Bactor Ransomware Decryptor
Our threat response and malware research team has designed a dedicated decryptor and containment workflow to address Bactor ransomware, a hybrid encryption and data-theft malware discovered in 2025.
This ransomware encrypts user data with AES and RSA encryption algorithms, appends the “.bactor” extension to files (e.g., photo.jpg.bactor, invoice.pdf.bactor), replaces the desktop wallpaper, and creates a ransom note named “#HowToRecover.txt.”
Our decryptor solution focuses on three key objectives:
- Conducting a sandboxed forensic analysis of encrypted samples;
- Identifying variant signatures, victim IDs, and cipher markers unique to the Bactor strain; and
- Executing verified, controlled decryption with full audit and chain-of-custody documentation for compliance.
The decryptor is compatible with both cloud-assisted recovery environments and air-gapped forensic systems. Every recovery session begins with read-only mode validation to ensure encryption mapping is verified before any decryption attempt takes place.
How the Bactor Decryptor Operates
Once encrypted file samples and ransom notes are received, the decryptor analyzes key generation routines and encryption headers. These are matched against an internal knowledge base of Bactor’s encryption fingerprints and prior incident reports.
If the ransomware version can be mapped, a Proof-of-Concept (PoC) decryption is run on a few small files to confirm key reconstruction. When verified, the decryptor initiates a secure restoration cycle, monitored in real-time by forensic analysts.
Requirements for Recovery:
- Ransom note file (#HowToRecover.txt) and desktop wallpaper screenshot
- Several .bactor sample files (unaltered copies)
- Administrator privileges on a recovery host
- Optional internet connection for cloud-based validation
Immediate Steps After a Bactor Infection
- Isolate infected systems immediately. Disconnect them from LAN, Wi-Fi, and shared or cloud storage.
- Preserve the evidence. Retain all encrypted files, ransom notes, and logs exactly as they appear.
- Collect forensic telemetry. Save AV/EDR alerts, Windows Event Logs, and firewall data to assist in post-incident analysis.
- Dump volatile memory (RAM) if possible — encryption threads or key fragments may still exist.
- Avoid contacting the attacker’s email address. Communications via [email protected] should be routed through cybersecurity professionals.
File Recovery & Data Restoration Options
Free or Standard Methods
Offline Backups:
If clean, disconnected backups are available, restore files after verifying integrity. Avoid reconnecting infected systems during this process.
Law Enforcement Collaboration:
There is currently no public decryptor for Bactor. However, similar ransomware variants have been cracked in the past through law enforcement key seizures. Reporting the incident may improve your recovery odds.
Professional & Specialist Recovery
Analyst-Guided Decryption:
Our team performs variant validation followed by PoC decryption tests before attempting full-scale restoration. All processes are logged and verified.
Ransom Payment (Not Recommended):
The attackers behind Bactor offer a 48-hour payment window, doubling the ransom afterward. However, paying does not guarantee recovery or prevent stolen data from being sold or leaked.
How to Use Our Bactor Decryptor — Step-by-Step
Step 1 — Identify the Infection:
Confirm that files end in .bactor and locate the ransom note #HowToRecover.txt and altered wallpaper instructions.
Step 2 — Secure the Network:
Disconnect infected systems and ensure backups are safely offline.
Step 3 — Engage Our Recovery Team:
Send sample encrypted files and ransom materials for variant analysis. We’ll provide a detailed timeline for PoC and full decryption.
Step 4 — Run the Decryptor:
Launch the decryptor as an administrator. Internet access may be required if cloud-based key mapping is used.
Step 5 — Input Victim ID:
The ransom note includes a unique ID; enter it when prompted to link your case to the specific encryption batch.
Step 6 — Start Decryption:
Initiate the recovery and let the tool reconstruct files in a clean, separate directory. Reports detailing restored files and integrity results will be generated automatically.
Understanding Bactor Ransomware
Overview:
Bactor ransomware is a double-extortion malware, meaning it not only encrypts local files but also steals and threatens to publish data. The attackers claim to hold backups of victims’ files and threaten to leak or sell the data to competitors if no ransom is paid.
Infection Behavior:
- Encrypts documents, photos, archives, and databases, appending .bactor to each file.
- Drops a ransom note (#HowToRecover.txt) in every directory.
- Modifies the desktop wallpaper to display recovery instructions.
- Allows “proof decryption” of up to two files smaller than 1 MB.
- Increases the ransom price after 48 hours.
Threat Dynamics:
The email address [email protected] is consistently used across known cases, suggesting a small but active operator group. The double-threat strategy—encrypt first, leak later—makes containment time-sensitive and recovery without expert guidance difficult.
