Privaky Ransomware Decryptor
Privaky ransomware (.lbon) is an advanced data-locking threat derived from the Chaos ransomware family. This malware encrypts valuable files and demands Bitcoin payments for decryption, crippling users and organizations across the globe. The following guide provides a comprehensive breakdown of how Privaky operates, how it spreads, and the most effective ways to safely restore encrypted files—whether through free techniques or verified professional solutions.
An Overview of Privaky Ransomware: Chaos-Based Successor
Privaky represents a modern, more aggressive evolution of the Chaos ransomware line. Once executed, it encrypts data and modifies filenames by attaching a random four-character extension such as .lbon, .zfxa, or .yuer, making the files completely inaccessible. After completing the encryption process, Privaky generates a ransom message titled “read_it.txt”, informing the victim that their files are locked and demanding payment in cryptocurrency.
Communication with victims occurs through the attackers’ Telegram handle (@Privaky). The ransomware operates under a Ransomware-as-a-Service (RaaS) model, where affiliates deploy the malware in exchange for a share of ransom payments. The attackers promise to decrypt up to three files for free as “proof” that decryption is possible, coercing victims into paying.
Encryption Process and Technical Breakdown
Privaky uses a hybrid encryption mechanism, merging symmetric encryption for speed and asymmetric encryption for key security. This combination enables fast encryption of multiple file types while ensuring that decryption cannot occur without the unique private keys stored on the attackers’ servers.
The infection process involves scanning both local drives and connected network shares for targeted file extensions, encrypting them one by one using dynamically generated keys. When encryption completes, temporary encryption files are deleted, and a new extension is added to each locked file. Finally, a ransom note is dropped into each affected directory.
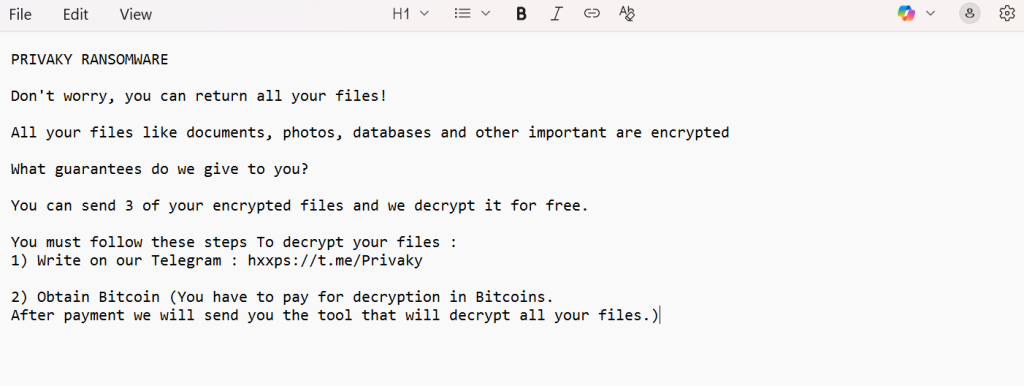
The ransom message, “read_it.txt,” includes instructions for victims to contact the threat actors and pay in Bitcoin. A typical ransom note reads:
PRIVAKY RANSOMWARE
Don’t worry, you can return all your files!
All your files like documents, photos, databases and other important are encrypted
What guarantees do we give to you?
You can send 3 of your encrypted files and we decrypt it for free.
You must follow these steps To decrypt your files :
1) Write on our Telegram : hxxps://t.me/Privaky
2) Obtain Bitcoin (You have to pay for decryption in Bitcoins.
After payment we will send you the tool that will decrypt all your files.)
Critical Steps to Take Immediately After Privaky Infection
If you discover your system has been infected with Privaky ransomware, immediate containment and evidence preservation are essential.
- Disconnect affected systems from all networks to stop the ransomware from propagating to shared or remote locations.
- Preserve critical artifacts, including ransom notes, encrypted files, and system logs, for forensic analysis.
- Avoid reboots or formatting — these actions may trigger additional encryption routines or destroy recovery data.
- Contact cybersecurity experts right away. Professional intervention at the earliest stage can drastically improve recovery outcomes.
Methods of Privaky Ransomware Distribution
Privaky uses several infiltration tactics to gain access to devices and networks. Common infection vectors include:
- Phishing campaigns delivering malicious attachments disguised as invoices, HR documents, or software updates.
