Gentlemen Ransomware Decryptor
Our cybersecurity team has reverse-engineered critical components of the Gentlemen ransomware encryption process. Using proprietary AI-driven algorithms and blockchain verification, our decryptor has helped organizations across finance, healthcare, logistics, and government sectors recover encrypted data without paying ransom.
Compatible with Windows, Linux, and VMware ESXi, the decryptor is designed for reliability, speed, and accuracy.
How It Works
- AI + Blockchain Analysis
Encrypted files are processed in a secure, isolated environment where AI identifies encryption patterns. A private blockchain ledger verifies every decrypted output for integrity and authenticity. - Login ID-Based Mapping
Gentlemen ransom notes contain unique victim IDs. Our decryptor uses these to align with the correct encryption batch for accurate recovery. - Universal Key Option
For cases where ransom notes are missing, we provide a Universal Decryptor that can handle updated variants of Gentlemen ransomware. - Secure Execution
Our tool performs read-only scans first, preventing accidental data corruption before full decryption begins.
Requirements
To use our decryptor, you will need:
- A copy of the ransom note (gentlemen_readme.txt or equivalent).
- Access to encrypted files.
- Stable internet connection (for cloud processing and integrity checks).
- Local or domain admin privileges.
Immediate Steps to Take After Gentlemen Ransomware Attack
- Disconnect Immediately – Isolate compromised systems to stop ransomware spread.
- Preserve Everything – Do not delete ransom notes or encrypted files.
- Shut Down Affected Systems – Avoid reboots; Gentlemen persistence scripts can re-trigger.
- Contact a Recovery Expert – DIY attempts risk corruption.
How to Decrypt Gentlemen Ransomware and Recover Your Data
Gentlemen ransomware has rapidly evolved since its emergence in mid-2023. Our specialized decryptor leverages cryptographic flaws and timestamp analysis to restore files safely, without ransom payment.
Gentlemen Decryption and Recovery Options
Free Methods
- Open-Source Decryptors – For older variants with weaker encryption.
- Backup Restore – Safest method if clean backups exist.
- VM Snapshots – Quick restore for virtualized environments.
- GPU Brute Force Attempts – Sometimes feasible for older builds.
Paid Methods
- Paying the Ransom – Risky, no guarantees, may be illegal.
- Third-Party Negotiators – Costly and slow.
Our Specialized Gentlemen Ransomware Decryptor
Optimized for 2025 variants, supporting:
- Reverse Engineering of leaked samples.
- Cloud Decryption with full integrity logs.
- Fraud Prevention with verified recovery cases.
Step-by-Step Gentlemen Recovery Guide
- Assess the Infection – Confirm extensions (.gentlemen, .locked, .gnlt).
- Secure the Environment – Disconnect and remove persistence.
- Submit Samples – Ransom note + encrypted files.
- Run Decryptor – Start recovery with correct victim ID.
Offline vs Online Recovery
- Offline Recovery – Air-gapped, for sensitive/government systems.
- Online Recovery – Faster, cloud-audited with blockchain verification.
What is The Gentlemen Ransomware?
- First observed: late 2023.
- Type: Ransomware-as-a-Service (RaaS).
- Tactics: Double extortion (data theft + encryption).
- Targets: High-value corporate networks.
How Gentlemen Works: Inside Look
Initial Access Vectors
- VPN brute force (Cisco/Fortinet).
- Exploiting CVEs (Fortinet, MOVEit).
- Phishing campaigns.
- RDP exploitation.
Tools, TTPs & MITRE Mapping
- Credential Theft: Mimikatz, LaZagne (T1003).
- Reconnaissance: AdFind, SoftPerfect (T1018).
- Defense Evasion: BYOVD, rootkits (T1562).
- Data Exfiltration: RClone, WinSCP, Ngrok (T1048).
- Encryption: ChaCha20 + RSA; shadow copy deletion.
Known Indicators of Compromise (IOCs)
- File Extensions: .gentlemen, .locked, .gnlt.
- Ransom Note: gentlemen_readme.txt.
- Suspicious Tools: Mimikatz, AnyDesk, RClone.
- Outbound Traffic: Mega.nz, Ngrok.io, TOR C2 servers.
Mitigations & Best Practices
- Enforce MFA on VPN/RDP.
- Patch firewalls and transfer software.
- Network segmentation.
- Block BYOVD exploits.
- Invest in MDR/SOC monitoring.
