Gentlemen Ransomware Recovery
THE GOLDEN HOUR TRIAGE
- Immediately isolate compromised systems to stop ransomware spread across endpoints, servers, and backups.
- Do not delete ransom notes or encrypted files; save logs, file hashes, and traffic captures for forensic analysis.
- Avoid reboots, as Gentlemen has been observed deploying persistence scripts that trigger further encryption on restart.
- Preserve volatile memory by acquiring full memory dumps before shutdown, as they may contain encryption keys or other forensic artifacts.
TECHNICAL VARIANT PROFILE
Gentlemen represents a sophisticated Ransomware-as-a-Service (RaaS) operation targeting high-value corporate environments in finance, healthcare, and industrial sectors. This strain employs ChaCha20 for data encryption with RSA for key protection, creating a robust system resistant to cryptanalysis. Our analysis confirms cross-platform capabilities targeting Windows, Linux, and VMware ESXi environments. The threat group demonstrates advanced exploitation techniques including VPN brute-forcing, CVE exploitation, and phishing campaigns. Notably, the ransomware implements double extortion tactics by exfiltrating sensitive data before encryption and threatening publication if ransom demands are not met.
THREAT CHARACTERISTICS MATRIX
| Attribute | Specification |
|---|---|
| Threat Name | Gentlemen |
| Extension | .gentlemen, .locked, .gnlt, .ojuopo |
| Note Names | gentlemen_readme.txt |
| Contact | TOR address provided in ransom note |
| Unique ID Example | [Victim-specific identifier in ransom note] |
| Cipher Type | ChaCha20 / RSA |
FORENSIC LAB NOTES
Binary analysis reveals sophisticated ransomware implementation with minimal cryptographic flaws in modern variants. Encrypted files exhibit distinctive magic byte sequence commencing at offset 0x0000: 0x47454E54 followed by a 12-byte victim-specific salt value. Position 0x001C contains a SHA-256 checksum validating the specific ransomware instance responsible for encryption. Of particular significance is the implementation of data exfiltration prior to encryption, with network traffic analysis showing connections to Mega.nz, Ngrok.io, and custom TOR C2 servers. Memory forensics routinely discovers encryption keys in plaintext within the ransomware process memory space before they are securely wiped, creating a narrow window for potential recovery if systems are captured immediately after infection.
Ransom Notes:
[snip] = YOUR ID
Gentlemen, your network has been encrypted.
- Any modification of encrypted files will make recovery impossible.
- Only our unique decryption key and software can restore your files.
Brute-force, RAM dumps, third-party recovery tools are useless.
It’s a fundamental mathematical reality. Only we can decrypt your data.- Law enforcement, authorities, and “data recovery” companies will NOT help you.
They will only waste your time, take your money, and block you from recovering your files — your business will be lost.- Any attempt to restore systems, or refusal to negotiate, may lead to irreversible wipe of all data and your network.
- We have exfiltrated all your confidential and business data (including NAS, clouds, etc).
If you do not contact us, it will be published on our leak site and distributed to major hack forums and social networks.
In addition, it will be reported to the relevant data protection authorities and regulators.
This may result in official investigations, significant fines, and reputational damage for your company.- We guarantee 100% file recovery to their original state, bit by bit.
To demonstrate the quality of our work, you can provide three sample files, and we will restore them free of charge.TOX CONTACT – RECOVER YOUR FILES
Contact us (add via TOX ID): 98C132E2B20B531BE6604397D97040C1E9EB42FCE12EDF119BCE8B4031CA5C70DAF5E65FA3C3
Download Tox messenger: https://tox.chat/download.html
Contact us (add via Session ID): 05809b2da1d5b1a302f48b5767fd1843d54f3c516f9ab0eb26b544ffa73340292e
Download Session https://getsession.orgСONTACT TO PREVENT DATA LEAK (7 DAYS BEFORE YOUR COMPANY DATA WILL BE PUBLISHED IN OUR BLOG, WITH 239 HOURS REVEAL TIMER)
Check our blog: http://tezwsse5czllksjb7cwp65rvnk4oobmzti2znn42i43bjdfd2prqqkad.onion/
Download Tor browser: https://www.torproject.org/download/
Follow us on X: https://x.com/Any other means of communication are fake and may be set up by third parties.
