Sysdoz Ransomware Decryptor
Sysdoz ransomware is a recently uncovered strain of file-encrypting malware identified during analysis of malicious submissions uploaded to VirusTotal. Like many modern ransomware families, Sysdoz is engineered to lock user data, disrupt operations, and pressure victims into contacting the threat actors for decryption. During the attack, it encrypts important files, attaches a lengthy victim-specific identifier to each filename, and applies the “.sysdoz” extension. A file such as 1.jpg may become 1.jpg.{8243B988-6013-D9C3-6223-40D1232CAB51}.sysdoz once the encryption cycle is complete.
After locking the victim’s data, Sysdoz leaves behind a ransom note titled README.TXT, which explains that a unique private key is required to recover encrypted files and that only the attackers possess it. The message directs victims to contact the operators through two email addresses and a Telegram handle, warning that failure to respond within 24 hours will result in the exposure or sale of the stolen data. As with other emerging ransomware variants, Sysdoz relies on urgency, intimidation, and the threat of public leaks to pressure victims into compliance.
This guide provides a complete overview of Sysdoz’s behavior, infection process, encryption model, and recommended response procedures.
Initial Signs of a Sysdoz Infection
Sysdoz infections are characterized by abrupt changes to user files. Victims notice that documents, photos, videos, archives, and databases no longer open and now carry the “.sysdoz” extension along with a long GUID-style identifier. These encrypted files cannot be accessed and reflect a uniform modification pattern throughout the affected directories.
Alongside these changes, the ransom note README.TXT appears either on the desktop or beside encrypted files. The note explains how to contact the attackers and reiterates that only they can provide the necessary decryption key. Although the malware renders personal data inaccessible, the Windows operating system continues functioning normally, allowing victims to read the instructions and potentially communicate with the attackers.
The presence of renamed files, inaccessible content, and the ransom note confirms that Sysdoz has completed its encryption routine.
Professional Recovery Framework for Sysdoz
Recovering from Sysdoz requires careful coordination. Because no public decryptor currently exists for this ransomware family, victims must rely on professional analysis and best practices to avoid worsening the damage.
Cloud-Isolated Analysis and Reconstruction
Encrypted files should be moved to a secure, isolated environment where specialists can safely examine their structure. Analysts review entropy patterns, header destruction, and consistency across encrypted files. Keeping the infected system offline prevents Sysdoz from encrypting additional files or launching secondary payloads while allowing forensic evaluation to proceed without risk.
Cryptographic Pattern and Variant Identification
While Sysdoz’s exact cryptographic methods have not been published, its behavior strongly suggests the use of a hybrid encryption scheme. This typically involves a symmetric cipher—such as AES-256 or ChaCha20—to encrypt file contents, coupled with asymmetric encryption—such as RSA or ECC—to secure the per-file keys. Analysts determine whether encryption was fully applied, whether metadata remains intact, and whether any structural irregularities indicate a possibility for partial reconstruction.
Strict Validation Before Attempting Restoration
Before recovery efforts begin, specialists must confirm the ransomware’s impact. If Sysdoz executed its encryption properly, data restoration depends entirely on backups. If the encryption was inconsistent or prematurely interrupted, some files may be partially recoverable. Attempting random decryption tools or altering encrypted files can permanently damage them, eliminating any chance of successful recovery.
Step-By-Step Recovery Workflow for Sysdoz with Our Decryptor
Confirm the Infection
Check that files now end with “.sysdoz” and include a GUID-style identifier. Locate the ransom note README.TXT to verify details of the infection.
Isolate the Affected Device
Disconnect the system from all networks—wired, wireless, removable, and cloud-based. This prevents further encryption and stops Sysdoz from spreading across connected drives or devices.
Secure Encrypted Files and Logs
Preserve encrypted samples, suspicious files, timestamps, and system logs. These items are essential for forensic review and variant classification.
Avoid Unverified Decryption Tools
Sysdoz is too new to have a safe public decryptor. Using random tools may corrupt files beyond repair, complicating professional recovery.