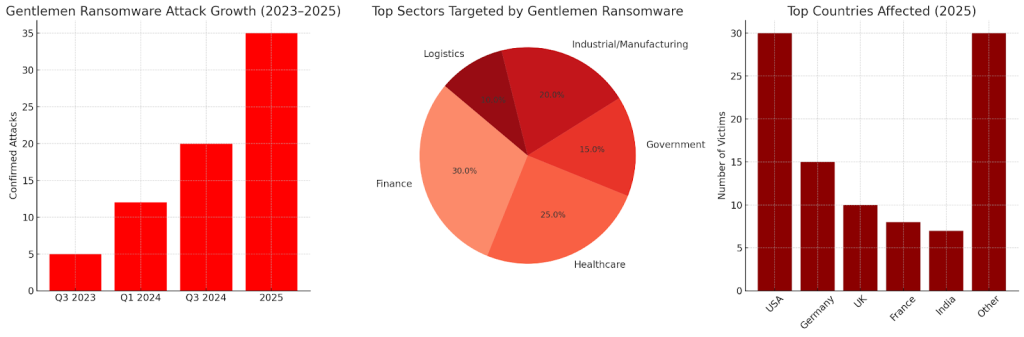
Victim Stats and Data
Timeline Growth (2023–2025)
Timeline Growth (2023–2025)
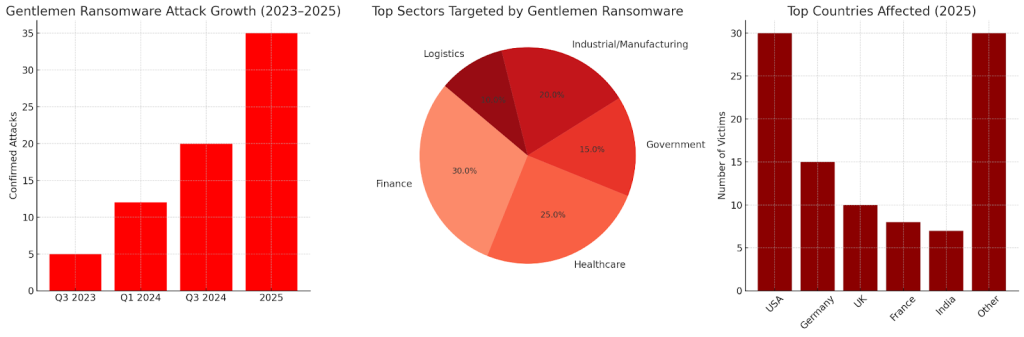
Targeted Sectors
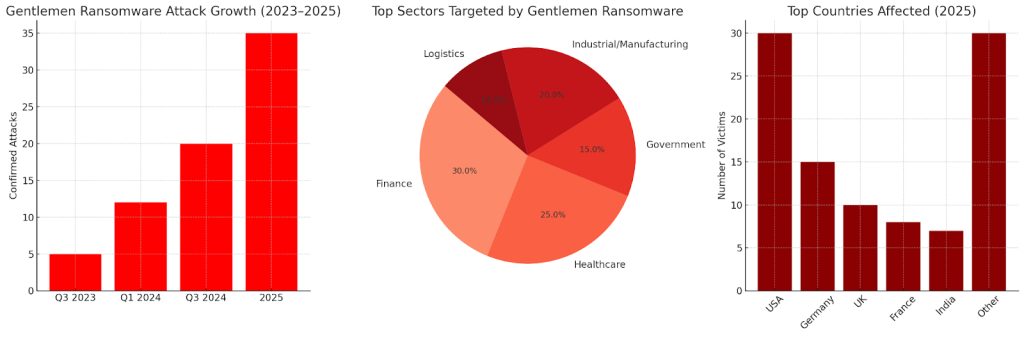
Top Countries Impacted (2025)
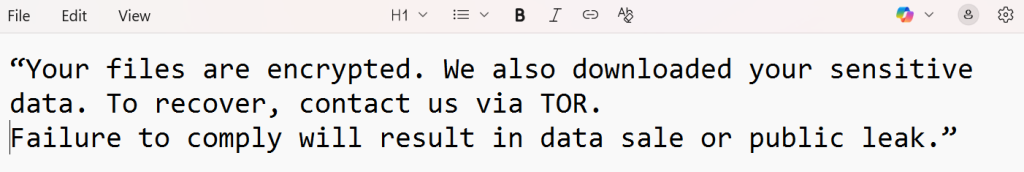
Gentlemen Ransom Note
“Your files are encrypted. We also downloaded your sensitive data. To recover, contact us via TOR.
Failure to comply will result in data sale or public leak.”
Conclusion
Gentlemen ransomware is a fast-evolving, high-impact RaaS threat. Paying ransom fuels crime and carries no guarantees.
Our Gentlemen Decryptor has already restored encrypted files for dozens of enterprises across Windows, Linux, and ESXi — safely, quickly, and without ransom payments.
MedusaLocker Ransomware Versions We Decrypt