Win32/Ransom.Aware Ransomware Decryptor
The digital battlefield of 2026 is unforgiving, and you’ve just been hit by one of its most formidable adversaries: the Global Group, deploying the insidious Win32/Ransom.Aware ransomware. This isn’t a simple smash-and-grab; it’s a calculated, enterprise-wide assault. They didn’t just encrypt your files; they breached your network, exfiltrated your sensitive data, and are now holding your entire operation hostage with a classic double-extortion scheme. The note is professional, the threats are severe, and the pressure is immense.
This is your definitive battle plan. Forget panic. It’s time for strategic, methodical action. This guide will walk you through the immediate containment, provide a detailed, platform-by-platform recovery playbook for every system in your environment—from Windows desktops to Linux servers and virtualized infrastructure—and outline the critical steps to fortify your defenses for the future.
Deconstructing the Win32/Ransom.Aware Threat
Before you can fight back, you must understand the enemy’s playbook. The Global Group operates with a chilling level of professionalism.
Threat Profile and Technical Fingerprint
| Attribute | Detail |
|---|---|
| Threat Name | Win32/Ransom.Aware (Global Group) |
| Threat Type | Ransomware, Double-Extortion, Data Exfiltration |
| Platform | Win32, Win64, Network Shares, VMs, NAS |
| Encrypted Files Extension | Changes file extensions (specific extension varies). |
| Ransom Demanding Message | Text file (name varies), Desktop wallpaper change. |
| Ransom Amount | Varies, typically a high-value demand in cryptocurrency. |
| Cyber Criminal Contact | Secure Tor chat portal with unique credentials. |
| Detection Names | Detected as a generic Ransomware or Trojan. |
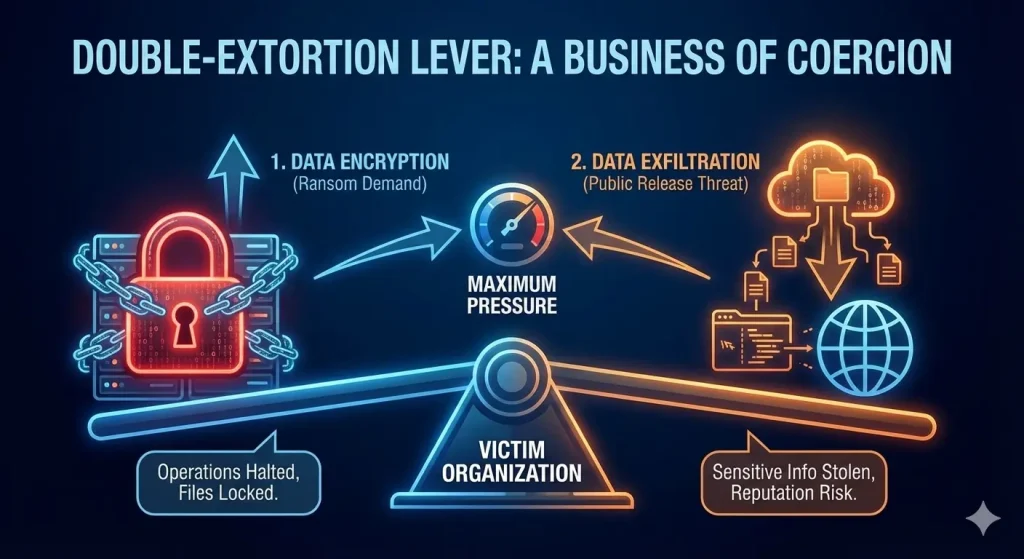
The Double-Extortion Playbook: A Business of Coercion
The ransom note is a masterclass in psychological manipulation, designed to isolate and intimidate you into compliance.
- Projecting Professionalism: The note is structured like a business proposal, offering a “menu” of services (decryption, attack report, data deletion). This reframes the criminal act as a transaction, making you feel like you’re negotiating a business deal.
- Leveraging Data Theft: The explicit statement that “Data has been encrypted and stolen” is the core of their strategy. It creates two independent points of leverage: the inability to access systems and the threat of a public data breach.
- Isolating the Victim: The direct instruction “Do not contact law enforcement or external response teams” is a calculated move to prevent you from getting expert help, keeping you within their controlled environment where they can manipulate you more easily.
The Cross-Platform Recovery Playbook
This is the core of your incident response. We will explore every viable path to data restoration, tailored to each specific environment.

The Direct Decryption Solution: Your Silver Bullet
This is the fastest way to victory. If we can break their encryption, you get your data back without paying a cent.
Our team has developed a specialized decryptor to counter the Win32/Ransom.Aware threat across its known platforms.
