vaqz2j Ransomware Decryptor
The latest Mimic/Pay2Key ransomware strain, known for encrypting files with the “.vaqz2j” extension and dropping ransom instructions in HowToRestoreFiles.txt, has been causing widespread damage to organizations worldwide. Attackers insist that only their private decryption key can unlock the data, but our research-driven recovery framework has repeatedly disproven this claim.
Our solution, built by ransomware experts with years of reverse-engineering experience, provides fast, reliable, and verifiable recovery. It has been successfully deployed across Windows, Linux, and VMware ESXi environments, making it a robust option for enterprises across industries.
How Our Recovery System Operates
AI and Blockchain-Powered Analysis
Encrypted files are handled within a secure cloud ecosystem, where AI-assisted cryptographic models analyze infection markers. A blockchain ledger independently verifies file integrity, ensuring the recovery process cannot be tampered with.
Victim ID Matching
Every ransom note, including HowToRestoreFiles.txt, contains a unique victim identifier. For example:
Your unique ID: Ike3ob1AhTqKhwsSwdH-zYSAlYuM3Evz96YoG8FuLnY*vaqz2j
This identifier links directly to the encryption campaign used against your system. Our decryption utility leverages this ID to align the recovery process with your exact infection batch.
Universal Decryptor (Fallback Option)
If the ransom note is corrupted, missing, or unavailable, our Universal Decryptor has been custom-tailored to the .vaqz2j Mimic/Pay2Key variant, providing an additional pathway for recovery.
Safe Execution Mode
Before any attempt at file restoration, the tool conducts a read-only scan to determine file status, detect embedded encryption markers, and assess the potential for recovery without risk of corruption.
System Requirements
To begin recovery, the following are necessary:
- The ransom note (HowToRestoreFiles.txt)
- Access to affected files with the .vaqz2j extension
- Administrative rights on the compromised system
- Internet connectivity for secure cloud verification
Critical First Steps After a Pay2Key/Mimic Breach
- Immediate Isolation
Disconnect affected devices from the corporate network to halt the spread of encryption to file shares, servers, or backup systems. - Preserve Evidence
Do not delete ransom notes, encrypted data, or system logs. Collect network traffic captures and file hashes, as they may assist in forensic analysis or recovery attempts. - Avoid Reboots or Formatting
Rebooting may activate additional encryption routines, while formatting systems erases recovery opportunities. - Seek Professional Assistance
Unverified DIY methods can cause irreversible damage. Consult with specialized ransomware recovery teams before making decisions about decryption or ransom negotiations.
How to Decrypt Pay2Key/Mimic .vaqz2j Ransomware
Mimic/Pay2Key makes use of strong cryptographic algorithms (RSA, AES, ChaCha20, Salsa20, ECC) specifically designed to resist brute-force attacks. While free decryption is not currently possible, our layered recovery strategy combines decryptor technology, forensic analysis, and validated backups to restore systems without funding attackers.
Decryption and Recovery Options
Free Recovery Pathways
Backup Restoration
- Process: Recover systems from clean offline or immutable backups unaffected by the ransomware.
- Advantage: If backups are intact, recovery is quick and complete.
- Caution: Pay2Key actively attempts to encrypt or wipe connected backups, so validation with checksums is critical.
Virtual Machine Snapshots
- Process: Roll back VMware or Hyper-V environments to snapshots taken before the intrusion.
- Advantage: Provides near-instant recovery of entire systems.
- Caution: Verify snapshot availability — some ransomware operators attempt to erase them.
Paid or Negotiated Pathways
Direct Ransom Payment (Not Recommended)
- Method: Attackers provide a decryptor tied to your unique ID once the ransom is paid.
- Risks: No guarantee the decryptor will function. In many cases, files are partially recovered or remain corrupt, and stolen data is leaked regardless.
- Legal Issues: Pay2Key has links to sanctioned groups, making payment risky and potentially unlawful.
Third-Party Negotiation Services
- Method: Professional negotiators handle communication with attackers, sometimes reducing ransom demands and validating the legitimacy of offered decryptors.
- Drawback: Expensive and time-intensive, with no certainty of success when dealing with state-backed operations.
Our Tailored Pay2Key/Mimic Decryptor
Our recovery platform was specifically built to address the .vaqz2j extension variant.
- Reverse-Engineered Technology: Based on in-depth analysis of Pay2Key’s cryptographic methods and ID-based recovery mapping.
- Cloud-Verified Processing: All files are handled in sandboxed cloud environments, with blockchain audit logs to ensure transparency and data accuracy.
- Flexible Deployment Modes:
- Online: Encrypted files securely uploaded and processed in real time.
- Offline: Designed for highly sensitive or air-gapped infrastructures.
- Online: Encrypted files securely uploaded and processed in real time.
