Ameriwasted Ransomware Decryptor
The Ameriwasted ransomware family is a dangerous data-locking threat that renames encrypted files with the .ameriwasted suffix. After extensive research into its encryption routine, our team developed a specialized decryptor tailored for enterprises, government institutions, and healthcare networks. The tool supports Windows, Linux, and VMware ESXi, ensuring compatibility with mixed infrastructures while maintaining high speed, reliability, and data accuracy.
How Our Recovery Tool Works
Our decryption framework combines advanced AI-driven algorithms with blockchain verification to restore locked files. The system prevents corruption by ensuring every decrypted file is matched against blockchain-authenticated keys.
Victim Identifier Mapping: Each ransom note (such as [filename].ameriwasted_info) contains a unique victim ID. Our decryptor extracts and uses this value to align with the correct encryption instance.
Universal Mode: When ransom notes are missing or incomplete, our premium universal decryptor is able to handle newer Ameriwasted strains.
Non-Destructive Verification: Before unlocking any file, the tool performs a read-only analysis, guaranteeing that data integrity remains intact.
Requirements for Successful Recovery
Before initiating recovery, the following items must be available:
- At least one ransom note (.ameriwasted_info).
- Several encrypted files for analysis.
- Internet access for secure cloud-based decryption.
- Administrator privileges on the compromised system.
Immediate Response After Ameriwasted Infection
Responding quickly to an Ameriwasted intrusion can significantly affect the outcome of recovery efforts.
Isolate the Impacted Systems
Disconnect compromised endpoints from the network to prevent further file encryption.
Preserve All Digital Evidence
Retain ransom notes, locked files, and system logs. These are essential for both decryption and forensic investigation.
Do Not Reboot Systems
Restarting may execute leftover scripts that could expand the encryption.
Engage Professionals
Avoid unverified decryptors found online. Professional tools provide far greater chances of recovery and reduce the risk of permanent loss.
File Recovery from Ameriwasted Infections
Ameriwasted relies on robust encryption, making files inaccessible and renaming them with the .ameriwasted extension. Without access to decryption keys, recovery is impossible through conventional means. Our research into flaws in its encryption model, however, enables us to provide safe alternatives that eliminate the need for ransom payments.
Available Recovery Options for Ameriwasted Victims
Free Methods
Public Decryptors: If any are released, they usually target outdated or faulty Ameriwasted builds. Use with caution, as incorrect tools may damage files further.
Backup Restoration: The most secure method remains restoring from offline or cloud backups, provided they were stored beyond the ransomware’s reach. Validation of integrity should be completed before reinstating systems.
Virtual Snapshots: For virtualized setups like VMware or other hypervisors, pre-attack snapshots may be rolled back. This option is only viable if attackers have not removed or corrupted snapshot repositories.
Paid Recovery Solutions
Paying Threat Actors: While paying the ransom may deliver a decryptor, this path is unreliable. Many victims receive broken tools or malware-ridden decryptors, and in some jurisdictions, payments may carry legal implications.
Third-Party Negotiators: Some companies hire negotiators to deal directly with attackers. Negotiators may reduce ransom demands and test decryptors before purchase, though this method can be expensive and time-consuming.
Our Proprietary Ameriwasted Decryptor: Unlike attacker-issued tools, our decryptor is engineered for controlled recovery. Using victim IDs or blockchain-stored universal keys, it restores encrypted files within a secured environment, ensuring no hidden backdoors remain.
Step-by-Step Guide: Using Our Ameriwasted Decryptor
Our software is designed to deliver a safe and structured recovery. Follow these steps:
1. Collect the Necessary Files
Have at least one ransom note ([filename].ameriwasted_info) and a few encrypted files. Do not alter or rename them.
2. Prepare the System
Remove the device from all networks. Confirm administrator access. End any suspicious background tasks that may continue encryption.
3. Launch the Tool
Run the decryptor with administrative rights. Load both ransom note(s) and encrypted files into the interface.
4. Victim ID Analysis
The software extracts the unique identifier embedded in ransom notes and cross-references it with our key servers.
5. Controlled Decryption
After a read-only assessment, the system decrypts files and restores them securely.
6. Review and Save
Recovered files are placed back into their original directories. A detailed audit log is generated for proof of integrity.
7. Post-Recovery Security
Run a complete antivirus sweep. Secure all backups offline. Apply security updates to block reinfection attempts.
Ameriwasted Ransom Note & Infection Traits
Each encrypted file is paired with a ransom note ending in .ameriwasted_info. These notes explain the encryption and provide attacker contact addresses — [email protected] and [email protected]. They warn against renaming or moving files.
A typical ransom note reads:
–
YOUR NETWORK IS ENCRYPTED NOW
USE [email protected] | [email protected] TO GET THE PRICE FOR YOUR DATA
DO NOT GIVE THIS EMAIL TO 3RD PARTIES
DO NOT RENAME OR MOVE THE FILE
THE FILE IS ENCRYPTED WITH THE FOLLOWING KEY:
–
KEEP IT
Indicators of Compromise (IOCs)
- File Extensions: .ameriwasted
- Ransom Notes: [filename].ameriwasted_info
- Attacker Emails: [email protected], [email protected]
- AV Detections:
- Microsoft: Ransom:Win32/WastedLocker.MA!MTB
- Kaspersky: Trojan.Win32.Qshell.wad
- ESET: Variant Of Win32/Kryptik.HFDU
- Avast: Win32:DangerousSig [Trj]
- Microsoft: Ransom:Win32/WastedLocker.MA!MTB
Tactics, Techniques, and Procedures (TTPs)
Ameriwasted attackers employ techniques common across modern ransomware:
- Initial Access: Through phishing campaigns, drive-by downloads, malicious ads, or trojans.