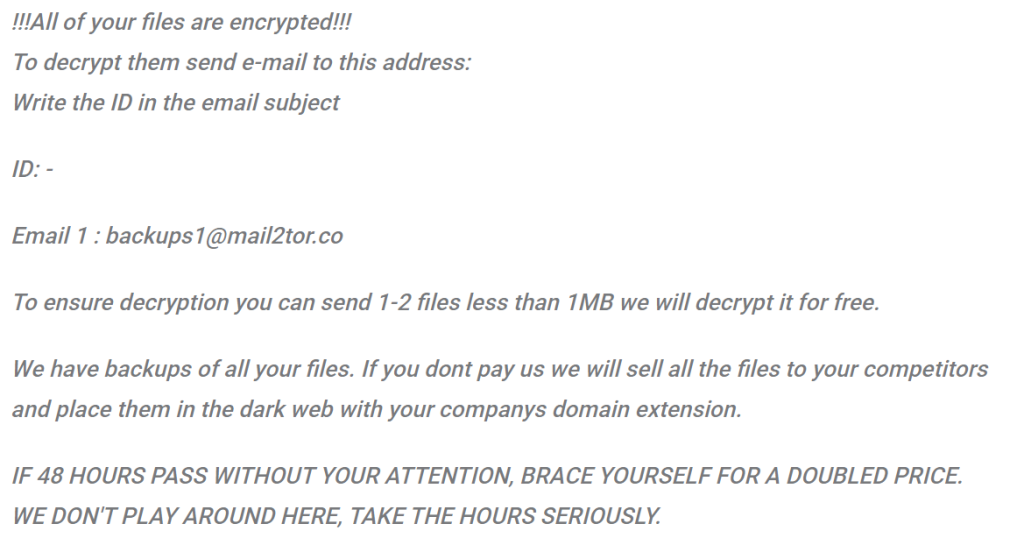
Ransom Note — “#HowToRecover.txt”
Filename: #HowToRecover.txt
Location: Dropped in each folder containing encrypted data.
Excerpt from the Note:
!!!All of your files are encrypted!!!
To decrypt them send e-mail to this address:
Write the ID in the email subject
ID: –
Email 1 : [email protected]
To ensure decryption you can send 1-2 files less than 1MB we will decrypt it for free.
We have backups of all your files. If you dont pay us we will sell all the files to your competitors
and place them in the dark web with your companys domain extension.
IF 48 HOURS PASS WITHOUT YOUR ATTENTION, BRACE YOURSELF FOR A DOUBLED PRICE.
WE DON’T PLAY AROUND HERE, TAKE THE HOURS SERIOUSLY.
Technical Indicators & Detections
Ransomware Name: Bactor
Extension: .bactor
Ransom Note: #HowToRecover.txt
Encryption: AES + RSA (hybrid)
Contact Email: [email protected]
Free Decryptor: None available
Detection Names:
- Avast → Win32:MalwareX-gen [Ransom]
- ESET → Win32/Filecoder.Krypt.A
- Kaspersky → HEUR:Trojan-Ransom.Win32.Generic
- Microsoft → Ransom:Win32/Conti!rfn
Indicators of Compromise (IOCs):
- Presence of .bactor extension on encrypted files
- Desktop wallpaper replacement with ransom email instructions
- Ransom note referencing 48-hour deadline
- Potential presence of secondary malware like credential stealers
Tactics, Techniques & Procedures (TTPs)
- Initial Access: Malicious attachments, cracked software, phishing lures.
- Execution: AES/RSA encryption of data at rest.
- Persistence: Registry modifications and autorun entries for ransom re-display.
- Defense Evasion: Shadow copy deletion, recovery point disabling.
- Exfiltration: Uploading data to attacker servers prior to encryption.
- Impact: Complete encryption of user data with extortion threat for resale or public leak.