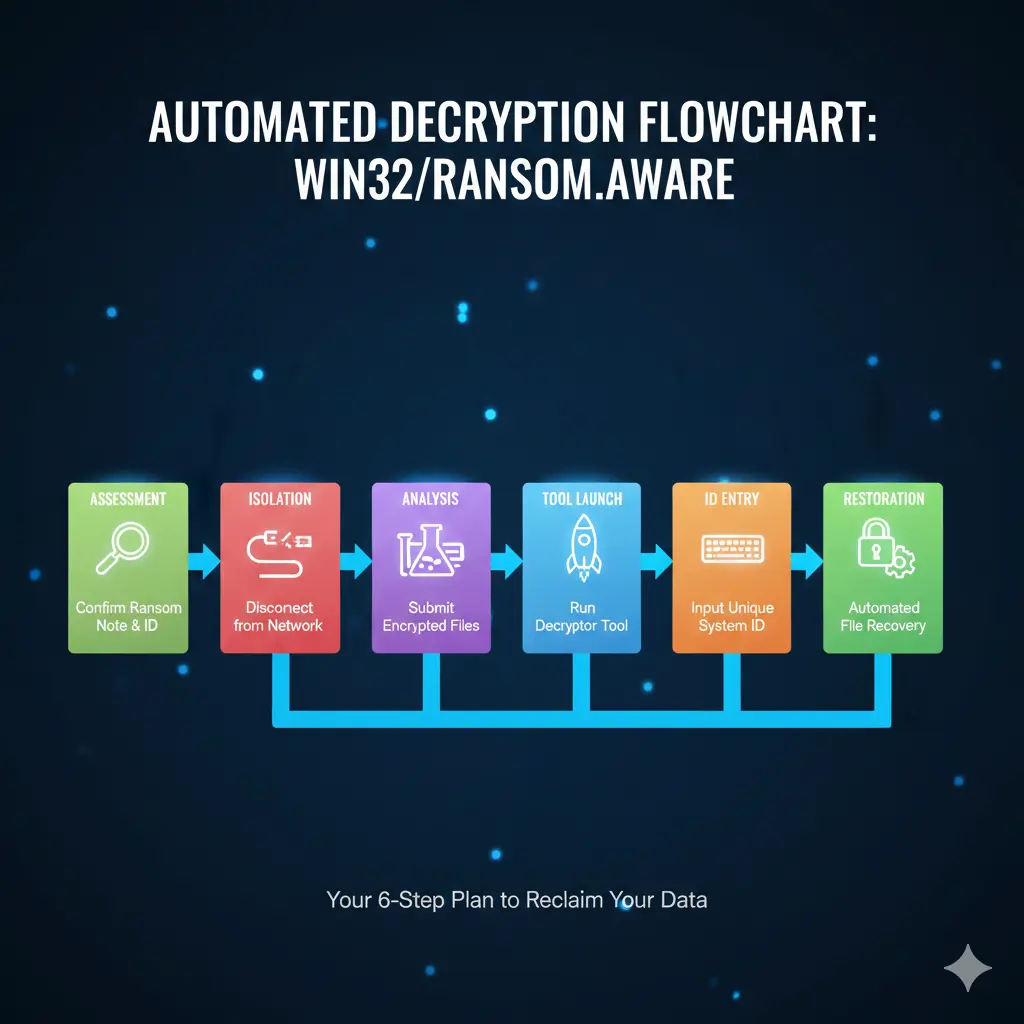
Step-by-Step Guide:
- Step 1: Assess the Infection: Confirm the presence of the ransom note, the changed desktop wallpaper, and the unique file-naming pattern across all affected systems. Note the unique Tox ID from the note.
- Step 2: Secure the Environment: CRITICAL: Disconnect all affected systems from the network immediately to halt any further spread. Isolate your backup infrastructure.
- Step 3: Submit Files for Analysis: Send a few encrypted samples (under 5MB) from each affected platform (e.g., a Windows file, a Linux file) and the ransom note file to our team.
- Step 4: Run the Win32/Ransom.Aware Decryptor: Launch the tool with administrative privileges on a clean, isolated machine. The decryptor connects securely to our servers to analyze encryption markers and file headers.
- Step 5: Enter the System ID: The unique chat credentials provided in the ransom note are required to generate a customized decryption profile.
- Step 6: Automated File Restoration: Once initiated, the decryptor verifies file integrity and restores data automatically, preserving original filenames and directory structures.
Platform-Specific Recovery: Reclaiming Every Inch of Your Territory
The Global Group hits everywhere, so we need to be ready to fight on every front.