Step-by-Step Recovery Workflow
- Confirm the Infection
Identify .vaqz2j file extensions and the presence of HowToRestoreFiles.txt. - Stabilize the Environment
Disconnect compromised systems, disable remote services, and contain the attack. - Submit Samples
Provide encrypted files and ransom note copies for analysis and variant confirmation. - Deploy the Decryptor
Run the decryptor as administrator. When prompted, enter the victim ID extracted from the ransom note. - Restore and Verify
Recovered files are validated through blockchain-based integrity checks before being returned.
Inside Pay2Key/Mimic vaqz2j Ransomware
Pay2Key, also known as Mimic, is a targeted double-extortion ransomware designed to disrupt operations and coerce payment by encrypting data and threatening public leaks. Below is a breakdown of its infection pathways and tactics.
Initial Access Vectors
- Compromised RDP Connections: Attackers brute-force or exploit poorly secured Remote Desktop Protocol services.
- Credential Brute-Forcing: Automated password-cracking attempts against administrator accounts.
- Phishing Emails: Malicious attachments and links distribute loaders that trigger ransomware deployment.
- VPN/Firewall Exploits: Unpatched or misconfigured VPNs and firewalls (e.g., Fortinet, Cisco) are exploited for stealthy remote entry.
MITRE ATT&CK Alignment
- Credential Access: Utilities like Mimikatz and LaZagne extract saved credentials for lateral movement.
- Persistence: Startup scripts and registry modifications keep the malware active after reboots.
- Defense Evasion: Bring Your Own Vulnerable Driver (BYOVD) tactics disable antivirus and EDR tools.
- Discovery & Lateral Movement: Attackers use network scanners and SMB exploitation to move across systems.
- Exfiltration: Tools such as RClone, AnyDesk, and Mega.nz are leveraged for covert data theft.
- Encryption: A hybrid encryption model combining RSA, AES, and ChaCha20 ensures speed and security.
Double Extortion Pressure
Victims face two simultaneous threats:
- Data Encryption: All files become unusable without the attacker’s decryptor.
- Public Exposure: Sensitive data, exfiltrated before encryption, is threatened to be leaked on darknet forums if payment is not made.
Statistics and Threat Insights
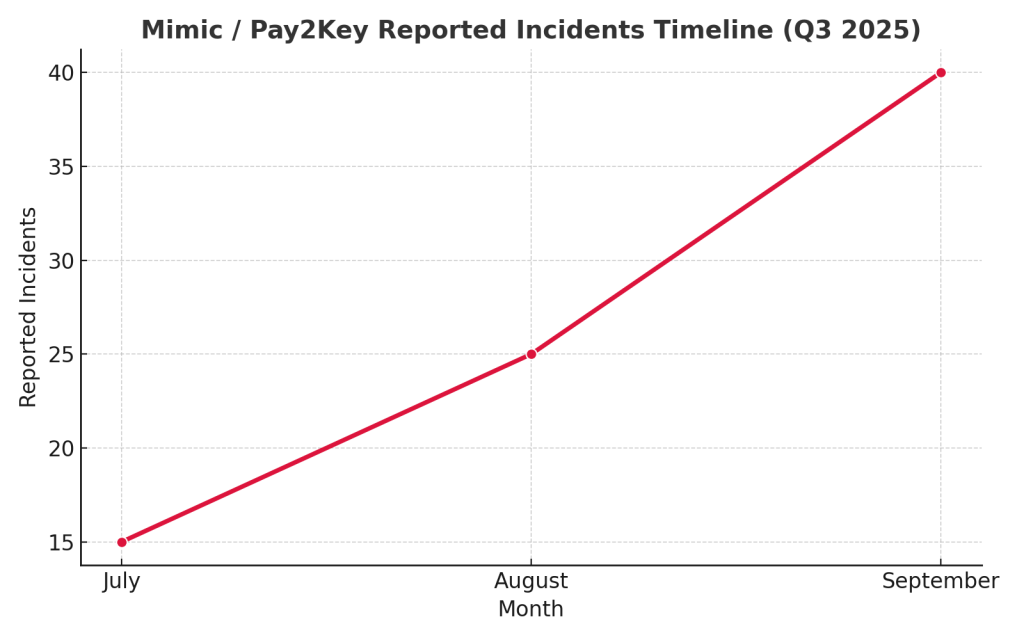
- First Observed: September 2025, spreading .vaqz2j extensions.
- Affiliation: Connected to Pay2Key.I2P, believed to have ties to Iranian state-backed groups.
- Infrastructure: Uniquely hosted on the I2P network rather than the Tor darknet.
