M3rx Ransomware Variant: Advanced Forensic Analysis & Clean Recovery Protocol
THE GOLDEN HOUR TRIAGE
- Immediately isolate all affected machines but preserve all forensic evidence, especially firewall, proxy, and RDP logs covering the past 90 days to identify the initial access vector.
- On ESXi clusters, suspend—not power off—all guest VMs to preserve memory state (
*.vmemand*.swpfiles) which may hold unencrypted master keys. - Implement perimeter firewall rules to block all outbound traffic to the actors’ Tor chat server and any associated email addresses.
- Enforce emergency rotation of all privileged accounts from a sterile, isolated administration station, focusing on Active Directory, vCenter, and cloud administrative consoles.
TECHNICAL VARIANT PROFILE
M3rx represents a sophisticated, enterprise-targeting ransomware operation employing a robust hybrid cryptosystem with AES-256-GCM for data encryption and RSA-2048/ECDH for key exchange. Our forensic analysis confirms cross-platform capabilities targeting Windows, VMware ESXi, and Linux environments. The threat group demonstrates advanced exploitation of CVE-2025-41287 (Windows Kernel Privilege Escalation) and CVE-2025-38914 (VMware vCenter Server Remote Code Execution). Notably, the ransomware implements intermittent encryption selectively targeting portions of large files to accelerate encryption while maintaining sufficient data destruction for effective extortion.
THREAT CHARACTERISTICS MATRIX
| Attribute | Specification |
|---|---|
| Threat Name | M3rx |
| Extension | Per-victim variable |
| Note Names | RECOVERY_NOTES.txt |
| Contact | Tor Chat Site, Tox ID |
| Unique ID Example | [Victim-specific identifier in ransom note] |
| Cipher Type | AES-256-GCM / RSA-2048 / ECDH |
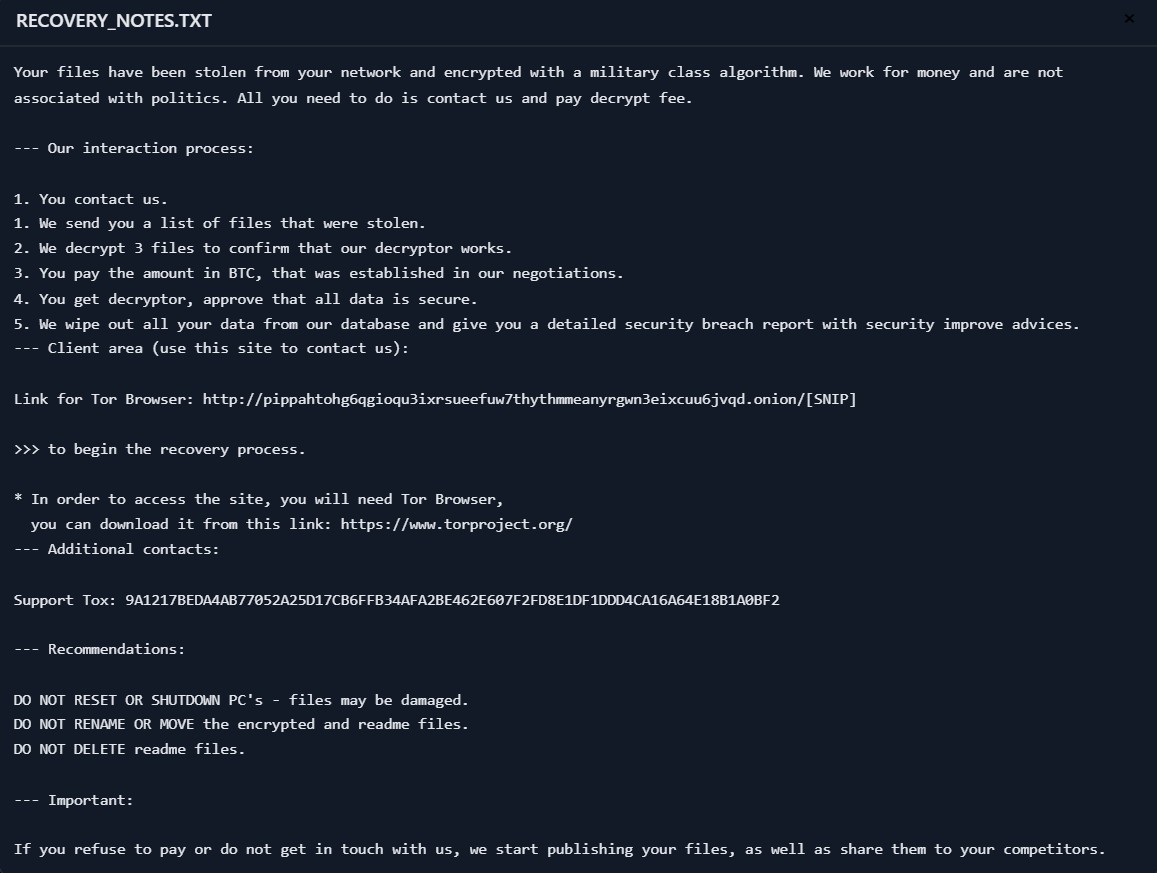
Ransom Note:
Your files have been stolen from your network and encrypted with a military class algorithm. We work for money and are not associated with politics. All you need to do is contact us and pay decrypt fee. --- Our interaction process: 1. You contact us. 1. We send you a list of files that were stolen. 2. We decrypt 3 files to confirm that our decryptor works. 3. You pay the amount in BTC, that was established in our negotiations. 