobi Group.
As you can see you have been attacked by us! We offer you to make a deal with us. all you need to do is contact us by following the instructions below.
We are not politically motivated group, we are interested only in money, we always keep our word. You have a possibility to decrypt your files and save your reputation in case we find good solution!
You have to know we do not like procrastination. You have 7 days to come to the chat room and start negotiations.
– 1 Communication Process:
In order to contact with us you need to download Tor Browser.
You can download Tor Browser from this link:
https://www.torproject.org/download
After you joined to chat room you have the opportunity to request several things from us for free:
1. make a test decrypt.
2. get a list of the files stolen from you.
At the end, we should agree on the price for our services. Keep in mind that we got your income/insurance documents.
– 2 Access to the chat room:
To access us please use one of the following links:
1. hxxx://sinobi7yuoppj76qnkwiobwfc2qve2xkv2ckvzyyjblwd7ucpptl62ad.onion/login
***
If Tor is blocked in your country you can use this link: http://chat.sinobi.us.org/login
Your unique ID: 68676f1e88b682********** – use it to register in the chat room.
– 3 Blog:
To access us please use one of the following links:
1: hxxx://sinobi6ftrg27d6g4sjdt65malds6cfptlnjyw52rskakqjda6uvb7yd.onion/leaks
***
If Tor is blocked in your country you can use this link: http://blog.sinobi.us.org/leaks
– 4 Recommendations:
Do not try to recover your files with third-party programs, you will only do harm.
Do not turn off / reboot your computer.
Do not procrastinate.
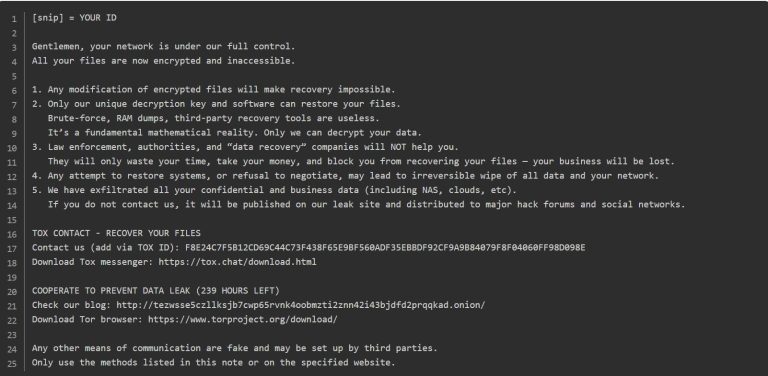
Screenshot of the ransom note file:
This file includes instructions on how to communicate with the attackers, make ransom payments, and retrieve the decryption key. You can upload a screenshot of this ransom note in your documentation.
Encryption Mechanism
| Algorithm | Role |
| AES | Encrypts individual file contents |
| RSA | Encrypts the AES keys; only decrypted by attackers’ private key |
Best Practices to Prevent Infection
Patch & Update Systems
- Apply all OS and software patches
- Regularly audit network configurations
Access Control
- Enable MFA and principle of least privilege
- Disable unused admin accounts
Network Segmentation
- Separate backups from production networks
- Use VLANs and next-gen firewalls
Backup Strategy
- Follow the 3-2-1 rule (3 copies, 2 types, 1 offsite)
- Automate and test restoration regularly
Employee Training
- Conduct frequent phishing simulations
- Educate staff on social engineering risks
Free Recovery Alternatives
Before paying or using a decryptor, try these methods:
- NoMoreRansom.org: Check for free decryptors
- System Restore Points: Roll back system state
- Shadow Copies: Recover earlier versions
- Offline Backups: Restore from cold storage
- Data Recovery Tools: Use Recuva, PhotoRec, etc.
Conclusion
The Sinobi ransomware threat, highlighted by the attack on Hana Financial, represents the modern evolution of targeted, high-stakes cybercrime. Through advanced encryption, data leaks, and real-time chat servers, Sinobi aims to extort its victims with precision.
However, with tools like the Sinobi Ransomware Decryptor, structured backup strategies, and strong cybersecurity practices, organizations can regain control—without paying the ransom.
MedusaLocker Ransomware Versions We Decrypt