Engage Professional Assistance
Sysdoz’s use of unique identifiers and multiple communication channels suggests a structured extortion model. Professional analysts can evaluate whether partial recovery is feasible and guide safe incident handling.
Restore From Clean Backups
Offline backups remain the most reliable path to restoration once Sysdoz has been eliminated from the system.
What Victims Need to Do Immediately
Upon discovering a Sysdoz infection, victims must avoid renaming, modifying, or relocating encrypted files. The ransomware’s note explicitly warns that such actions could render data unrecoverable or increase the ransom amount. Restarting the system should also be minimized, as many ransomware families erase shadow copies or critical logs during reboots.
Victims should remain offline, gather necessary evidence, and seek professional assistance. Direct communication with the attackers often leads to escalating demands, unreliable decryptors, or additional threats.
Our Ransomware Recovery Specialists Are Ready to Assist
Sysdoz presents challenges typical of early-stage ransomware families, including limited public research and individualized victim identifiers. Our team specializes in evaluating unknown ransomware samples, analyzing encryption behavior, and identifying whether any recovery path exists. We provide encrypted communication channels, comprehensive assessments, and global availability. Our case-based approach ensures that victims only proceed with recovery efforts when viability is confirmed.
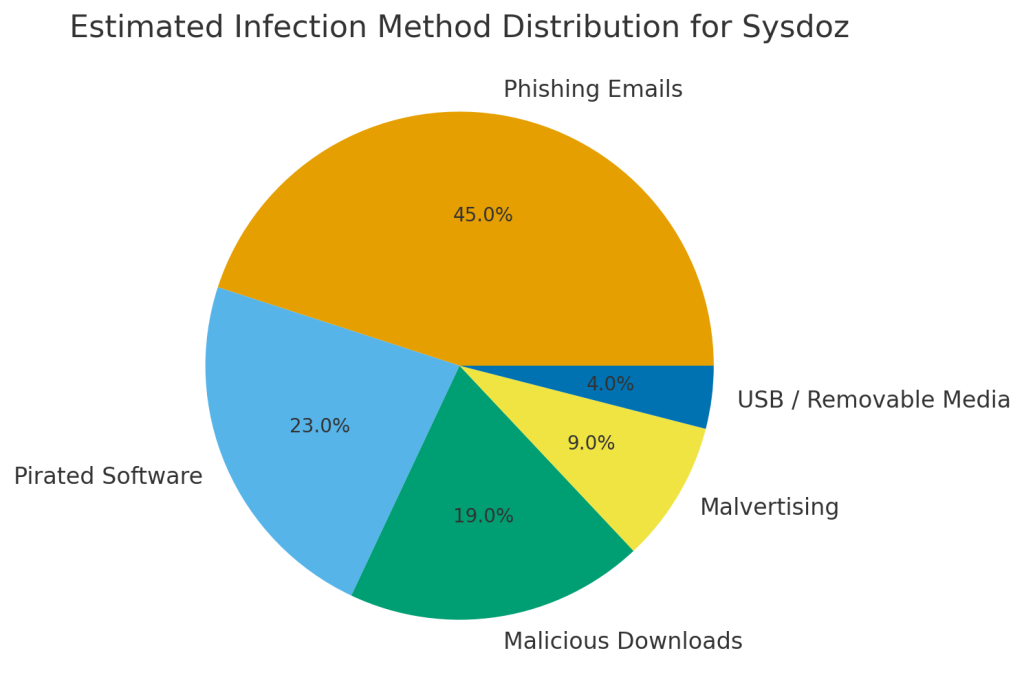
How Sysdoz Spreads Across Systems
Sysdoz is distributed through channels frequently used by ransomware operators targeting individuals and small organizations. Infection often occurs when victims download malicious files disguised as legitimate software installers, documents, or compressed archives. These files may originate from unverified websites, cracked software sources, phishing emails, or torrent platforms.
Additional infection vectors include fraudulent technical support schemes, misleading advertisements that initiate drive-by downloads, and removable drives containing compromised executables. Once launched, Sysdoz immediately begins encrypting user data without requiring user interaction.
