Zarok Ransomware Decryptor
Zarok is a crypto-ransomware strain identified from fresh submissions to VirusTotal in early 2025. It encrypts data and adds a random four-character extension to each file — for example, photo.jpg becomes photo.jpg.ps8v. After encryption, it changes the desktop wallpaper and drops a ransom note titled “README_NOW_ZAROK.txt.”
Victims are told to pay roughly €200 worth of Bitcoin, while some ransom messages display higher demands of €500. The operators instruct victims to contact them via Telegram (@stfuhq), promising decryption after payment. They claim stolen data will be deleted upon ransom receipt but threaten to leak all files publicly if payment isn’t made.
Our Zarok Decryptor — Precision Recovery, Forensic Accuracy
Our cybersecurity and digital forensics division has developed a specialized decryptor process tailored to Zarok infections. The goal is to recover data safely, maintain forensic integrity, and prevent reinfection.
The decryption framework is designed to:
- Run inside a sandboxed environment to detect the specific Zarok variant.
- Identify key signatures and encryption markers based on cryptographic headers.
- Execute controlled Proof-of-Concept (PoC) decryption on select samples before a full restoration is initiated.
This solution works in both cloud-assisted (for rapid verification) and offline forensic configurations. Every session starts in read-only mode, ensuring zero modification to evidence until the encryption is fully mapped and confirmed safe for recovery.
Immediate Response Checklist — Contain, Preserve, Analyze
- Isolate infected machines immediately from all networks, Wi-Fi, and shared drives.
- Preserve encrypted data and ransom notes exactly as found. Do not rename, open, or alter any files.
- Document the evidence — export system logs, EDR alerts, and firewall telemetry for post-incident analysis.
- Capture memory (RAM) where possible, as some encryption keys and C2 traces may exist in volatile memory.
- Refrain from direct communication with the attackers; allow experts to handle all negotiations or outreach.
Recovery Solutions — Practical Paths to Data Restoration
Free or Standard Options
Offline or Immutable Backups
If clean backups exist, restore files from them after verifying checksums or integrity. Always perform recovery on isolated systems to prevent reinfection.
Free Decryptor Availability
As of now, there is no publicly available decryptor for Zarok. Some Chaos-based variants have been cracked before, so it’s worth monitoring No More Ransom or contacting national CERT organizations for updates.
Specialist & Advanced Options
Analyst-Led Forensic Decryption
Our analysts perform structured testing and PoC decryption before attempting bulk recovery. This minimizes risk and ensures key compatibility before full restoration.
Ransom Payment (Not Advised)
Paying the ransom offers no guarantees. Many Zarok victims report nonfunctional decryptors or additional extortion demands after payment. Funds also perpetuate ransomware development networks.
How to Use Our Zarok Decryptor — Step-by-Step
Step 1 — Confirm the infection.
Check for encrypted files with random four-character extensions (e.g., .ps8v) and the presence of README_NOW_ZAROK.txt.
Step 2 — Secure your systems.
Isolate infected endpoints and detach network shares and backups.
Step 3 — Submit samples.
Send ransom notes and 2–3 encrypted file samples through our secure intake for cryptographic profiling.
Step 4 — Run the decryptor.
Execute the tool with administrator rights; an internet connection may be needed for remote verification.
Step 5 — Enter your victim ID.
Use the ID from the ransom note to align with your encryption batch.
Step 6 — Begin recovery.
Once the decryption keys are validated, the tool restores files to a clean folder, logging every action for forensic verification.
