BB Ransomware Decryptor
BB ransomware is a variant of the MedusaLocker family, notorious for encrypting valuable data and locking systems until victims pay a ransom. Once active, it renames every encrypted file by appending the “.BB” extension (e.g., report.docx becomes report.docx.BB). Alongside file encryption, the malware generates a ransom note titled Recovery_Instructions.html, which appears in every folder affected.
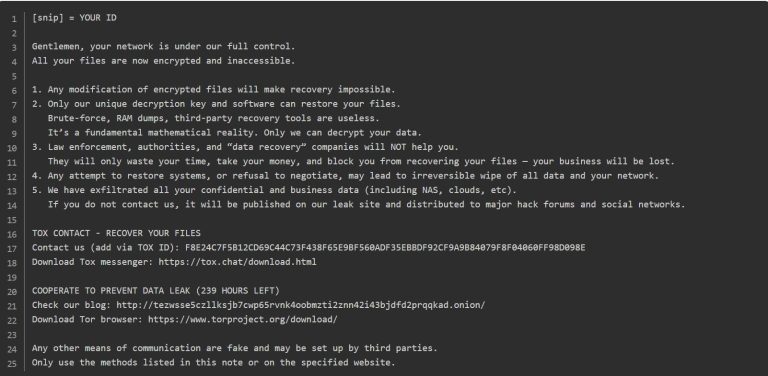
The ransom note instructs victims to reach the attackers via Tor links or two listed email addresses: [email protected] and [email protected]. A ransom is demanded, typically 0.3 BTC, and the criminals claim they use a hybrid encryption scheme (RSA + AES). Victims are pressured to pay quickly, as the note warns that the cost will rise if they don’t make contact within 72 hours.
Essential First Response Steps After BB Encryption
When BB ransomware strikes, immediate action is critical.
- Disconnect devices from the network without delay (unplug cables or disable Wi-Fi/Ethernet adapters) to contain the infection.
- Preserve forensic evidence — do not delete ransom notes or modify encrypted files. Collect logs, traffic captures, and file hashes for future analysis.
- Avoid unnecessary reboots — restarting infected systems may trigger additional scripts and make matters worse.
- Activate incident response — call in internal security teams or third-party experts as quickly as possible.
These steps should be carried out urgently and carefully, as they can significantly impact recovery options.
Containment and Removal of BB Ransomware
Removing the ransomware executable is an essential step but does not restore encrypted files. Use trusted endpoint protection tools or enterprise-grade EDR solutions to detect and remove BB’s binaries, registry modifications, and persistence mechanisms. After cleaning, leave compromised systems offline until you have a validated recovery plan.
A thorough scan with reputable antivirus programs (updated with the latest signatures) will help eliminate lingering threats, but remember: encrypted files will remain locked even if the infection is wiped.
Recovery Choices — Free Methods and Their Limitations
Backups
The safest way to regain access is through offline or immutable backups. Before restoring, confirm their integrity using checksums or snapshot validation. Many organizations successfully recover this way if backups were stored securely and isolated.
Shadow Copies
In some cases, Windows Volume Shadow Copies may still exist. If BB has not deleted them, you may be able to roll back. However, attackers typically remove these snapshots, leaving this option unreliable.
Decryptor Availability
At present, there is no free universal decryptor available for BB ransomware. Attempts to use random third-party tools can cause further file corruption.
When backups or shadow copies are intact, restoring after malware removal remains the best no-cost solution.
Paid Solutions — Negotiation, Risks, and Our BB Decryptor
Paying the Criminals
Victims who consider paying the ransom should know there is no assurance that valid decryption tools will be delivered. Even when provided, some tools cause corruption or leave hidden backdoors. Beyond technical risks, ransom payments fund organized crime and may breach legal or regulatory rules.
Engaging Negotiators
Some firms hire professional negotiators to communicate with the attackers through Tor portals. Negotiators can:
- Validate proof of decryption.
- Attempt to reduce ransom amounts.
- Manage sensitive communications securely.
However, this process can be expensive and still carries risk.