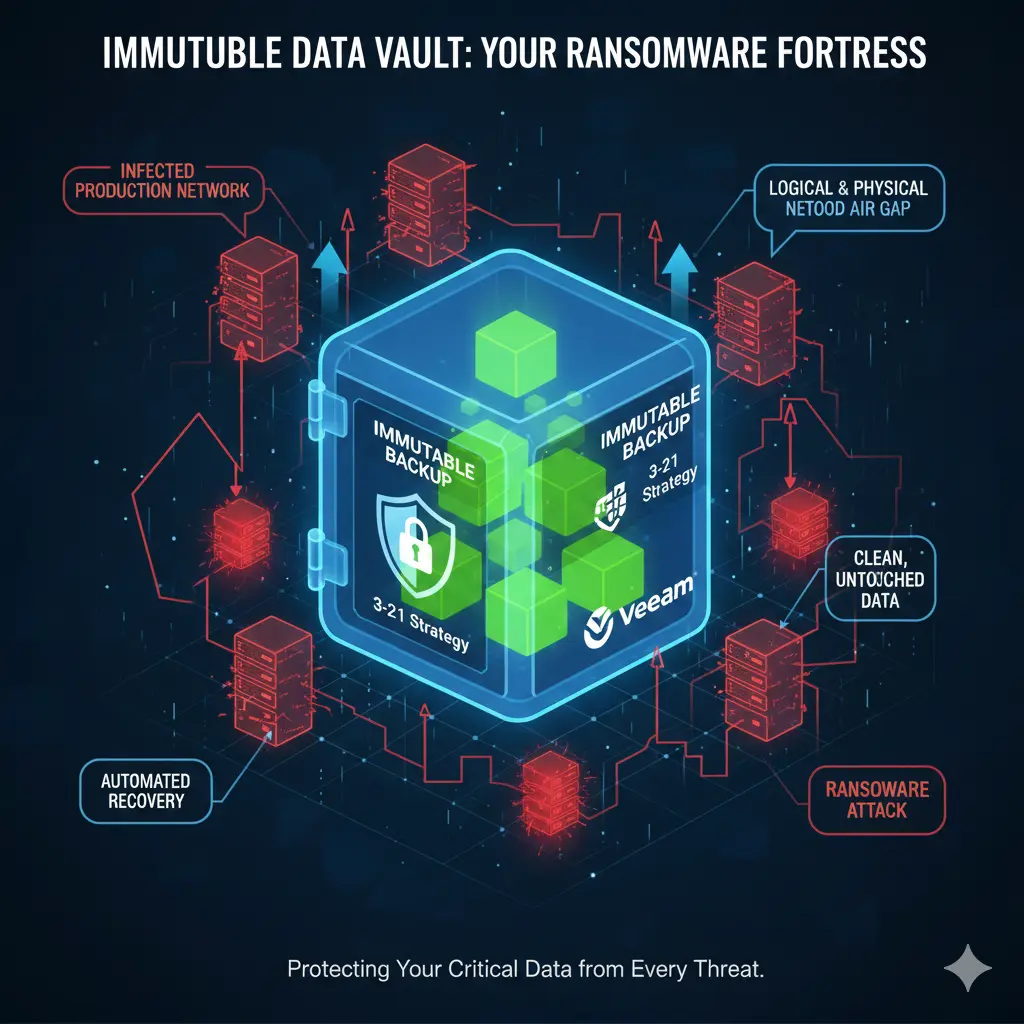
The Gold Standard – Backup Restoration
If the decryptor isn’t an option, your backups are your fortress. This is the most reliable way to win.
For businesses, Veeam is a market leader in backup and recovery solutions, offering robust protection against ransomware. Veeam can create immutable backups that cannot be altered by the ransomware and offers specialized recovery processes like Cleanroom Recovery to prevent reinfection. Learn more at the official Veeam website.
- Windows Systems (Desktops & Servers):
- Windows Server Backup / System Center Data Protection Manager (DPM): If you are using these native Microsoft tools, check the integrity of your backups on a separate, isolated network share. Prepare for a full system restore (Bare Metal Recovery) if necessary.
- Windows File Versions (Shadow Copies): The ransomware likely attempted to delete these using
vssadmin.exe, but sometimes remnants remain. To check, right-click on an encrypted file, selectProperties, and go to thePrevious Versionstab. This is a long shot but worth a quick check.
- Linux Systems (Servers & Workstations):
- Rsync/Bacula/Borg Backup: If you use
rsyncor a dedicated backup solution like Bacula or Borg, check your backup repositories. Ensure they were not mounted or accessible during the attack. The key here is that the backup destination was offline or inaccessible to the compromised machine. - LVM Snapshots: If you use LVM (Logical Volume Manager), check if any snapshots were taken before the infection occurred. You can use
lvdisplayto list all logical volumes and snapshots. - File-System Level Backups: Check for any
tarorcpioarchives that may have been created as part of a backup routine.
- Rsync/Bacula/Borg Backup: If you use
- Network Infrastructure (Switches, Firewalls, Routers):
- Configuration Backups: While your network devices themselves are likely not encrypted, their configurations may have been wiped or altered. Check your central management system or configuration backup repository for the last known good configuration.