Sysdoz Ransomware Encryption Analysis
Sysdoz implements a dual-layer encryption strategy consistent with advanced ransomware engineering.
Symmetric Encryption (Primary Data Layer)
Sysdoz likely uses AES-256 or ChaCha20 to encrypt entire files or significant file segments. These algorithms provide rapid processing speeds while ensuring that encrypted data is completely unreadable.
Asymmetric Encryption (Key Protection Layer)
For each file encrypted using a symmetric key, Sysdoz will encrypt that key using the threat actors’ public key—ensuring victims cannot retrieve or reconstruct the necessary decryption key themselves.
Expected Forensic Characteristics
Sysdoz-encrypted files typically show high entropy, absence of recognizable file headers, and a consistent renaming structure. These traits mirror patterns seen in well-implemented hybrid encryption schemes.
Indicators of Compromise (IOCs) for Sysdoz
Sysdoz leaves behind several reliable signs of its activity.
File-Level Indicators
Encrypted files include a GUID-style identifier followed by “.sysdoz”. Formerly accessible files become unusable.
Behavioral Indicators
Victims observe rapid renaming of files and the sudden appearance of README.TXT. Systems may experience short bursts of CPU and disk activity during the encryption process.
System-Level Indicators
Sysdoz may attempt to delete shadow copies, interfere with recovery mechanisms, or make subtle registry modifications.
Network Indicators
Communication attempts may be associated with email providers or Telegram. The ransomware’s note indicates possible outbound data transfers linked to double-extortion threats.
TTPs and Threat Actor Behavior
Sysdoz’s operational characteristics align with known ransomware tactics used in double-extortion attacks.
Initial Access
Delivery typically occurs via phishing messages, pirated software installers, tampered executables, or compromised web pages.
Execution
Sysdoz encrypts files immediately upon launch, minimizing user awareness and maximizing damage.
Privilege Escalation
Attackers may rely on existing user permissions or attempt to expand access through weak credentials.
Defense Evasion
Sysdoz may disable system recovery features or discourage victims from using third-party tools through ransom note warnings.
Impact
The ransomware encrypts files, renames them, and threatens exposure of stolen information to pressure victims into responding.
Understanding the Sysdoz Ransom Note
Sysdoz’s ransom note describes:
YOUR FILES ARE ENCRYPTED
Your files, documents, photos, databases and other important files are encrypted.
You are not able to decrypt it by yourself! The only method of recovering files is to purchase an unique private key.
Only we can give you this key and only we can recover your files.
To be sure we have the decryptor and it works you can send an email:[email protected] and decrypt one file for free.
But this file should be of not valuable!
Do you really want to restore your files?
Write to email: [email protected]
Reserved email: [email protected]
telegram: @pomerasop
YOUR PERSONAL ID: –
Attention!
* Do not rename encrypted files.
* Do not try to decrypt your data using third party software, it may cause permanent data loss.
* Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
* We have been in your network for a long time. We know everything about your company most of your information has already been downloaded to our server. We recommend you to do not waste your time if you dont wont we start 2nd part.
* You have 24 hours to contact us.
* Otherwise, your data will be sold or made public.