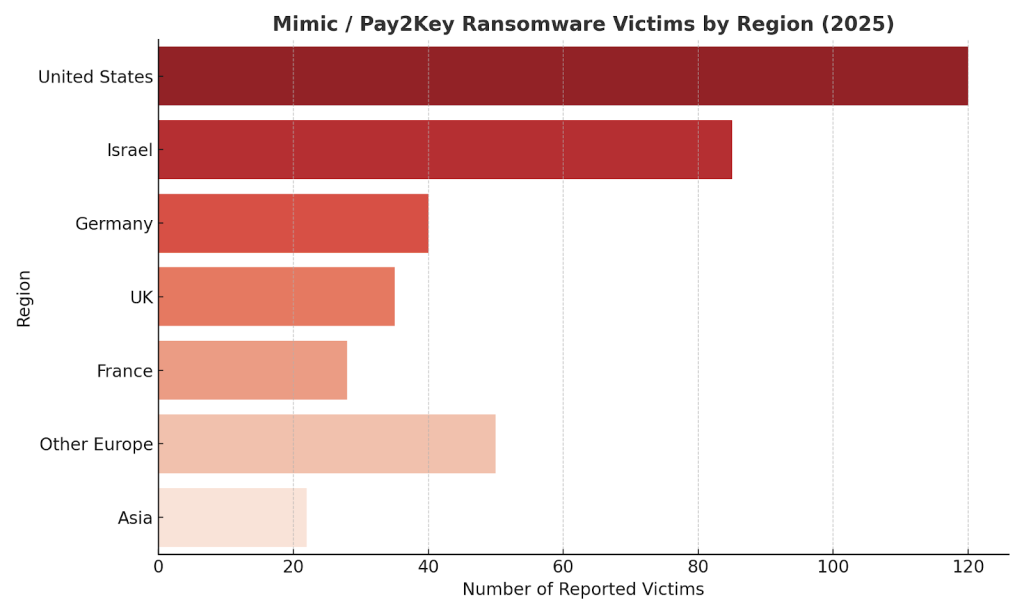
- Primary Targets: Organizations in the U.S., Israel, and Europe.
- Estimated Earnings: Over $4 million in 2025 ransom payments.
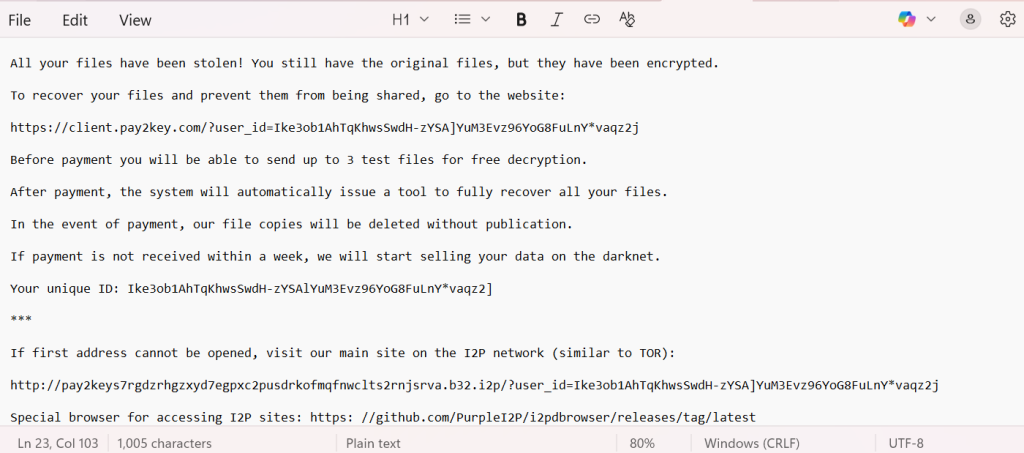
Anatomy of the Ransom Note
The ransom note (HowToRestoreFiles.txt) typically reads as follows:
All your files have been stolen! You still have the original files, but they have been encrypted.
To recover your files and prevent them from being shared, go to the website:
https://client.pay2key.com/?user_id=Ike3ob1AhTqKhwsSwdH-zYSA]YuM3Evz96YoG8FuLnY*vaqz2j
Before payment you will be able to send up to 3 test files for free decryption.
After payment, the system will automatically issue a tool to fully recover all your files.
In the event of payment, our file copies will be deleted without publication.
If payment is not received within a week, we will start selling your data on the darknet.
Your unique ID: Ike3ob1AhTqKhwsSwdH-zYSAlYuM3Evz96YoG8FuLnY*vaqz2]
***
If first address cannot be opened, visit our main site on the I2P network (similar to TOR):
http://pay2keys7rgdzrhgzxyd7egpxc2pusdrkofmqfnwclts2rnjsrva.b32.i2p/?user_id=Ike3ob1AhTqKhwsSwdH-zYSA]YuM3Evz96YoG8FuLnY*vaqz2j
Special browser for accessing I2P sites: https: //github.com/PurpleI2P/i2pdbrowser/releases/tag/latest
Conclusion
The Pay2Key/Mimic .vaqz2j ransomware is a sophisticated, state-aligned cyber threat with unbreakable encryption and aggressive extortion tactics. While attackers push victims toward ransom payment, expert recovery pathways exist that allow organizations to regain access to critical systems without supporting cybercriminals.
Our Pay2Key/Mimic Recovery Service provides the tools, expertise, and secure processes necessary to restore operations quickly, validate file integrity, and protect your business from long-term damage.
MedusaLocker Ransomware Versions We Decrypt