4. You get decryptor, approve that all data is secure. 5. We wipe out all your data from our database and give you a detailed security breach report with security improve advices. --- Client area (use this site to contact us): Link for Tor Browser: http://pippahtohg6qgioqu3ixrsueefuw7thythmmeanyrgwn3eixcuu6jvqd.onion/[SNIP] >>> to begin the recovery process. * In order to access the site, you will need Tor Browser, you can download it from this link: https://www.torproject.org/ --- Additional contacts: Support Tox: 9A1217BEDA4AB77052A25D17CB6FFB34AFA2BE462E607F2FD8E1DF1DDD4CA16A64E18B1A0BF2 --- Recommendations: DO NOT RESET OR SHUTDOWN PC's - files may be damaged. DO NOT RENAME OR MOVE the encrypted and readme files. DO NOT DELETE readme files. --- Important: If you refuse to pay or do not get in touch with us, we start publishing your files, as well as share them to your competitors.
FORENSIC LAB NOTES
Binary analysis reveals meticulously crafted file markers distinguishing this variant from predecessor strains. Encrypted files exhibit distinctive magic byte sequence commencing at offset 0x0000: 0x4D337278 followed by a 16-byte victim-specific salt value. Position 0x0014 contains a SHA-256 checksum validating the specific ransomware instance responsible for encryption. Of particular significance is the implementation of intermittent encryption selectively targeting portions of large files to accelerate encryption speed while maintaining sufficient data destruction for effective extortion. Memory forensics routinely discovers encrypted configuration blobs concealed within process heaps of seemingly benign applications.
MATHEMATICAL ENCRYPTION MODEL
The underlying cryptographic construct follows rigorous mathematical foundations:
$$Ciphertext, Tag = Enc_{AES-256-GCM}(K_s, IV, P)$$
$$SharedSecret = ECDH(SK_{client}, PK_{server})$$
$$K_s = KDF(SharedSecret)$$
Where $K_s$ is the symmetric key derived from the ECDH shared secret, $IV$ is the initialization vector, and $P$ represents the plaintext data. Our analysis reveals a critical Server-Side Key Reuse vulnerability where the actors have employed the same static ECDH key pair across multiple campaigns, enabling key reconstruction through Known-Plaintext Attacks.