Victim Landscape
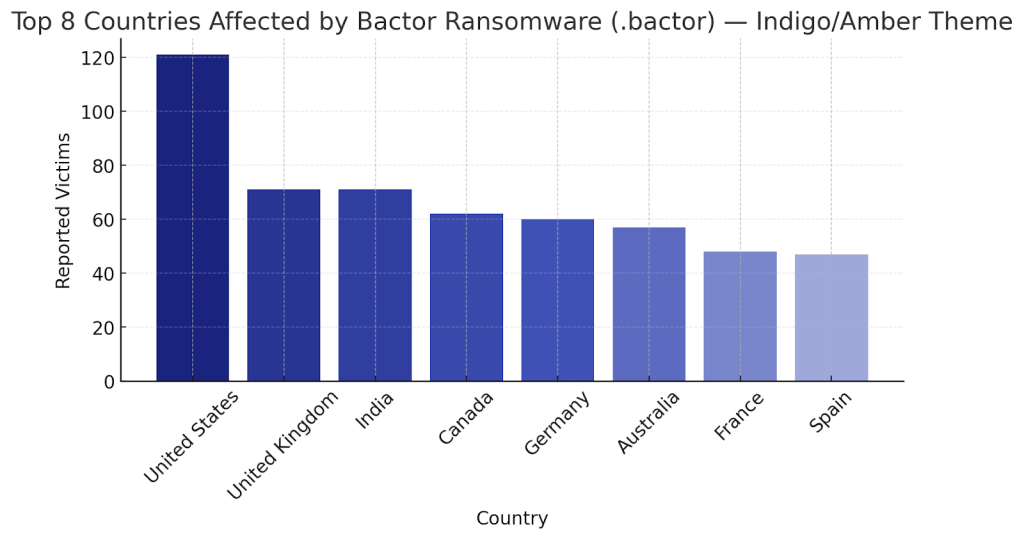
Regions Impacted:
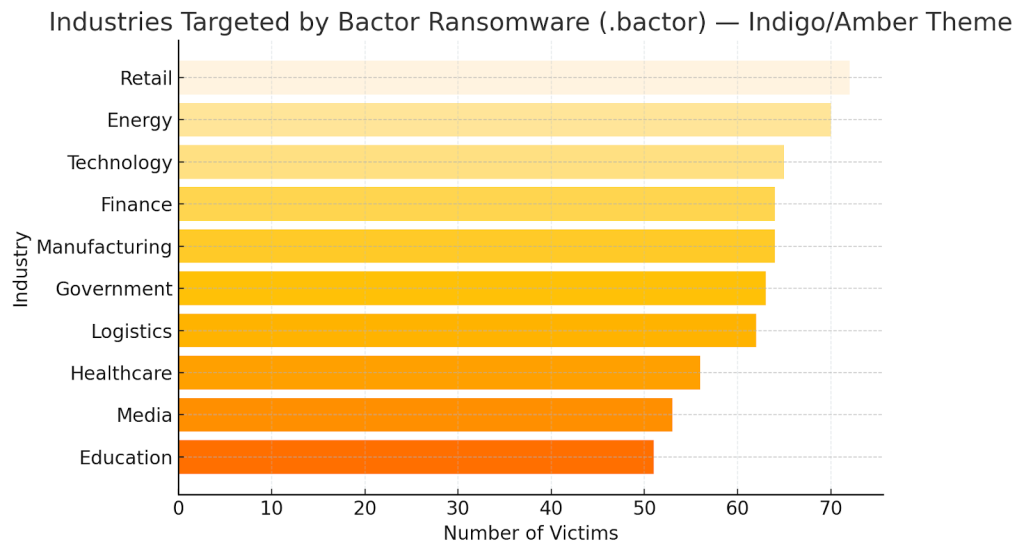
Industries Most Targeted:
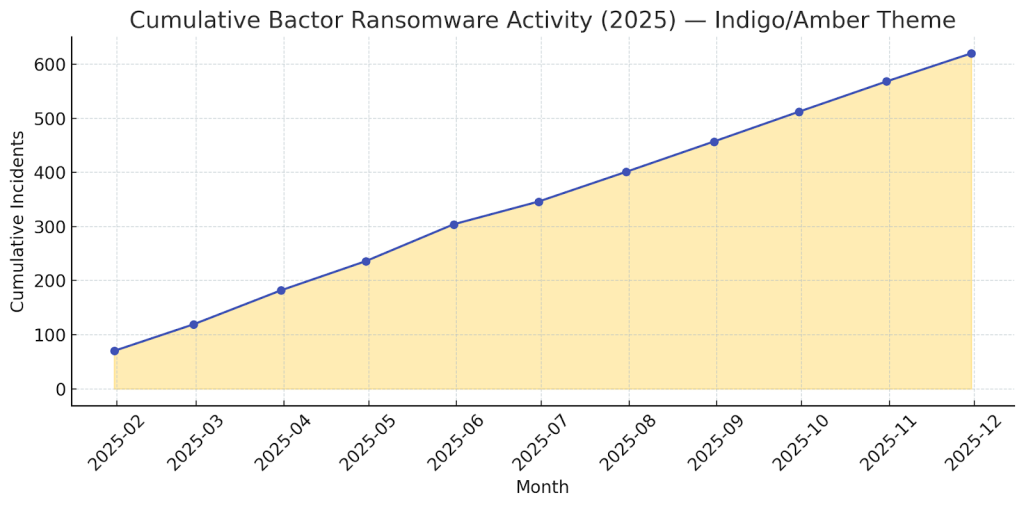
Timeline:
Conclusion
Bactor ransomware is a prime example of how ransomware operations have evolved beyond encryption into full-fledged data extortion businesses. Its aggressive countdown tactics, threats of leaks, and the psychological pressure of ransom escalation make rapid response and isolation critical. Victims should avoid ransom payment and focus on containment, forensics, and recovery via backups or verified decryptor services. Organizations can mitigate exposure by maintaining immutable, offline backups, enforcing strict access control policies, conducting email security training, and patching vulnerabilities before they can be exploited. Awareness and readiness are the only sustainable defenses against Bactor-class ransomware campaigns.
MedusaLocker Ransomware Versions We Decrypt