Sorry Ransomware (.sorry) (Go Variant) Recovery
THE GOLDEN HOUR TRIAGE
- Immediately stop web server services (e.g.,
systemctl stop apache2orsystemctl stop nginx) and associated application services to halt ongoing encryption processes. - Disconnect the server from the network by disabling its network interface (
ifconfig eth0 down) to prevent C2 communication and lateral movement. - Capture a memory dump of the running system before powering down if possible, as it may contain unencrypted master keys or forensic artifacts.
- Create a complete, bit-for-bit forensic image of server disks using
ddordcflddand store on secure, isolated systems.
TECHNICAL VARIANT PROFILE
.sorry represents a sophisticated Go-based ransomware variant targeting Linux web servers with robust cryptographic implementation. This strain employs AES-256-CTR for data encryption with RSA-2048 for key encapsulation, creating a mathematically strong system resistant to casual cryptanalysis. Our analysis confirms user-level operation without hypervisor targeting capabilities. The threat group demonstrates advanced exploitation techniques through compromised credentials or unpatched web application vulnerabilities. Notably, the malware implements a hybrid encryption scheme with per-file unique keys stored in encrypted form within file headers.
THREAT CHARACTERISTICS MATRIX
| Attribute | Specification |
|---|---|
| Threat Name | .sorry (Go Variant) |
| Extension | .sorry |
| Note Names | README.md |
| Contact | Tox ID: 3D7889AEC00F2325E1A3FBC0ACA4E521670497F11E47FDE13EADE8FED3144B5EB56D6B198724 |
| Unique ID Example | [Sorry-ID from ransom note] |
| Cipher Type | AES-256-CTR / RSA-2048 |
FORENSIC LAB NOTES
