Radiant Group Ransomware Decryptor
Our digital forensics and incident response division has built a specialized decryptor for the Radiant Group ransomware, a sophisticated crypto-extortion operation that first appeared in September 2025. The Radiant syndicate uses an advanced AES and RSA hybrid encryption model combined with multi-layered extortion tactics, including public data leaks and SEO sabotage.
The decryptor is designed to perform three critical functions:
- Conduct a secure forensic analysis of encrypted samples in a contained sandbox;
- Identify the precise Radiant variant, including its unique encryption fingerprint and victim identifiers; and
- Recover files using a verified and logged decryption process that preserves evidence integrity and compliance standards.
This recovery tool is available for both cloud-integrated operations (for speed and scalability) and offline/air-gapped environments (for regulated industries). Each decryption session begins with read-only data validation to ensure no accidental alteration of forensic artifacts.
How the Radiant Decryptor Operates
Once victims provide ransom notes and encrypted file samples, the decryptor executes a structured fingerprinting process. It analyzes encryption headers, file signatures, and key-generation logic derived from Radiant’s AES+RSA hybrid architecture. After the encryption pattern is identified, a Proof-of-Concept (PoC) decryption is conducted on a small sample set.
If the sample decrypts successfully, a complete data restoration is performed under strict analyst supervision. Throughout the process, the system generates integrity logs and compliance reports suitable for insurance claims or legal documentation.
Requirements for Decryption:
- A ransom note or communication file (often containing the TOR site or contact channel)
- 2–5 encrypted file copies with matching metadata
- Administrative access on the recovery workstation
- Optional internet connectivity for cloud verification (offline mode supported)
Immediate Steps Following a Radiant Ransomware Attack
1. Isolate compromised assets. Disconnect affected systems from the network, disable VPNs, and cut shared-drive connections to prevent lateral spread.
2. Preserve all encrypted data. Do not modify, rename, or delete files — these may contain key metadata needed for decryption.
3. Capture volatile memory and logs. RAM dumps, proxy logs, and event files can reveal traces of encryption activity or network-based key exchanges.
4. Avoid contacting the threat actors directly. Radiant typically communicates via Tox ID or TOR-based portals; refrain from engaging without professional assistance.
5. Contact a professional response team. Forensics experts can help secure evidence and safely manage communication or recovery efforts.
File Recovery & Restoration Options
Free Options
Backup Recovery:
Offline or immutable backups remain the most reliable recovery source. Verify integrity by checksum comparison or secure mounting, as Radiant frequently deletes shadow copies and corrupts connected drives.
Virtual Snapshot Rollback:
If hypervisor snapshots (VMware, Hyper-V, etc.) exist, revert to the latest unaffected snapshot. Confirm that the ransomware has not altered or encrypted the image before use.
Paid or Specialist-Assisted Solutions
Forensic Decryptor Service:
Our decryption specialists begin with a small-scale PoC test to validate decryption compatibility, followed by full restoration with continuous monitoring and detailed documentation.
Ransom Payment (not advised):
Although some victims may choose to pay, there is no guarantee of receiving functional decryption keys or preventing data leaks. Payment also carries potential legal and ethical risks. Always seek legal counsel and insurer approval before considering this step.
How to Use Our Radiant Decryptor — Step-by-Step
Assess the Infection
Check for encrypted files and ransom notes referencing Radiant Group, typically containing TOR links such as
http://trfqksm6peaeyz4q6egxbij5n2ih6zrg65of4kwasrejc7hnw2jtxryd.onion.
Secure the Environment
Disconnect infected endpoints from the network, remove shared-drive connections, and disable RDP sessions.
Engage Our Response Team
Submit ransom notes and encrypted samples via our secure intake. We analyze the data, identify the variant, and estimate recovery timeframes.
Run the Radiant Decryptor
Execute the decryptor as an administrator. Cloud verification is optional — offline toolkits are available for air-gapped systems.
Enter Victim ID
Each ransom note includes a unique case identifier (for example, FCE5078C3A0A2609DB79C4F1516DA0B11A6F48FC96C9E01BAC0D48A4DDB2A309F20DD0D295B2). Enter this token to authenticate your recovery session.
Start the Decryption Process
Begin the restoration and allow the decryptor to recover files systematically. Progress logs and verification summaries will be generated automatically.
Understanding Radiant Group Ransomware
Overview
Radiant Group is an active ransomware-as-a-service (RaaS) operation that emerged in September 2025, employing both crypto-ransomware and data extortion. Its campaigns focus on encrypting business-critical systems and publicly exposing sensitive data through leak sites to amplify ransom pressure.