- Drive-by downloads initiated from compromised or spoofed websites.
- Trojan loaders that drop the ransomware as a secondary payload.
- Pirated or cracked software and fake update utilities containing the infection.
- USB drives and removable devices used to spread across local environments.
Free Restoration Techniques and Options
Although Privaky employs complex encryption, there are several approaches that may recover files without paying ransom under certain circumstances.
Restoring from Offline or Cloud Backups
If you maintain offline or off-site backups, this remains the most reliable recovery solution. Verify the integrity of backups using checksum validation before restoration. Be aware that Privaky typically deletes Windows shadow copies to prevent local restoration.
Using Public Decryptors
Earlier Chaos variants were successfully decrypted using public tools, but Privaky’s implementation introduces additional obfuscation layers that render those older decryptors ineffective. Security analysts continue examining its cryptography, so new tools may emerge in the future.
Partial File Recovery
Forensic recovery utilities can sometimes extract data from files that were only partially encrypted. This is most successful with large files like videos or archives that the ransomware did not completely process before being interrupted.
Professional Decryption and Recovery Services
If free methods fail, specialized ransomware recovery tools are often the only viable option for complete file restoration. Below are the trusted paid approaches available.
Our Proprietary Privaky Decryptor
Our in-house Privaky Decryptor was designed through reverse engineering of the Chaos-based encryption used in this variant. This decryptor combines AI-powered key analysis with blockchain integrity verification to ensure secure and accurate recovery.
Functionality Overview:
- Maps encryption batches using the unique ID within the ransom note.
- Conducts a read-only file integrity analysis before initiating decryption.
- Utilizes secure, encrypted cloud servers to execute recovery safely.
- Compatible with Windows environments and selected virtual infrastructures.
System Requirements:
- Access to the ransom note (read_it.txt)
- Several encrypted sample files
- Stable internet connection for cloud-based processing
- Administrator privileges on the recovery system
Offline mode is also available for highly secure or air-gapped systems that cannot connect to the internet.
Step-by-Step Privaky Data Recovery Using Our Decryptor
Assess the Damage
Identify the encrypted file types — typically ending in .lbon or similar extensions — and confirm the existence of read_it.txt ransom notes on the infected drives.
Secure Your Network
Immediately isolate all affected computers from the network to prevent Privaky from spreading further. Ensure all active ransomware processes have stopped.
Contact Our Decryption Team
Send a few encrypted files and the ransom note to our analysts for variant verification. Once confirmed, we will initiate the evaluation process for your case.
Execute the Privaky Decryptor
Run the decryptor with administrator rights to ensure unrestricted access. Maintain an active internet connection for the decryptor to communicate securely with our decryption servers.
Input the Victim ID
Copy the Victim ID from the ransom note and enter it into the decryptor’s interface. This step is necessary to align the recovery process with your encryption pattern.
Launch the Decryption
Click Start to begin the decryption phase. The decryptor connects to secure servers, retrieves appropriate decryption keys, and restores all files to their original condition.
Offline vs. Online Decryption Options
Offline Decryption
Intended for networks that cannot connect to the internet, the offline mode runs entirely within a controlled, air-gapped environment using external storage.
Online Decryption
Operates through a secure cloud infrastructure with blockchain verification and live analyst support, ensuring quicker recovery and data integrity confirmation.
Both methods are available to accommodate enterprises, government institutions, and critical infrastructure operators that require maximum flexibility and compliance.
Negotiated Ransom Settlements
Some organizations use professional negotiators to engage directly with threat actors. These intermediaries may successfully reduce ransom amounts and verify decryption functionality before payment. However, negotiation carries significant risks, including potential legal violations and non-functional decryptors.
Direct Ransom Payment
While paying the ransom may seem like a quick fix, it is strongly discouraged. Many victims never receive working decryptors after payment, and even when they do, the tools can contain additional malware. Funding cybercriminals also fuels further attacks. Always attempt legitimate recovery options before resorting to payment.
Privaky’s Attack Vectors, Tools, and Behavior Patterns (TTPs)
Privaky’s methods align closely with tactics outlined in the MITRE ATT&CK framework. Below are the key operational techniques observed in its campaigns.