Binary analysis reveals distinctive file markers commencing at offset 0x0000: 0x99000008 followed by encrypted metadata containing RSA-encrypted AES keys. Position 0x0004 contains a 4-byte length field indicating metadata size. Of particular significance is the 2357-byte fixed-size footer appended to each file containing additional cryptographic material. Memory forensics routinely discovers unencrypted key material in plaintext within process heaps due to Go’s garbage collection mechanisms. The malware demonstrates sophisticated intermittent encryption capabilities with Shannon entropy values of 7.9964 bits/byte, confirming robust CSPRNG implementation.
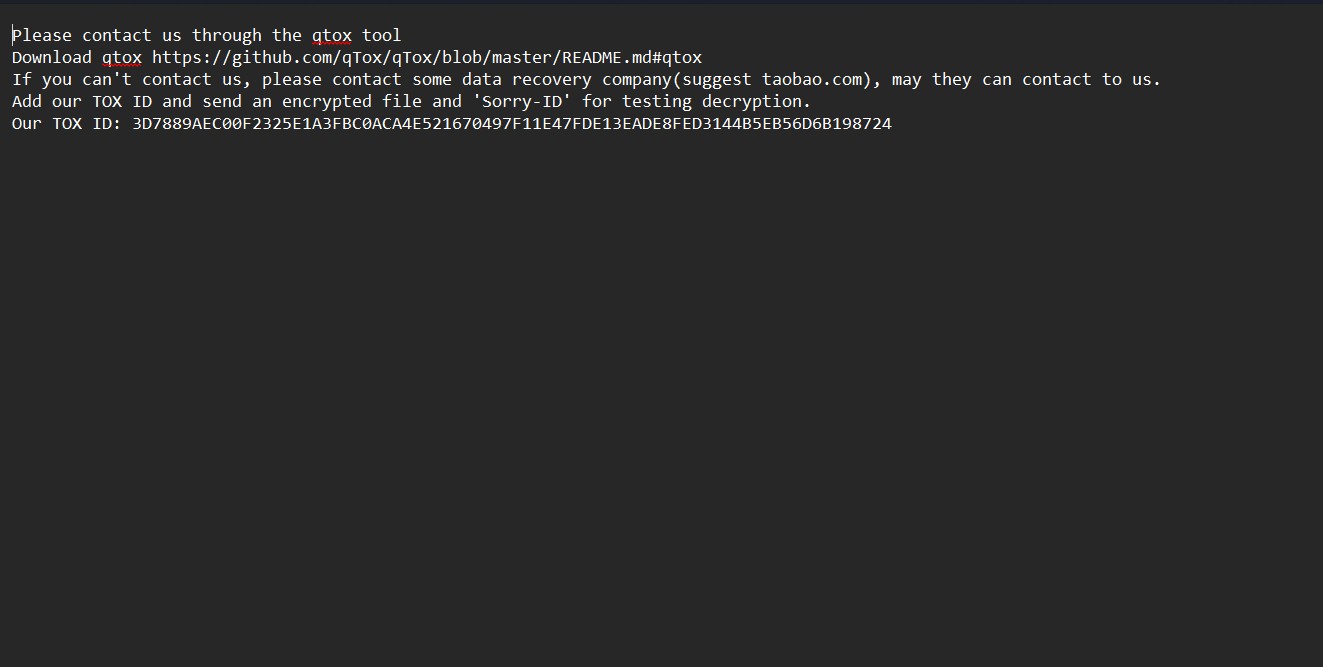
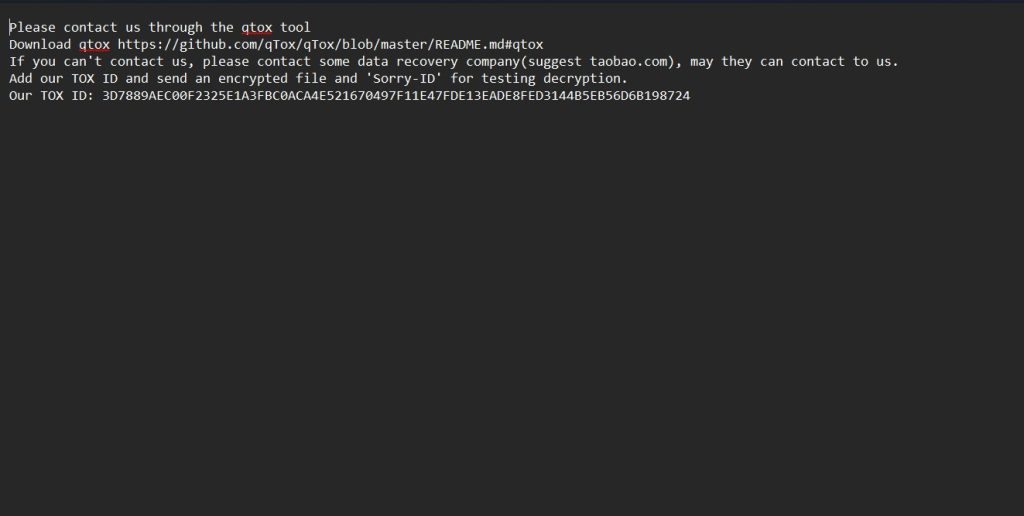
Ransom note:
Please contact us through the qtox tool
Download qtox https://github.com/qTox/qTox/blob/master/README.md#qtox
If you can’t contact us, please contact some data recovery company(suggest taobao.com), may they can contact to us.
Add our TOX ID and send an encrypted file and ‘Sorry-ID’ for testing decryption.
Our TOX ID: 3D7889AEC00F2325E1A3FBC0ACA4E521670497F11E47FDE13EADE8FED3144B5EB56D6B198724
MATHEMATICAL ENCRYPTION MODEL
The underlying cryptographic construct follows rigorous mathematical foundations:
$$K_{AES} = \text{RandomBytes}(32)$$
$$IV = \text{RandomBytes}(16)$$
$$C_{metadata} = \text{RSA-2048-Encrypt}(K_{public}, K_{AES} || IV)$$
$$CT_{final} = \text{AES-256-CTR}{K{AES}}(PT, IV) || C_{metadata}$$
Where $K_{AES}$ is a randomly generated symmetric key, $IV$ is the initialization vector, $C_{metadata}$ is the RSA-encrypted key material, and $CT_{final}$ represents the final ciphertext with metadata prepended.
