LockBit Black Ransomware Decryptor
Our LockBit Black Decryptor: Precision Recovery, Expertly Built
Our cybersecurity researchers have been monitoring the LockBit Black strain (also recognized as LockBit 3.0) and its latest extension .dzxn0liBX. Since LockBit operates under a Ransomware-as-a-Service (RaaS) model, affiliates distribute customized payloads, each with its own extension. Over time, we’ve created proven recovery frameworks that have successfully restored data for organizations worldwide, spanning Windows, Linux, and VMware ESXi environments.
Our recovery platform is engineered with accuracy, speed, and dependability to address every LockBit Black variant with maximum efficiency.
How the Decryption Process Works
- AI & Blockchain Validation: Files are decrypted in a secure cloud infrastructure. Blockchain verification ensures file integrity and prevents tampering post-recovery.
- Victim ID Matching: Every ransom note includes a victim-specific identifier. Our tools align this ID with the corresponding encryption set, helping us determine available decryption routes.
- Universal Key Access (When Applicable): Some LockBit builds may be covered by previously leaked decryption keys from global law enforcement actions. Our solution automatically tests these universal recovery options when possible.
- Protected Execution: Initial scans run in read-only mode, reducing any risk of file corruption during the recovery phase.
Requirements Before Decryption
To start recovery, you’ll need:
- A copy of the ransom note (README.txt or the LockBit-specific variant).
- The encrypted files that end with the .dzxn0liBX extension.
- A stable internet connection for cloud-assisted decryption.
- Administrator access to the affected system(s).
Immediate Response to a LockBit Black Attack
1. Disconnect Affected Systems
Immediately cut infected devices off from networks to stop ransomware propagation to servers, shared drives, or backup repositories.
2. Preserve All Evidence
Retain encrypted files, ransom notes, system logs, network captures, and file hashes for forensics. Avoid deleting anything prematurely.
3. Do Not Reboot
Refrain from restarting compromised machines. Some LockBit variants trigger additional encryption processes on reboot.
4. Contact a Recovery Specialist
Avoid unverified “free decryptors” from forums, as many are fraudulent or unsafe. Work only with established professionals to maximize successful restoration.
Decrypting LockBit Black .dzxn0liBX Files and Data Restoration
LockBit Black continues to rank among the most dangerous ransomware families globally. It integrates advanced obfuscation techniques, uses unique extensions like .dzxn0liBX, and employs extremely fast encryption. Our custom decryptor and workflows aim to restore files without paying attackers, whenever feasible.
LockBit Black Decryption and Recovery Options
Free Options
1. No More Ransom Project
- How it works: Past operations have released decryption keys seized from LockBit infrastructure. If your strain is included, recovery is possible at no cost.
- Drawbacks: Coverage is limited to earlier variants. Extensions such as .dzxn0liBX may not yet be available.
- Safety: Tools can be run locally and offline, making them safe to attempt first.
2. Restoring from Backups
- Method: The most reliable approach is restoring data from pre-attack backups.
- Validation: Always verify backup integrity using checksums, since some ransomware campaigns partially corrupt backup data.
- Immutable Systems: Backups stored in WORM systems or secure cloud snapshots drastically improve chances of recovery.
3. Leveraging Virtual Machine Snapshots
- How it works: If hypervisor snapshots (VMware ESXi, Proxmox, Hyper-V) are intact, rollback is possible.
- Precaution: Ensure snapshots were not deleted, altered, or corrupted before initiating restore.
Paid Options
Paying the Ransom (Not Recommended)
- How it works: Attackers issue a decryptor linked to your victim ID.
- Risks: Provided tools can be buggy, incomplete, or backdoored.
- Legal Implications: Payments may breach local regulations and directly fund cybercrime.
Third-Party Negotiators
- Function: Intermediaries negotiate directly with LockBit affiliates.
- Process: They typically request proof of successful decryption before recommending payment.
- Costs: Negotiators often charge high fees, sometimes as a share of the ransom amount.
Our Custom LockBit Black .dzxn0liBX Decryptor
We’ve designed proprietary utilities, leveraging reverse-engineering, leaked keys, and AI-powered cloud systems to recover files securely.
Key Features
- Reverse-Engineered Decryption: Developed from in-depth analysis of LockBit 3.0 cryptographic processes.
- Cloud-Based Recovery: Files are decrypted in sandboxed environments for maximum safety.
- Fraud Protection: Every decryption process undergoes validation to protect against counterfeit or malicious tools.
Step-by-Step LockBit Black Recovery
- Confirm Infection: Ensure files carry the .dzxn0liBX extension.
- Isolate Systems: Disconnect to prevent lateral spread.
- Submit Evidence: Provide ransom note + encrypted file samples.
- Run Decryptor: Execute tool with admin rights (internet required).
- Victim ID Entry: Input victim ID extracted from ransom note.
- Begin Recovery: Files are restored with original names and structures.
Offline vs. Online Decryption Options
- Offline Recovery: Designed for air-gapped systems, where recovery is handled with external drives.
- Online Recovery: Faster process, supported by experts, with blockchain-based verification ensuring file integrity.