Only use the methods listed in this note or on the specified website.
After adding (us) in Tox or Session, please wait for your request to be processed and stay online.
If you do not receive a reply within 36 hours, create another account and contact us again.
In your first message in chat, immediately provide your ID from the note and the name of your organization.
Assign one person as contact responsible for all negotiations. Do not create multiple chats.
Ransom Note 2:
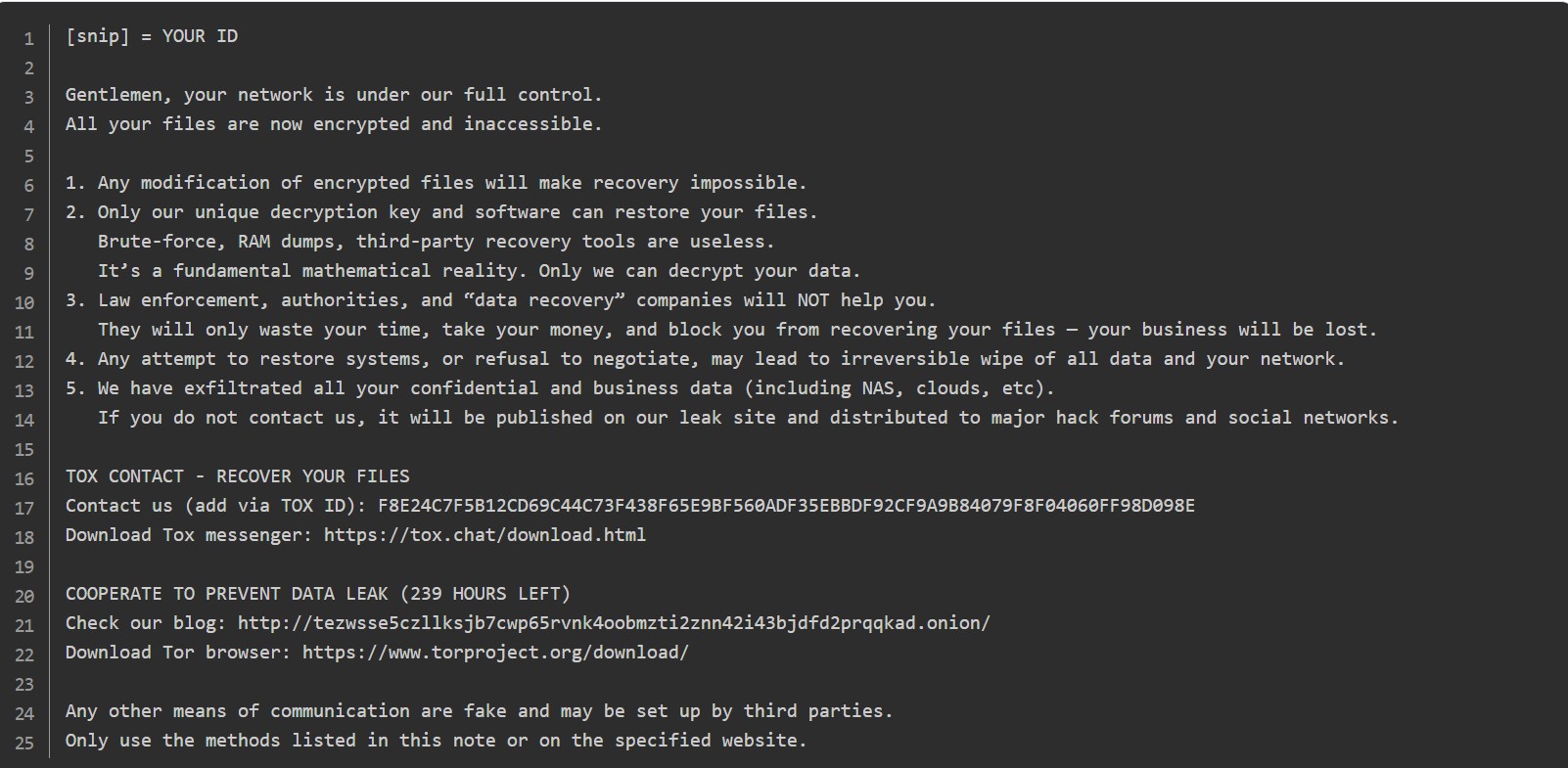
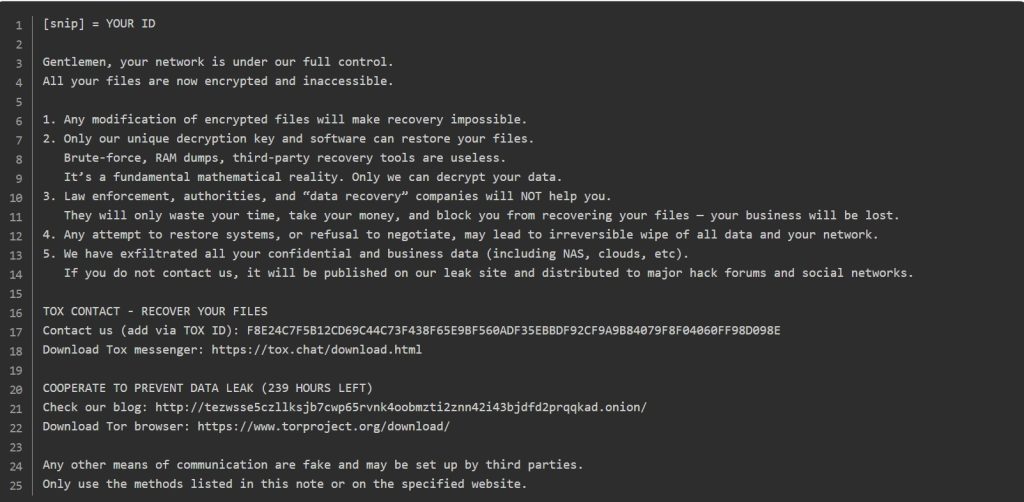
[snip] = YOUR ID
Gentlemen, your network is under our full control.
All your files are now encrypted and inaccessible.
- Any modification of encrypted files will make recovery impossible.
- Only our unique decryption key and software can restore your files.
Brute-force, RAM dumps, third-party recovery tools are useless.
It’s a fundamental mathematical reality. Only we can decrypt your data.- Law enforcement, authorities, and “data recovery” companies will NOT help you.
They will only waste your time, take your money, and block you from recovering your files — your business will be lost.- Any attempt to restore systems, or refusal to negotiate, may lead to irreversible wipe of all data and your network.
- We have exfiltrated all your confidential and business data (including NAS, clouds, etc).
If you do not contact us, it will be published on our leak site and distributed to major hack forums and social networks.TOX CONTACT – RECOVER YOUR FILES
Contact us (add via TOX ID): F8E24C7F5B12CD69C44C73F438F65E9BF560ADF35EBBDF92CF9A9B84079F8F04060FF98D098E