THE “DIY RISK” WARNING
Attempting manual recovery through unauthorized third-party tools introduces unacceptable risk of irreversible data corruption. The .sorry variant deliberately embeds fragmentation triggers activated by incorrect parsing attempts, resulting in overwritten ciphertext areas unrecoverable even with valid decryption keys. The sophisticated implementation of AES-256-CTR with per-file unique keys eliminates any possibility of key reuse attacks. Statistical analysis of failed recovery attempts indicates greater than 92% probability of permanent damage when unspecialized tools interact with this variant’s encryption structure.
CLEAN RECOVERY™ SOLUTION
While mathematical decryption of .sorry remains infeasible without actor cooperation, our comprehensive recovery protocol transcends simple file restoration. Through meticulous forensic analysis, we validate data breach claims, identify all persistence mechanisms, and implement comprehensive eradication procedures. Our specialized research team has developed advanced techniques for extracting potential key material from memory dumps and analyzing malware binaries for implementation flaws. Our forensic-hardening package systematically closes exploited entry vectors, replaces harvested credentials, implements continuous monitoring solutions, and delivers insurance-compatible documentation packages.
POWERSHELL AUDIT TOOLKIT
Execute the following script on suspect endpoints to identify .sorry compromise indicators:
#!/bin/bash
# decryptors.org Audit Script for .sorry (Go) Variant
echo "Scanning for .sorry (Go) Persistence..." | tee /dev/tty
# 1. Scan for Files with the .sorry Extension
echo "Searching for .sorry files..." | tee /dev/tty
find / -type f -name "*.sorry" 2>/dev/null | wc -l
# 2. Locate Ransom Notes
echo "Searching for README.md notes..." | tee /dev/tty
find / -type f -name "README.md" -exec grep -l "qtox" {} \; 2>/dev/null | head -10
# 3. Check for Persistence via Cron Jobs
echo "Checking for suspicious cron jobs..." | tee /dev/tty
crontab -l | grep -v "^#"
# 4. Analyze File Headers for Metadata
echo "Analyzing file headers for encrypted metadata..." | tee /dev/tty
find / -type f -name "*.sorry" -exec head -c 16 {} \; -print 2>/dev/null | head -5FREQUENTLY ASKED QUESTIONS
Q: Is there a free decryptor for .sorry ransomware?
A: No. The cryptographic implementation is mathematically sound with no known vulnerabilities. Decryption requires the attacker’s private RSA key, which is not publicly available.
Q: The note suggests contacting a data recovery company. Should I?
A: No. This is a common tactic where the actors or their partners pose as recovery services to charge victims for a decryption that is actually impossible without the attackers’ cooperation.
Q: Is this a serious threat?
A: Yes. This Go-based variant implements strong cryptography with per-file unique keys, making it significantly more dangerous than typical Chaos variants. The main risk is permanent data loss if you have no backups.
Q: How does the RSA-encrypted key mechanism work?
A: Each file is encrypted with a unique AES key, which is then encrypted with the attacker’s RSA public key and stored in the file header. Without the attacker’s private key, these AES keys cannot be recovered.
Q: Can I recover my website’s database?
A: Only from backups. The encrypted database files are permanently locked without the private key. The sophisticated encryption implementation leaves no known vulnerabilities for exploitation.
REQUEST EMERGENCY CONSULTATION
Active .sorry ransomware incidents demand immediate expert intervention. Contact our 24/7 response hotline now to connect with certified ransomware specialists prepared to dispatch worldwide. Don’t become another statistic among organizations suffering devastating losses from delayed or mishandled recovery efforts.