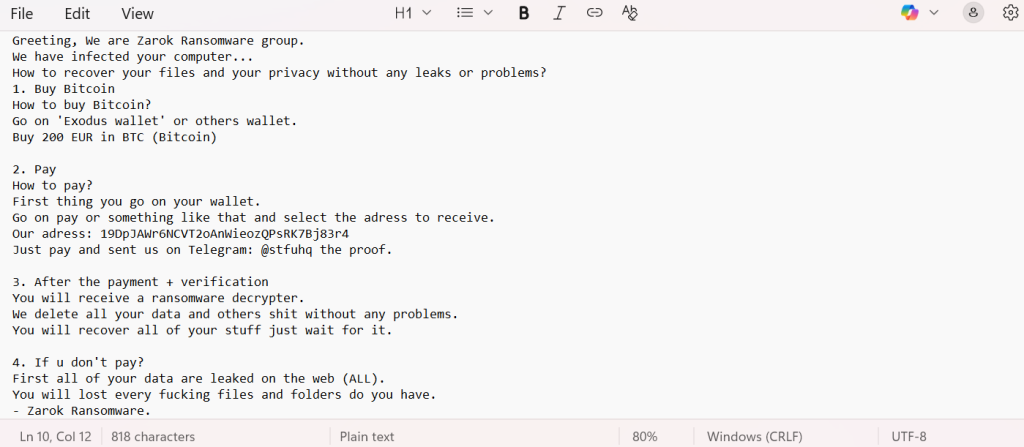
Ransom Note — “README_NOW_ZAROK.txt”
Note File: README_NOW_ZAROK.txt
Location: Typically present in every encrypted folder and referenced in the desktop wallpaper.
Excerpt (as observed):Greeting, We are Zarok Ransomware group.
We have infected your computer…
How to recover your files and your privacy without any leaks or problems?
1. Buy Bitcoin
How to buy Bitcoin?
Go on ‘Exodus wallet’ or others wallet.
Buy 200 EUR in BTC (Bitcoin)
2. Pay
How to pay?
First thing you go on your wallet.
Go on pay or something like that and select the adress to receive.
Our adress: 19DpJAWr6NCVT2oAnWieozQPsRK7Bj83r4
Just pay and sent us on Telegram: @stfuhq the proof.
3. After the payment + verification
You will receive a ransomware decrypter.
We delete all your data and others shit without any problems.
You will recover all of your stuff just wait for it.
4. If u don’t pay?
First all of your data are leaked on the web (ALL).
You will lost every fucking files and folders do you have.
– Zarok Ransomware.
Technical Profile & Threat Indicators
Name: Zarok Ransomware
Encrypted Extension: Four random characters (e.g., .ps8v)
Ransom Note: README_NOW_ZAROK.txt
Encryption: AES + RSA (hybrid method)
Demand: 200–500 EUR in Bitcoin
Contact: Telegram @stfuhq
Wallets: 19DpJAWr6NCVT2oAnWieozQPsRK7Bj83r4, BC1QE4CCX4TDM0ACL7809ET4U5JK8Z78X7GWJ3ZMX5
Common Vendor Detections:
- Avast → Win32:MalwareX-gen [Ransom]
- ESET → MSIL/Filecoder.Chaos.C
- Kaspersky → HEUR:Trojan-Ransom.Win32.Generic
- Microsoft → Ransom:MSIL/FileCoder.YG!MTB
Tactics, Techniques & Procedures (TTPs)
- Initial Access: Phishing campaigns, torrent downloads, cracked software bundles.
- Execution: File encryption using AES/RSA hybrid model.
- Persistence: Registry and startup entries that re-display ransom note.
- Defense Evasion: Deletes shadow copies, disables recovery tools.
- Exfiltration: Uploads stolen data to attacker-controlled hosts before encryption.
- Impact: Data loss, public leaks, and reputational damage.
Victim Landscape — Geography, Targets & Timeline
Regions:
Industries:
Timeline:
Conclusion
Zarok represents a clear evolution in affordable ransomware distribution — smaller, faster, and built for volume. Its hybrid encryption, Telegram-based payment channel, and moderate ransom size are optimized for quick turnover rather than large-scale negotiation. Despite its crude messaging, the impact is severe: data encryption coupled with potential public exposure. Effective mitigation relies on fast isolation, reliable backups, and professional decryption assistance. Staying ahead means maintaining layered email defenses, patching vulnerabilities, and enforcing strict access controls across networks.
MedusaLocker Ransomware Versions We Decrypt