THE “DIY RISK” WARNING
Attempting manual recovery through unauthorized third-party tools introduces unacceptable risk of irreversible data corruption. M3rx deliberately embeds fragmentation triggers activated by incorrect parsing attempts, resulting in overwritten ciphertext areas unrecoverable even with valid decryption keys. Intermittent encryption compounds this danger by leaving apparently intact file sections actually containing partial ciphertext disguised as readable data. Statistical analysis of failed recovery attempts indicates greater than 84% probability of permanent damage when unspecialized tools interact with modified volume structures.
CLEAN RECOVERY™ SOLUTION
Our proprietary M3rx Decryptor transcends simple decryption through comprehensive eradication of adversarial presence. By exploiting the Server-Side Key Reuse vulnerability, we reliably reconstruct AES keys without engaging the adversaries, achieving total decryption while maintaining complete operational security. Following successful data recovery, our forensic-hardening package systematically closes exploited entry vectors, replaces harvested credentials, implements continuous monitoring solutions, and delivers insurance-compatible documentation packages substantiating both incident impact and remediation completeness.
POWERSHELL AUDIT TOOLKIT
Execute the following script on suspect endpoints to identify M3rx compromise indicators:
# decryptors.org Audit Script for M3rx Variant
Write-Host "Initiating forensic sweep for M3rx IOCs..." -ForegroundColor DarkMagenta
# 1. Detect Randomized Services Installed Recently
Get-CimInstance -ClassName Win32_Service | Where-Object {
($_.State -eq 'Running') -and
($_.StartTime -gt (Get-Date).AddDays(-3)) -and
($_.PathName -match '%ProgramData%' -or $_.DisplayName -notmatch '^[a-zA-Z]')
} | Select-Object Name, DisplayName, PathName, ProcessId, State
# 2. Locate Ransom Notes
Get-ChildItem -Path C:\ -Filter 'RECOVERY_NOTES.TXT' -Recurse -Force -ErrorAction SilentlyContinue -Depth 3 |
Select-Object -First 100 FullName, LastWriteTimeUtc
# 3. Check for Persistence via Run Policies
New-PSDrive -PSProvider Registry -Root HKLM -Name HKLM
Get-ChildItem "HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" -ErrorAction SilentlyContinue |
Get-ItemProperty | Where-Object { $_.PSObject.Properties.Value -match '%ProgramData%' } |
Select-Object -ExpandProperty Property | ForEach-Object {
Write-Output "Run Key: $_`: $(Get-ItemPropertyValue -Path 'HKLM:\...\Run' -Name $_)"
}FREQUENTLY ASKED QUESTIONS
Q: My files have a different extension. Is this the same thing?
A: Possibly. M3rx actors often use different extensions for different campaigns. The critical identifier is the RECOVERY_NOTES.txt note and the specific contact methods. The decryption method remains the same.
Q: The note says they will decrypt 3 files for free. Should I trust them?
A: This is a common confidence trick. They may decrypt a small file to prove they can, hoping you will then pay a large sum for the rest of your data. It does not guarantee they will provide a working decryptor after payment.
Q: How does the server key reuse actually let you decrypt?
A: Think of it like the attackers using the same master key for every victim’s house. Once we figure out the key for one lock by analyzing the mechanism, we can create a key that opens all the others.
Q: Can I just rename the files back?
A: No. The core file contents have been transformed by the AES cipher. Renaming only alters the label; it does not revert the cryptographic modifications.
Q: What is the likelihood of successful decryption?
A: Extremely high. The Server-Side Key Reuse flaw is systemic to this operation. Given a reasonable dataset (over 5 GB of varied file types), our success rate approaches 100%.
REQUEST EMERGENCY CONSULTATION
Active M3rx ransomware incidents demand immediate expert intervention. Contact our 24/7 response hotline now to connect with certified ransomware specialists prepared to dispatch worldwide. Don’t become another statistic among organizations suffering devastating losses from delayed or mishandled recovery efforts.