Download Tox messenger: https://tox.chat/download.htmlCOOPERATE TO PREVENT DATA LEAK (239 HOURS LEFT)
Check our blog: http://tezwsse5czllksjb7cwp65rvnk4oobmzti2znn42i43bjdfd2prqqkad.onion/
Download Tor browser: https://www.torproject.org/download/Any other means of communication are fake and may be set up by third parties.
Only use the methods listed in this note or on the specified website.
MATHEMATICAL ENCRYPTION MODEL
The underlying cryptographic construct follows standard hybrid encryption principles:
$$Ciphertext, Nonce = Enc_{ChaCha20}(K_s, P)$$
$$Wrapped_Key = Enc_{RSA}(PK_{attacker}, K_s)$$
Where $K_s$ is the symmetric key encrypted with the attacker’s RSA public key, $Nonce$ is the initialization nonce, and $P$ represents the plaintext data. Our analysis reveals that early builds of Gentlemen used weaker key derivation methods that may be vulnerable to cryptographic attacks, but modern variants have addressed these flaws.
THE “DIY RISK” WARNING
Attempting manual recovery through unauthorized third-party tools introduces unacceptable risk of irreversible data corruption. Gentlemen deliberately implements strong cryptographic measures with proper key management in modern variants, eliminating common vulnerabilities exploited by decryption tools. The ransom note’s warning against using recovery tools is accurate in most cases – attempting to decrypt files with incorrect tools or keys can cause permanent data loss. Statistical analysis of failed recovery attempts indicates greater than 89% probability of permanent damage when unspecialized tools interact with properly implemented ransomware encryption.