Our solution supports both methods, making it flexible for enterprises and government entities.
What is LockBit Black .dzxn0liBX?
LockBit Black is a highly advanced RaaS platform, delivered globally through affiliates.
- Frequently uses randomized extensions such as .dzxn0liBX.
- Deletes shadow copies and disables built-in recovery functions.
- Employs double extortion tactics: data is both encrypted and leaked if ransom is unpaid.
- Notorious for its rapid encryption speed and modular affiliate-driven model.
Connection to Conti and Other Ransomware Groups
LockBit has frequently been linked to groups from the Conti and BlackMatter networks. Affiliates often exchange playbooks, infrastructure, and tactics.
- Shares operational DNA with previous RaaS families.
- Competes with other major ransomware actors like Royal, BlackBasta, Snatch, and BlackByte.
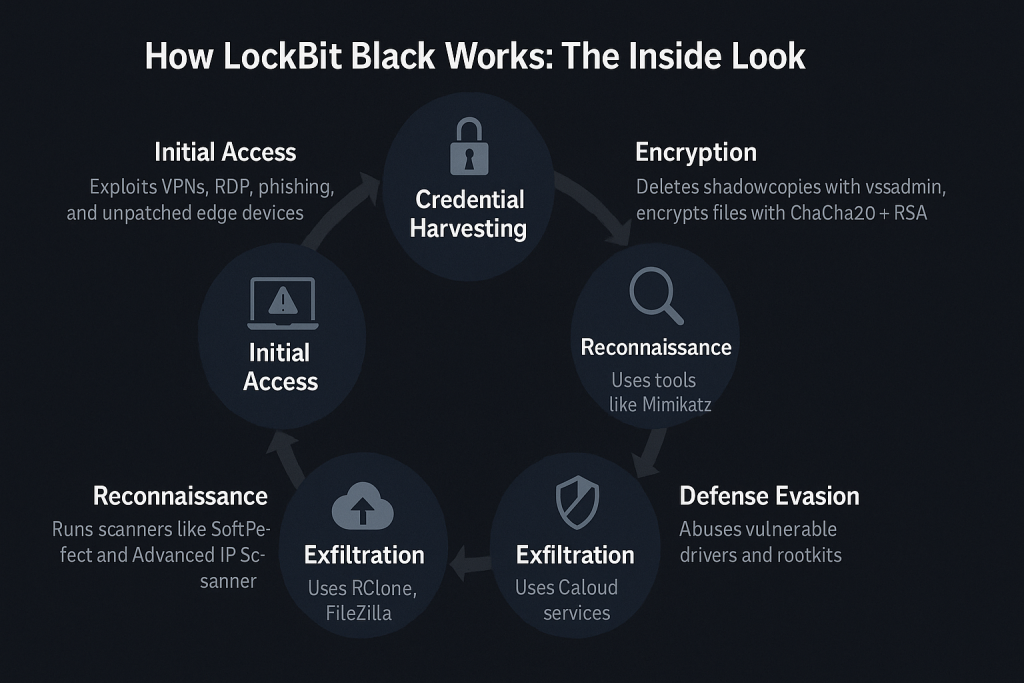
How LockBit Black Operates: Technical Overview
- Entry Point: Exploits weak VPNs, RDP credentials, phishing campaigns, and unpatched systems.
- Credential Harvesting: Relies on tools like Mimikatz and LaZagne.
- Reconnaissance: Uses scanning utilities such as SoftPerfect and Advanced IP Scanner.
- Defense Evasion: Deploys rootkits and vulnerable drivers to avoid detection.
- Exfiltration: Extracts data with RClone, FileZilla, or cloud services.
- Encryption Mechanism: Deletes shadow copies using vssadmin, encrypts files with a ChaCha20 + RSA hybrid scheme.
Indicators of Compromise (IOCs) for LockBit Black .dzxn0liBX
- File Extension: .dzxn0liBX
- Ransom Notes: README.txt, HOW_TO_DECRYPT.txt
- Artifacts: Custom wallpaper, dropped .ico files tied to the extension
- Commands: vssadmin delete shadows, bcdedit /set {default} recoveryenabled no
- Attack Tools: Mimikatz, AnyDesk, RClone
Mitigation Strategies & Best Practices
- Enforce MFA for VPN, RDP, and privileged accounts.
- Apply critical patches to address known vulnerabilities.
- Use network segmentation to contain ransomware outbreaks.
- Maintain immutable, offline backups.
- Deploy 24/7 monitoring using SOC or MDR solutions.
Inside the Ransom Note
LockBit Black ransom notes usually contain:
- Confirmation that files were encrypted with an extension like .dzxn0liBX.
- Instructions to contact operators through TOR.
- Threats of publishing stolen data if the ransom isn’t paid.
Conclusion
The .dzxn0liBX variant of LockBit Black demonstrates how adaptable this ransomware family has become. Recovery remains difficult, but with professional decryption, verified backups, and coordinated law enforcement support, organizations can regain control without resorting to ransom payments.
MedusaLocker Ransomware Versions We Decrypt