LockBit 3.0 Black Ransomware Decryptor
Our response engineers maintain a bespoke decryptor and workflow tailored to LockBit 3.0 Black—the modern evolution of the LockBit RaaS ecosystem. This strain encrypts files with a hybrid AES-256 + RSA-2048 scheme and tags each item with a random 9-character extension (for example, .3R9qG8i3Z). Ransom notes mirror that token (e.g., 3R9qG8i3Z.README.txt) to bind your case to a unique ID.
The decryptor is designed to:
- Safely analyze encrypted samples inside an isolated sandbox,
- Detect variant-specific markers and the per-victim token, and
- Restore data through a tightly logged, verifiable decryption process.
It’s available in both cloud-assisted and offline/air-gapped modes and always starts in read-only validation to protect evidence.
How the Decryptor Works
After you provide sample encrypted files and the ransom note, our tooling fingerprints the payload—matching headers, the 9-char scheme, and crypto structure against our case library. If it aligns with a supported pattern or a workable weakness, we perform a Proof-of-Concept (PoC) decrypt on a small file set. Once validated, we proceed to full restoration under analyst supervision while generating integrity logs for insurance and legal use.
Requirements:
- Ransom note like 3R9qG8i3Z.README.txt
- 2–5 encrypted samples with the random 9-char extension
- Admin privileges on a clean recovery host
- Optional connectivity for cloud key checks
Immediate Response Checklist
- Isolate endpoints from LAN/Wi-Fi/VPN and unmount shared or backup volumes.
- Preserve artifacts (encrypted files + notes) exactly as found—no renaming or edits.
- Collect evidence: EDR/AV alerts, Windows Event Logs, firewall/proxy telemetry, suspicious executables.
- Capture RAM, if possible—some campaigns leave ephemeral material in memory.
- Engage a professional team; avoid contacting the actor’s Telegram or links yourself.
Recovery Paths
Free / Standard
Backups — Restore from offline or immutable copies after checksum validation.
Public tools — No free decryptor exists for LockBit 3.0 at the moment. Keep an eye on No More Ransom for future releases if a cryptographic flaw is published.
Specialist
Forensic decryptor service — We start with PoC decrypts, then scale up with full chain-of-custody logging.
Paying the ransom (not recommended) — Even small demands (e.g., the “Mr.Robot” note asks ~$45) don’t ensure reliable keys or prevent leaks; consult counsel and your insurer before any decision.
How to Use Our Decryptor — Step-by-Step
Assess the Infection — Confirm the random 9-character extension (e.g., .3R9qG8i3Z) and the matching README.txt.
Secure the Environment — Disconnect affected systems and block cloud/drive syncs.
Engage Our Team — Upload the note and a few samples via our secure intake; we’ll provide a timeline.
Run the Decryptor — Execute with admin rights; cloud checks are optional if you prefer offline mode.
Enter the Victim/Decryption ID — Copy the 32-hex ID from the note to bind your session.
Start Recovery — The tool restores files to a clean target path and produces integrity + completion logs.
Understanding LockBit 3.0 Black
Profile — A modular RaaS platform known for rapid updates, broad affiliate use, and layered extortion.
“PC Locker 3.0 by Mr.Robot” — A branded variant that borrows LockBit’s playbook, adds low-entry ransoms and “mentorship” marketing, and uses Telegram for contact.
Behavior — Encrypts documents, DBs, images, configs; deletes shadow copies; disables recovery; and often conducts exfiltration to enable double/triple extortion.
Ransom Note
Typical name: 3R9qG8i3Z.README.txt
Distribution: Dropped in each encrypted folder.