Our BB Decryptor Service
We provide a specialized decryptor for BB/MedusaLocker infections as part of our professional recovery services. This tool is based on careful reverse-engineering and operates within a secure, sandboxed environment.
Our approach includes:
- Variant verification: analyzing ransom notes, encrypted files, and victim IDs.
- Safe analysis: all testing is done read-only, ensuring no accidental overwrites.
- Negotiation support (if necessary): we can manage Tor communications and secure escrow payment if technical recovery isn’t possible.
- Integrity checks: every recovered file is validated against known hashes and returned with an audit report.
⚠️ Note: Clients must provide the ransom note (Recovery_Instructions.html) and encrypted file samples. While success rates are high, guarantees cannot be made, as outcome depends on the specific BB variant and attacker cooperation.
Step-by-Step Process for Using Our BB Decryptor
- Confirm infection — verify that files end with .BB and locate the ransom note.
- Secure the environment — isolate infected devices, and ensure no scripts are still running.
- Contact our recovery team — submit encrypted samples and ransom notes for analysis.
- Lab analysis — our specialists identify the exact BB variant and recommend a recovery mode.
- Select processing method — choose between offline (air-gapped) or cloud-assisted recovery.
- Prepare host — log in as administrator, close unnecessary applications, and mount affected drives in read-only mode if possible.
- Run decryptor in admin mode — the tool first performs a dry run to show which files it can decrypt safely.
- Provide Victim ID — enter the ID from the ransom note so the decryptor can map to the correct batch of keys.
- Execute decryption — confirm and start the process, then monitor logs closely.
- Validate results — audit logs and compare hashes to ensure decrypted files are authentic.
- Rebuild systems — patch vulnerabilities, apply security fixes, and harden systems before reconnecting them to production.
Online vs Offline Decryption Approaches
- Offline (air-gapped) decryption — preferred for highly confidential networks where no data should leave the premises.
- Cloud-assisted decryption — faster and more efficient for complex cases but requires secure, encrypted transfer of metadata or file fragments.
Both methods are supported by our decryptor, depending on organizational requirements.
What We Require to Begin Recovery
- Copy of the ransom note (Recovery_Instructions.html).
- 2–3 encrypted files (small samples).
- Victim ID from the ransom note.
- Approval for offline or cloud-assisted processing.
Technical Details at a Glance
BB ransomware applies asymmetric RSA encryption alongside AES symmetric keys, making recovery without the attacker’s keys nearly impossible. Criminals often claim they exfiltrate sensitive data before encryption, enabling double-extortion tactics. Victims usually observe files renamed with .BB, ransom notes in directories, and missing shadow copies.
Ransom Note
The ransom note informs victims their files have been encrypted, warns them against using third-party software, and threatens to leak stolen data. It lists Tor links, contact emails, and payment instructions (e.g., 0.3 BTC to the wallet 1PormUgPR72yv2FRKSVY27U4ekWMKobWjg). Victims are invited to submit 2–3 files for free decryption as proof.
The message also emphasizes urgency, stating that the ransom amount will increase after 72 hours.
YOUR PERSONAL ID:
–
/!\ YOUR COMPANY NETWORK HAS BEEN PENETRATED /!\
All your important files have been encrypted!
Your files are safe! Only modified. (RSA+AES)
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE
WILL PERMANENTLY CORRUPT IT.
DO NOT MODIFY ENCRYPTED FILES.
DO NOT RENAME ENCRYPTED FILES.
No software available on internet can help you. We are the only ones able to
solve your problem.
We gathered highly confidential/personal data. These data are currently stored on
a private server. This server will be immediately destroyed after your payment.
If you decide to not pay, we will release your data to public or re-seller.
So you can expect your data to be publicly available in the near future..
We only seek money and our goal is not to damage your reputation or prevent
your business from running.
You will can send us 2-3 non-important files and we will decrypt it for free
to prove we are able to give your files back.