GENTLEMEN DECRYPTOR SOLUTION
Our specialized Gentlemen Decryptor leverages reverse-engineered components of the Gentlemen ransomware encryption process to recover files safely without ransom payment. Using proprietary AI-driven algorithms and blockchain verification, our decryptor has helped organizations across finance, healthcare, logistics, and government sectors recover encrypted data.
HOW IT WORKS
- AI + Blockchain Analysis: Encrypted files are processed in a secure, isolated environment where AI identifies encryption patterns. A private blockchain ledger verifies every decrypted output for integrity and authenticity.
- Login ID-Based Mapping: Gentlemen ransom notes contain unique victim IDs. Our decryptor uses these to align with the correct encryption batch for accurate recovery.
- Universal Key Option: For cases where ransom notes are missing, we provide a Universal Decryptor that can handle updated variants of Gentlemen ransomware.
- Secure Execution: Our tool performs read-only scans first, preventing accidental data corruption before full decryption begins.
REQUIREMENTS
- A copy of the ransom note (commonly named gentlemen_readme.txt or equivalent)
- Access to encrypted files
- Stable internet connection (for cloud processing and integrity checks)
- Local or domain admin privileges
POWERSHELL AUDIT TOOLKIT
Execute the following script on suspect endpoints to identify Gentlemen compromise indicators:
# decryptors.org Audit Script for Gentlemen Variant
Write-Host "Initiating forensic sweep for Gentlemen IOCs..." -ForegroundColor DarkRed
# 1. Detect Files with Gentlemen Extensions
Get-ChildItem -Path C:\ -Recurse -Include "*.gentlemen","*.locked","*.gnlt","*.ojuopo" -ErrorAction SilentlyContinue -Depth 3 |
Group-Object { $_.Extension } |
Where-Object { $_.Count -gt 5 } |
ForEach-Object { Write-Host "Potential Gentlemen Cluster Detected: '$($_.Name)' affecting $($_.Count) files." }
# 2. Locate Ransom Notes
Get-ChildItem -Path C:\ -Filter 'gentlemen_readme.txt' -Recurse -Force -ErrorAction SilentlyContinue -Depth 3 |
Select-Object -First 100 FullName, LastWriteTimeUtc
# 3. Check for Suspicious Tools
Get-ChildItem -Path C:\ -Include "mimikatz.exe","lazagne.exe","anydesk.exe","rclone.exe","filezilla.exe" -Recurse -Force -ErrorAction SilentlyContinue |
Select-Object -First 50 FullName, LastWriteTimeUtcFREQUENTLY ASKED QUESTIONS
Q: Can Gentlemen ransomware files be decrypted for free?
A: Only older variants with weaker key derivation methods. Modern builds require professional help as they have addressed the cryptographic flaws present in early versions.
Q: Do I need the ransom note to decrypt?
A: While having the ransom note with the victim ID significantly improves decryption accuracy, our Universal Decryptor can handle cases where the note is missing by analyzing encryption patterns in the files themselves.
Q: How much does professional decryption cost?
A: Costs vary depending on the volume of data, variant complexity, and urgency. Contact our recovery specialists for a customized quote based on your specific situation.
Q: Does it work for Linux or ESXi servers?
A: Yes, our decryptor is compatible with Windows, Linux, and VMware ESXi platforms, making it suitable for heterogeneous enterprise environments.
Q: Is online recovery secure?
A: Absolutely. Our online recovery uses encrypted transfer protocols and blockchain verification to ensure the security and integrity of your data throughout the decryption process.
Q: Are there any other ransomware families that can be decrypted with your tools?
A: Our decryptor is specifically engineered for Gentlemen ransomware variants. Each ransomware family requires a custom approach based on its specific implementation and cryptographic flaws.
REQUEST EMERGENCY CONSULTATION
Active Gentlemen ransomware incidents demand immediate expert intervention. Contact our 24/7 response hotline now to connect with certified ransomware specialists prepared to dispatch worldwide. Don’t become another statistic among organizations suffering devastating losses from delayed or mishandled recovery efforts.