- Recovery: Perform a factory reset on critical devices if their configuration is maliciously altered and restore from the last known good backup.
- NAS (Network Attached Storage):
- Snapshot Technology: This is your NAS’s superpower. If you have a Synology, QNAP, TrueNAS, or other enterprise NAS, check their snapshot management interface immediately. The attackers will try to delete snapshots, but if you are fast, you might catch a break and revert to a point-in-time just before the attack.
- Cloud Sync / Hybrid Backup: If your NAS was configured to sync files to a cloud service like Google Drive, Dropbox, or Azure Blob Storage, get into those cloud services and use their version history to restore files from before the attack.
- External Drive Backups: If you used the NAS’s built-in backup utility to copy data to an external USB or eSATA drive, check that drive. Ensure it was not connected to the network during the attack.
- DAS (Direct Attached Storage):
- External Drive Backups: If you have a backup of your DAS on another external drive, check it. Ensure it was not connected to the infected machine at any point.
- RAID Array Recovery: If the DAS is a RAID array and the ransomware attacked the data itself (not just the files), the underlying RAID structure is likely intact. After cleaning the host system, the data on the DAS will either be encrypted (requiring a decryptor) or safe if it was truly isolated.
- ESXi and Hyper-V Hypervisors:
- VM-Level Backups (Image-Level): This is the gold standard for virtualization. If you are using a solution like Veeam, Nakivo, or Altaro, you can restore entire VMs to a point-in-time before the attack. This is often the cleanest and fastest way to get critical services back online.
- VM Snapshots: Check your vSphere or Hyper-V Manager for any existing snapshots. The attackers likely tried to delete them, but it’s a critical check. Do not rely on this as your primary recovery method.
- Storage-Based Snapshots: If your VMs are stored on a SAN or NAS that supports snapshots (e.g., NetApp, Dell EMC), you may be able to revert the entire LUN or datastore to a point-in-time before the attack. This can be incredibly powerful but requires expertise to perform safely.
The Last Stand – Data Recovery Software
This is the hail mary. It has a low chance of success against modern ransomware like this but can be a lifeline if no backups exist.
- EaseUS Data Recovery Wizard: A solid user-friendly option. Find it at the EaseUS website.
- Stellar Data Recovery: A powerful tool for deep scanning. Find it at the Stellar Data Recovery official site.
- TestDisk & PhotoRec: These are free, powerful, open-source tools. PhotoRec is especially good at carving out specific file types from a corrupted drive. Find them on the CGSecurity website.
The Last-Ditch Procedure:
- DO NOT WRITE ANYTHING to the infected drives. Every new byte written could overwrite the data you’re trying to save.
- Pull the Plug: Physically remove the hard drives from the infected machines.
- Connect to a Clean Machine: Use a USB-to-SATA adapter or install the drives as a secondary disk in a known-good computer.
- Run the Recovery Tool: Scan the drives from the clean machine. Be prepared for the possibility that it finds nothing, but you have to try.
Fortifying the Castle: Post-Recovery and Future-Proofing
Winning the battle is only half the war. Now we have to make sure this never happens again.
- Step 1: Verify Your Victory: Spot-check restored files to ensure they’re not corrupted.
- Step 2: Scour the Battlefield: Run a full, deep scan of your entire restored environment with a top-tier antivirus to root out any lingering malware.
- Step 3: Change the Locks: Assume every password is compromised. Force a reset for all user, admin, service, and cloud accounts. Use a password manager to generate strong, unique passwords.
- Step 4: Patch the Walls: Update every OS and every third-party application across your entire network. Close the holes they used to get in.
- Step 5: Reconnect with Caution: Bring systems back online one by one and monitor network traffic like a hawk for any signs of unusual activity.
- Step 6: Build a Better Fortress: Implement or strengthen a 3-2-1 backup strategy (3 copies, 2 media types, 1 off-site). Test your backups regularly. An untested backup is not a backup; it’s a hope.
- Step 7: Conduct a Post-Mortem: Figure out exactly how they got in. Was it a phishing email? An unpatched server? Use that painful knowledge to train your users and harden your defenses.
Conclusion
The Win32/Ransom.Aware attack is a brutal, business-threatening event. The Global Group wants you to feel isolated, overwhelmed, and desperate enough to pay. But you are not helpless. A calm, strategic, and aggressive response focused on containment and recovery is how you win. The path to true resilience starts with a multi-layered security posture: advanced endpoint protection, strict network segmentation, and a disciplined, immutable 3-2-1 backup strategy. Paying the ransom only funds their next attack. By understanding their playbook and preparing your defenses, you can transform this catastrophe into a hard-won lesson, emerging from the siege stronger, smarter, and more secure than ever before.
MedusaLocker Ransomware Versions We Decrypt