Contact us for price and get decryption software.
hxxp://gvlay6u4g53rxdi5.onion/21-67gjhOAG8lerna1gBuHrXfleSKZIHEbG-6aKA403HiWP9ojmk4g4AAJonUb79Ly3A
* Note that this server is available via Tor browser only
Follow the instructions to open the link:
1. Type the addres “hxxps://www.torproject.org” in your Internet browser. It opens the Tor site.
2. Press “Download Tor”, then press “Download Tor Browser Bundle”, install and run it.
3. Now you have Tor browser. In the Tor Browser open “{{URL}}”.
4. Start a chat and follow the further instructions.
If you can not use the above link, use the email:
[email protected]
[email protected]
* To contact us, create a new mail on the site: protonmail.com
Make contact as soon as possible. Your private key (decryption key)
is only stored temporarily.
IF YOU DON’T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.
How BB Ransomware Spreads
Attackers distribute BB using several channels:
- Malicious spam emails with attachments (Word docs, PDFs, executables, archives).
- Fake software cracks and pirated installers.
- Malvertising and drive-by downloads.
- Trojan infections that install BB as a secondary payload.
These infection vectors allow both direct compromises and follow-on intrusions that spread laterally.
Key Indicators of Compromise (IOCs)
- Files renamed with .BB extension.
- Presence of Recovery_Instructions.html ransom note.
- Emails: [email protected], [email protected].
- BTC wallet example: 1PormUgPR72yv2FRKSVY27U4ekWMKobWjg.
- Tor communication channels listed in notes.
- AV detections mapping to MedusaLocker families.
- Deletion of Volume Shadow Copies (vssadmin delete shadows).
Tactics, Techniques, and Procedures (TTPs)
- Initial Access: phishing (T1566), exploitation of vulnerable services, malicious downloads.
- Credential Access: use of tools like Mimikatz to dump credentials (T1003).
- Lateral Movement: remote management abuse and scheduled task execution.
- Defense Evasion: deletion of shadow copies, disabling recovery functions.
- Exfiltration: in some campaigns, files are stolen before encryption (T1041/T1567).
- Impact: rapid encryption (T1486) of all reachable data.
Common attacker tools: RClone, WinSCP, AnyDesk, Mimikatz, and other admin/transfer utilities.
Structured Recovery Workflow
- Isolate affected systems.
- Document affected hosts and ransom notes.
- Save forensic evidence (logs, traffic dumps, hashes).
- Attempt validated backup or snapshot restoration.
- If backups fail, escalate to forensic or professional recovery teams.
- After decryption or restoration, harden infrastructure before resuming operations.
Preventing Future BB Infections
To reduce future risk, organizations should:
- Regularly patch VPNs, firewalls, and external-facing applications.
- Enforce multi-factor authentication on remote access.
- Disable unused RDP ports or protect them with strict policies.
- Maintain immutable or off-site backups.
- Segment networks to limit lateral spread.
- Use continuous monitoring (SOC or MDR services).
- Apply least-privilege access and block unsigned driver installations.