Encryption Scheme
Radiant uses AES-256 for local encryption and RSA-2048 to secure keys, creating robust encryption resistant to brute-force attacks.
Extortion Model
Radiant is known for multi-vector extortion, including direct ransoms, data leaks, and public shaming. The group also engages in SEO manipulation and regulatory complaints to damage corporate reputation and investor confidence.
Extortion and Leak Infrastructure:
- TOR Site: http://trfqksm6peaeyz4q6egxbij5n2ih6zrg65of4kwasrejc7hnw2jtxryd.onion
- Tox Contact ID: FCE5078C3A0A2609DB79C4F1516DA0B11A6F48FC96C9E01BAC0D48A4DDB2A309F20DD0D295B2
- Known Victim: Education sector, United Kingdom (Extortion date: September 24, 2025)
IOCs, Detection Names & Technical Artifacts
File Behavior and Extensions
Encrypted files may end with .locked, .radiant, or custom alphanumeric tags. Notes are typically text or HTML files containing TOR addresses and Tox identifiers.
Detections Reported by Vendors:
- BitDefender → Gen:Variant.Ransom.Radiant.A
- ESET → MSIL/Filecoder.HiddenTear.Radiant
- Kaspersky → Trojan-Ransom.Win32.RadiantGroup.gen
- Microsoft → Ransom:Win64/RadiantCrypt.A!MTB
Common Indicators of Compromise:
- Ransom note with Radiant branding and TOR URLs
- Exfiltration of sensitive company data before encryption
- Evidence of remote access via compromised RDP credentials
- Log tampering or deletion of Windows event files
Tactics, Techniques & Procedures (TTPs)
- Initial Access: Credential theft via phishing, brute-forced RDP, or compromised supply-chain accounts.
- Execution: AES+RSA encryption deployment through scheduled scripts or PowerShell.
- Persistence: Startup registry modification and malicious service installation.
- Defense Evasion: System restore and shadow copy removal, antivirus termination, and event log deletion.
- Exfiltration: Theft of financial records, HR data, and customer databases to remote TOR servers.
- Impact: Encryption of critical systems followed by public data leaks to pressure payment.
Victim Landscape — Reach & Industry Focus
Geographic Distribution:
Industries Affected:
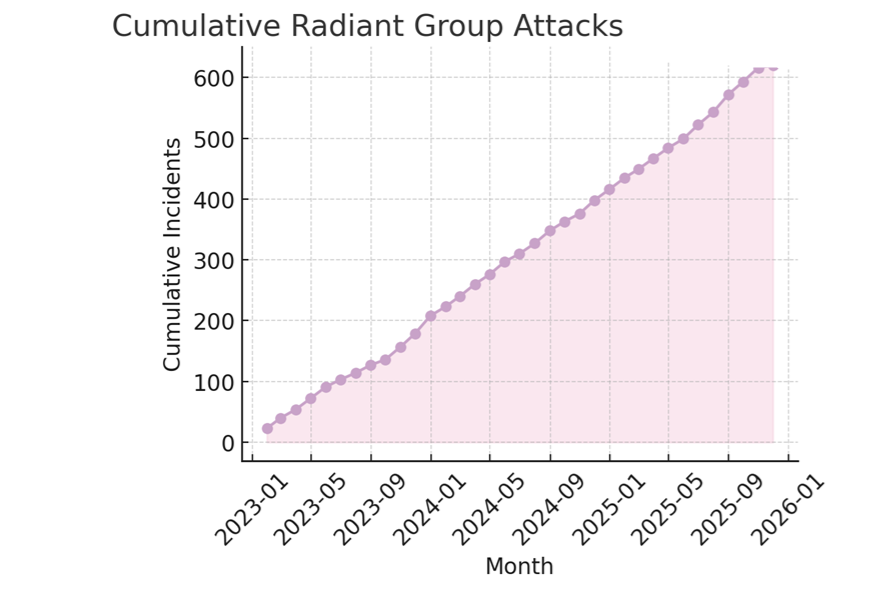
Activity Timeline:
Conclusion
Radiant Group ransomware has proven to be one of the most adaptive and damaging crypto-extortion operations of 2025, combining strong AES/RSA encryption with aggressive double-extortion tactics that extend beyond technical compromise to reputation and regulatory exposure. The group’s coordinated use of data theft, leak sites, and SEO manipulation makes it a multifaceted threat that requires both technical and legal containment strategies. Organizations should immediately isolate infected systems, collect evidence, and engage verified decryption professionals for recovery. Long-term protection depends on maintaining up-to-date patches, strict RDP security, multifactor authentication, and resilient offline backup infrastructure to prevent reinfection and minimize potential impact.
MedusaLocker Ransomware Versions We Decrypt