Excerpt from the Ransom Note:
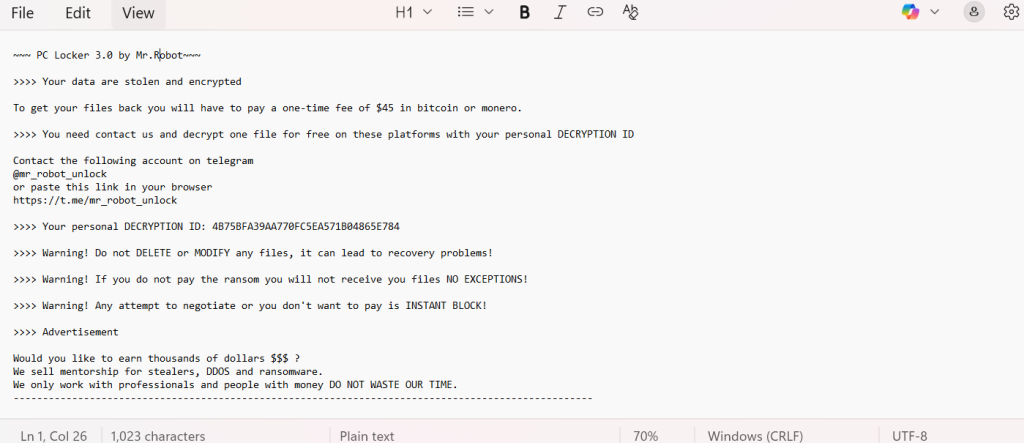
~~~ PC Locker 3.0 by Mr.Robot~~~
>>>> Your data are stolen and encrypted
To get your files back you will have to pay a one-time fee of $45 in bitcoin or monero.
>>>> You need contact us and decrypt one file for free on these platforms with your personal DECRYPTION ID
Contact the following account on telegram
@mr_robot_unlock
or paste this link in your browser
>>>> Your personal DECRYPTION ID: 4B75BFA39AA770FC5EA571B04865E784
>>>> Warning! Do not DELETE or MODIFY any files, it can lead to recovery problems!
>>>> Warning! If you do not pay the ransom you will not receive you files NO EXCEPTIONS!
>>>> Warning! Any attempt to negotiate or you don’t want to pay is INSTANT BLOCK!
>>>> Advertisement
Would you like to earn thousands of dollars $$$ ?
We sell mentorship for stealers, DDOS and ransomware.
We only work with professionals and people with money DO NOT WASTE OUR TIME.
—————————————————————————————————
IOCs, Detections & Technical Indicators
Name: LockBit 3.0 Black (aka PC Locker 3.0 by Mr.Robot)
Extension: 9-character random suffix (e.g., .3R9qG8i3Z)
Ransom note: [random9].README.txt
Encryption: AES-256 + RSA-2048
Example ID: 4B75BFA39AA770FC5EA571B04865E784
Detections (examples):
- ESET — Win64/Filecoder.Lockbit.Black
- Kaspersky — Trojan-Ransom.Win32.LockBit3.gen
- Bitdefender — Gen:Heur.Ransom.LockBit3.0
- Microsoft — Ransom:Win64/LockBitBlack.A!MTB
Common Indicators:
- Shadow copy deletion / recovery disabled
- Notes bearing “PC Locker 3.0 by Mr.Robot”
- Telegram handle @mr_robot_unlock present in the note
- Suspicious binaries under user/Temp paths
TTPs (MITRE-aligned)
- Initial Access: Phishing, trojanized installers, stolen credentials/RDP.
- Execution: AES/RSA file encryption; mass renaming with 9-char suffix.
- Persistence: Registry/startup modifications.
- Exfiltration: Staging and upload of sensitive data prior to encryption.
- Impact: Encryption + extortion; possible DDoS pressure for non-payment.
Victim Landscape — Regions, Sectors & Timeline
Regions: Sectors:
Timeline:
Conclusion
LockBit 3.0 Black fuses robust encryption with relentless extortion, and the “PC Locker 3.0 by Mr.Robot” spin underscores how affiliates tailor tactics to widen their reach. Even when a ransom appears small, paying rarely guarantees safe or complete restoration and can expose an organization to ongoing pressure. The most reliable path forward is disciplined incident handling: isolate systems at once, preserve evidence, lean on verified PoC-based decryption or clean backups, and strengthen long-term resilience with layered identity controls, tight RDP posture, continuous monitoring, and offline or immutable backups. Acting early and methodically is the difference between a contained incident and a protracted operational crisis.
MedusaLocker Ransomware Versions We Decrypt