Insights Into BB Victim Data
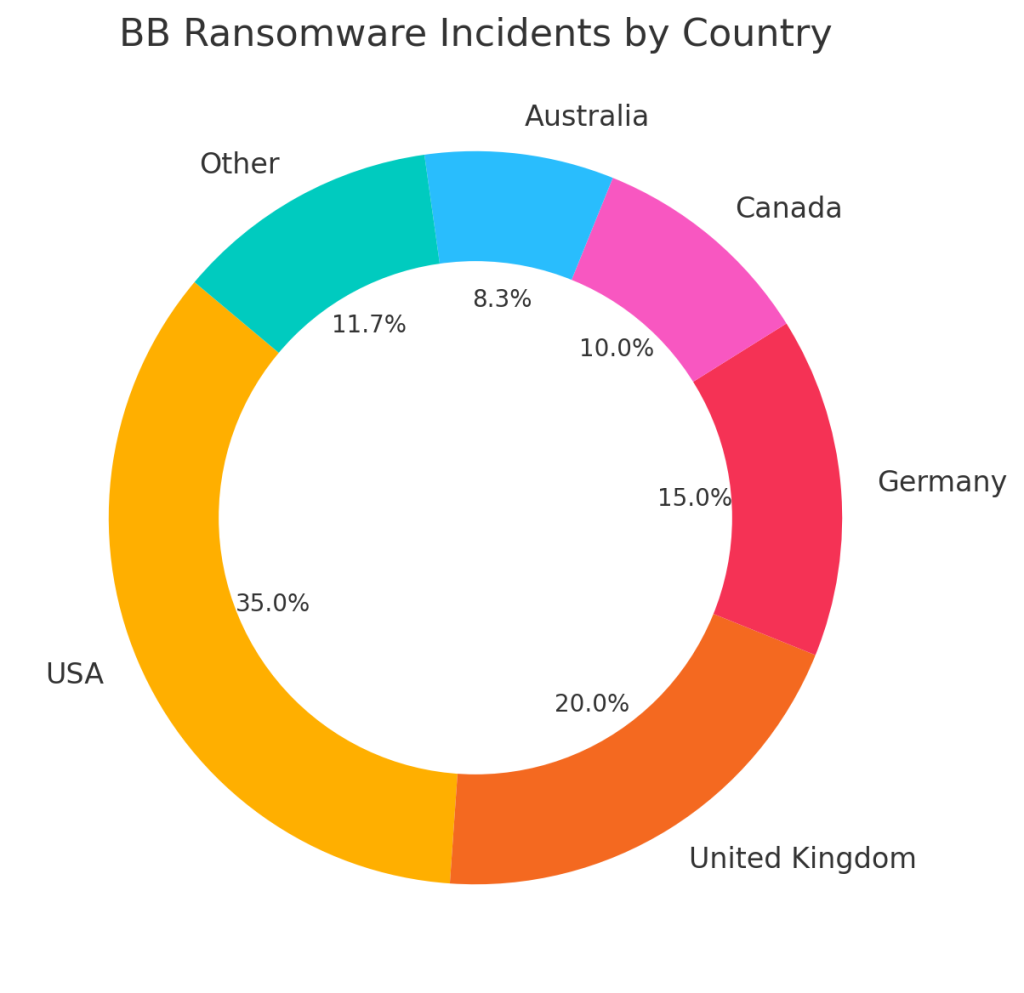
- By country: incidents have been most frequently observed in the United States, the UK, Germany, Canada, and Australia.
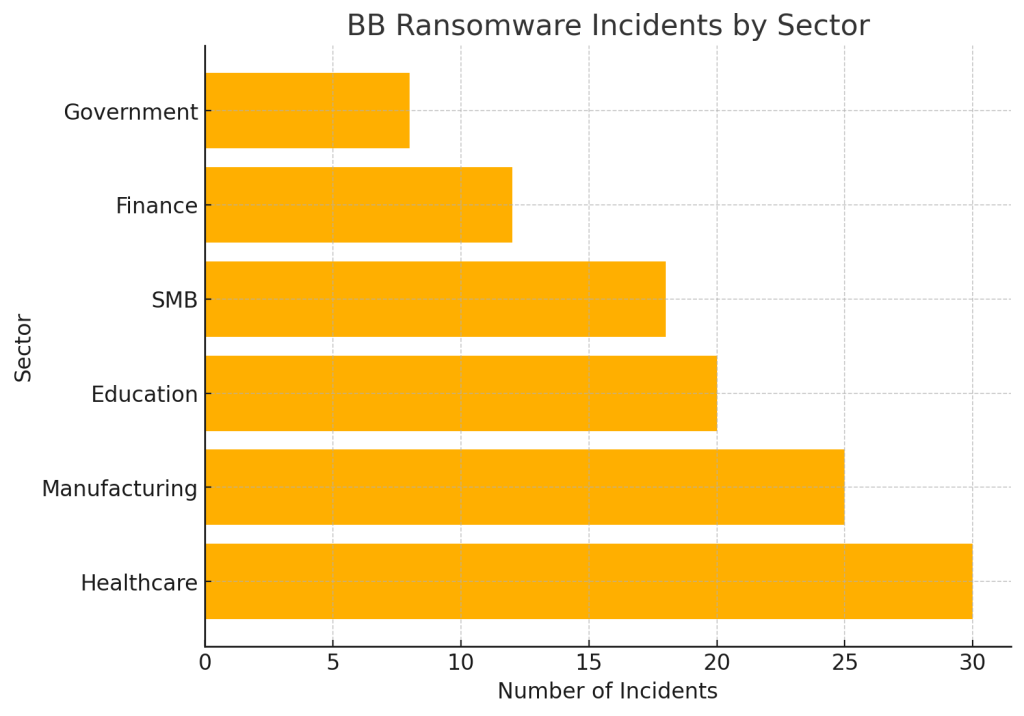
- By sector: healthcare, manufacturing, education, SMBs, finance, and government have been prime targets.