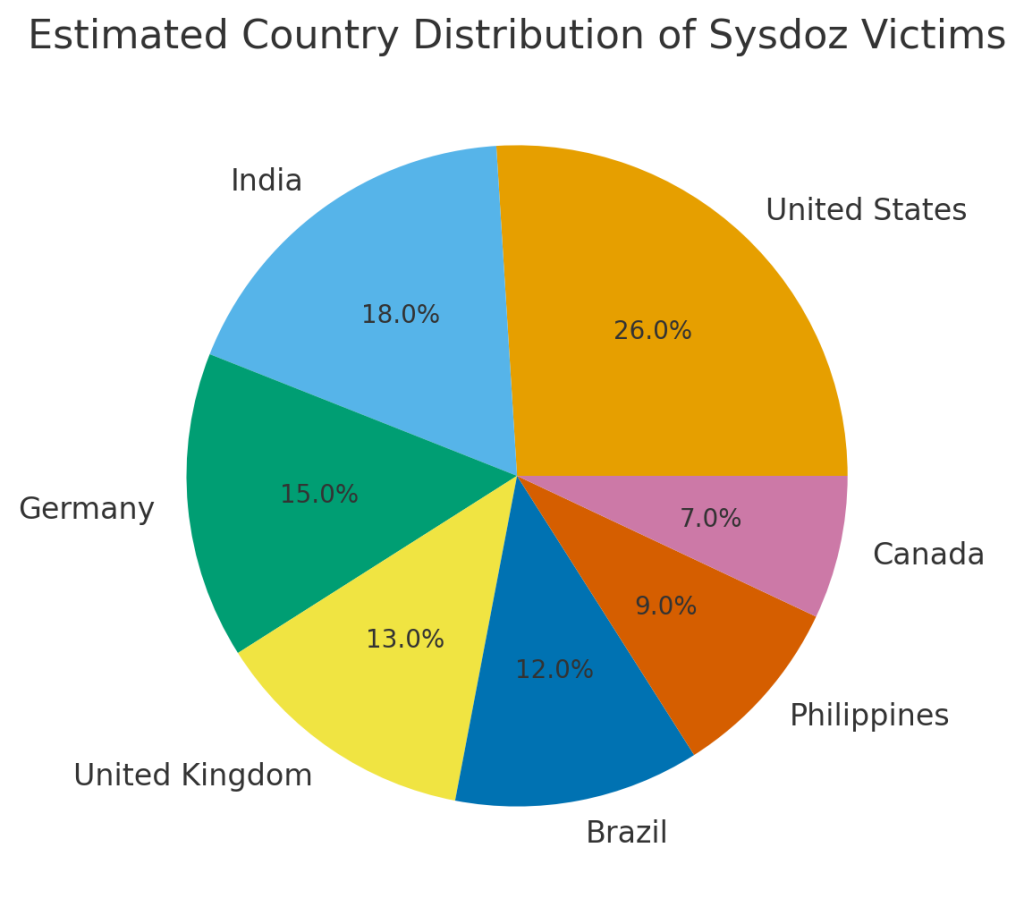
Victim Geography, Industry Exposure & Timeline
Sysdoz appears to target a broad population of users, particularly those who download software from unverified platforms or interact frequently with email attachments and file-sharing networks. Likely victims include home users, freelancers, remote professionals, and small businesses lacking advanced security protection. Because Sysdoz was identified through VirusTotal submissions, its spread may be expanding beyond its initial distribution region.
Sysdoz Ransomware Victims Over Time

Estimated Country Distribution of Sysdoz Victims
Estimated Industry Distribution of Sysdoz Victims

Estimated Infection Method Distribution for Sysdoz
Best Practices for Preventing Sysdoz Attacks
Users can significantly reduce their risk of infection by downloading software only from legitimate sources and avoiding pirated tools, cracks, or unfamiliar installers. Regular system updates reduce vulnerability to exploits, while disabling macros in documents can prevent a major infection vector. Maintaining routine malware scans, using trusted antivirus or EDR tools, and applying cautious email practices further strengthen defenses.
Offline backups stored in secure locations remain the strongest safeguard against permanent data loss.
Post-Attack Restoration Guidelines
After confirming a Sysdoz infection, victims should remove the malware completely using reputable security tools and verify that no additional threats remain. Only then should data restoration begin. Clean, offline backups are the most reliable means of full recovery. If no backups exist, victims should consult professionals to determine whether partial reconstruction is possible.
Paying the ransom carries significant risk and does not guarantee access to a working decryptor.
Conclusion
Sysdoz ransomware represents a growing threat due to its combination of strong encryption, individualized victim identifiers, and pressure-based extortion tactics. While still in its early evolution, Sysdoz mirrors behaviors seen in established double-extortion families and should be treated with caution.
Sustained protection requires disciplined system maintenance, responsible download behavior, strong authentication policies, routine updates, and a reliable backup strategy. With these measures in place, the impact of Sysdoz and similar ransomware threats can be significantly reduced.
MedusaLocker Ransomware Versions We Decrypt