- Execution: Encrypting files with asymmetric cryptography to lock out victims.
- Persistence: Propagation across local networks and removable media.
- Defense Evasion: Disabling recovery tools and shadow copies to block rollback.
- Impact: Total denial of access to files with ransom demands for restoration.
Tools and Methods Exploited with Ameriwasted
- Credential Harvesters: Password-stealing trojans often accompany the payload.
- Exploit Kits: Delivered via malicious advertisements or compromised websites.
- Fake Software Updates: Users are tricked into installing ransomware disguised as patches or installers.
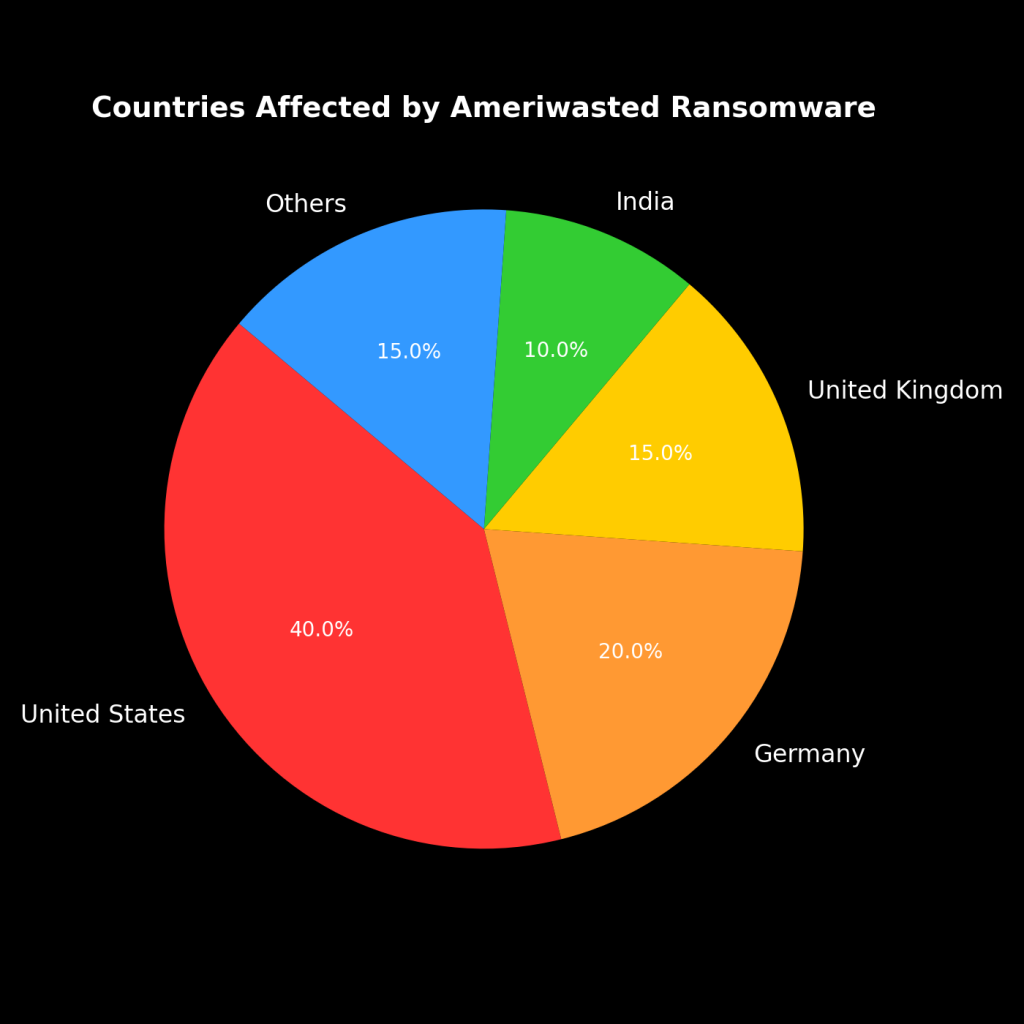
Ameriwasted Global Impact and Victim Data
Countries Most Affected
Targeted Organizations
Timeline of Attacks
Preventing Future Ameriwasted Incidents
Defense against Ameriwasted requires layered cybersecurity. Organizations should:
- Implement multi-factor authentication.
- Disable unnecessary RDP and VPN access.
- Apply security patches quickly.
- Use immutable, offline backup solutions.
- Monitor networks with SOC/MDR solutions for anomalies.
Conclusion
Ameriwasted ransomware is designed to cause maximum disruption by encrypting files and demanding ransom. Paying attackers only fuels their operations and carries no guarantee of recovery. With the right combination of backups, expert decryptors, and proactive security, victims can regain access safely and reduce future risks.
MedusaLocker Ransomware Versions We Decrypt