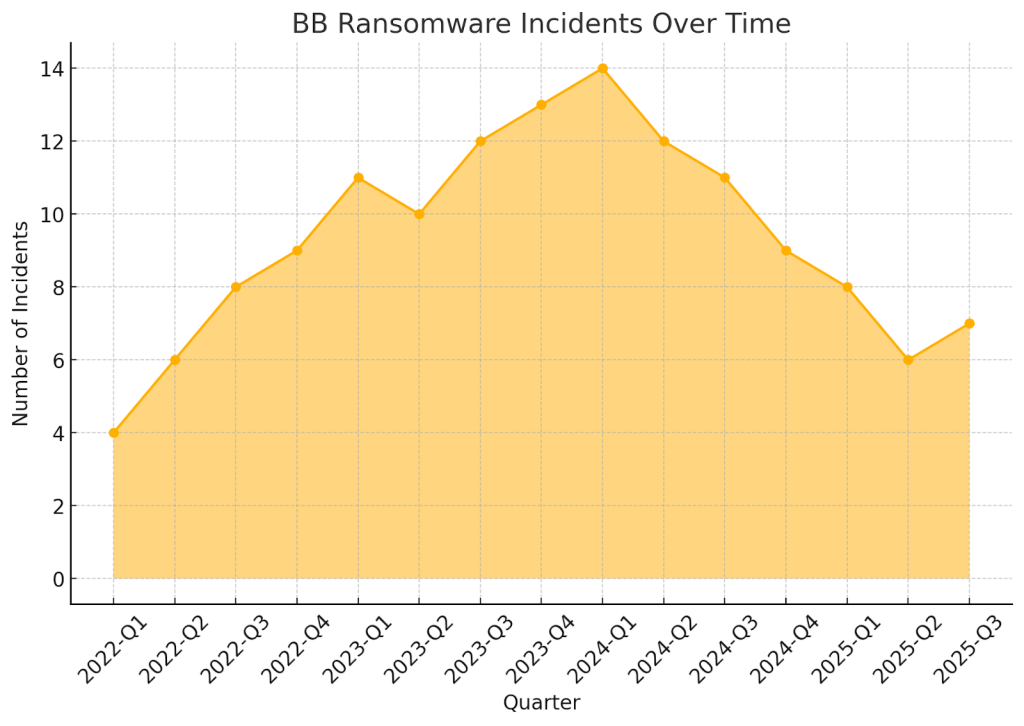
- By timeline: reported cases increased steadily between 2022 and mid-2024, with fluctuations continuing into 2025.
Forensic Evidence to Collect
For investigations, preserve:
- Encrypted file samples (one of each type).
- Copies of ransom notes.
- Memory dumps.
- Windows event logs.
- Antivirus and EDR logs.
- Evidence of scheduled tasks or unusual services.
- Network captures showing transfers to suspicious cloud services.
This data aids attribution, recovery, and potential legal reporting.
Conclusion
BB ransomware is one of the most destructive MedusaLocker variants in circulation. Victims must act swiftly to isolate infected systems, secure evidence, and engage with professional recovery services. The safest course is restoring from clean backups — when that’s not possible, carefully weigh negotiation and decryption options. Every incident should conclude with reinforced security and hardening to prevent reinfection.
MedusaLocker Ransomware Versions We Decrypt