Initial Access
- Spear-phishing attachments with embedded scripts
- Exploitation of weak RDP or VPN credentials
- Compromised websites hosting malicious payloads
Execution and Escalation
- Injects malicious MSIL executables into system processes
- Uses PowerShell scripts to elevate privileges and run encryption tasks
Persistence
- Creates startup registry keys for reboot persistence
- Deploys secondary payloads scheduled to relaunch ransomware activity
Defense Evasion
- Disables system antivirus and security tools
- Deletes system restore points and shadow copies to prevent recovery
Credential Theft and Network Discovery
- Uses tools resembling Mimikatz and LaZagne to extract passwords
- Scans connected networks to identify accessible hosts and shares
Exfiltration and Damage
- Steals data before encryption for possible double-extortion schemes
- Uses the Telegram API as a communication and control mechanism
- Encrypts all major file categories including documents, images, and archives
Indicators of Compromise (IOCs)
| Category | Details |
| Encrypted File Extension | .lbon or other four-character random suffix |
| Ransom Note Name | read_it.txt |
| Communication Channel | Telegram handle: @Privaky |
| Common Detections | Win32:MalwareX-gen [Ransom], Trojan-Ransom.Win32.Generic |
| Associated Processes | privaky.exe, chaos_build.exe |
| Registry Persistence Keys | HKCU\Software\Microsoft\Windows\CurrentVersion\Run\privaky |
Statistical Data and Victim Insights
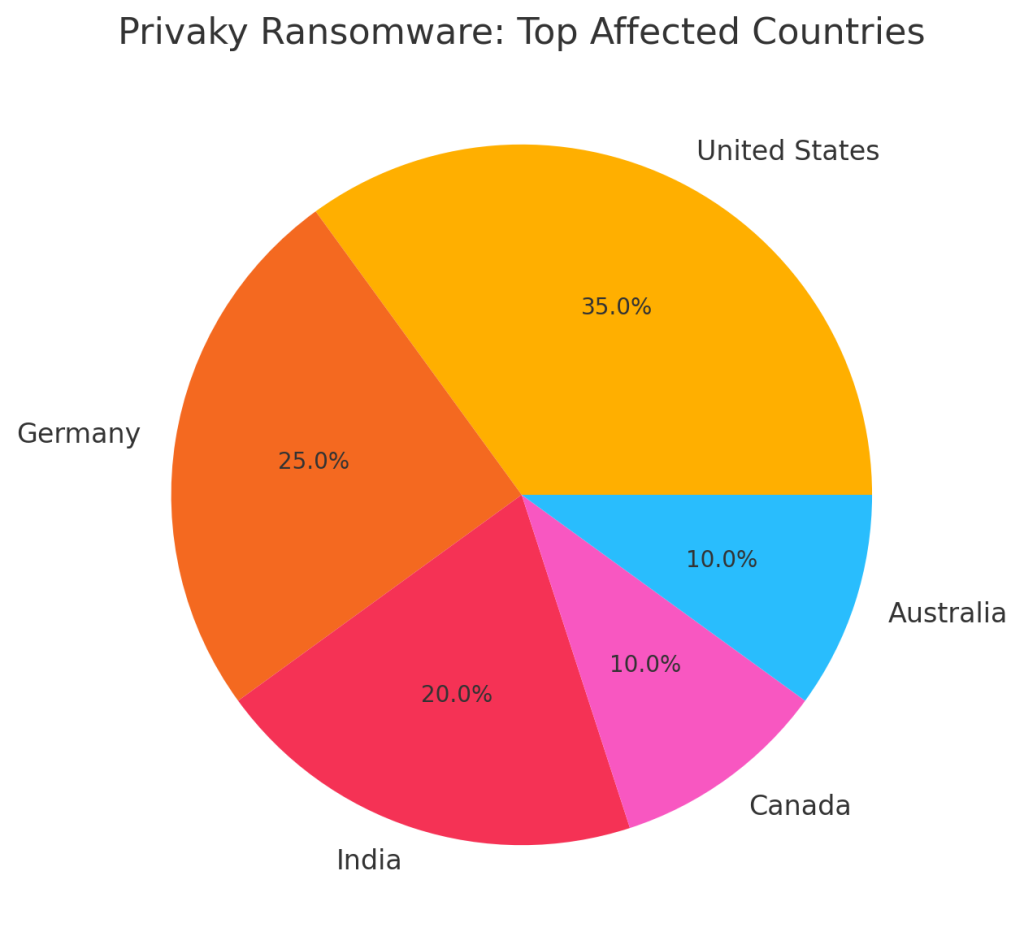
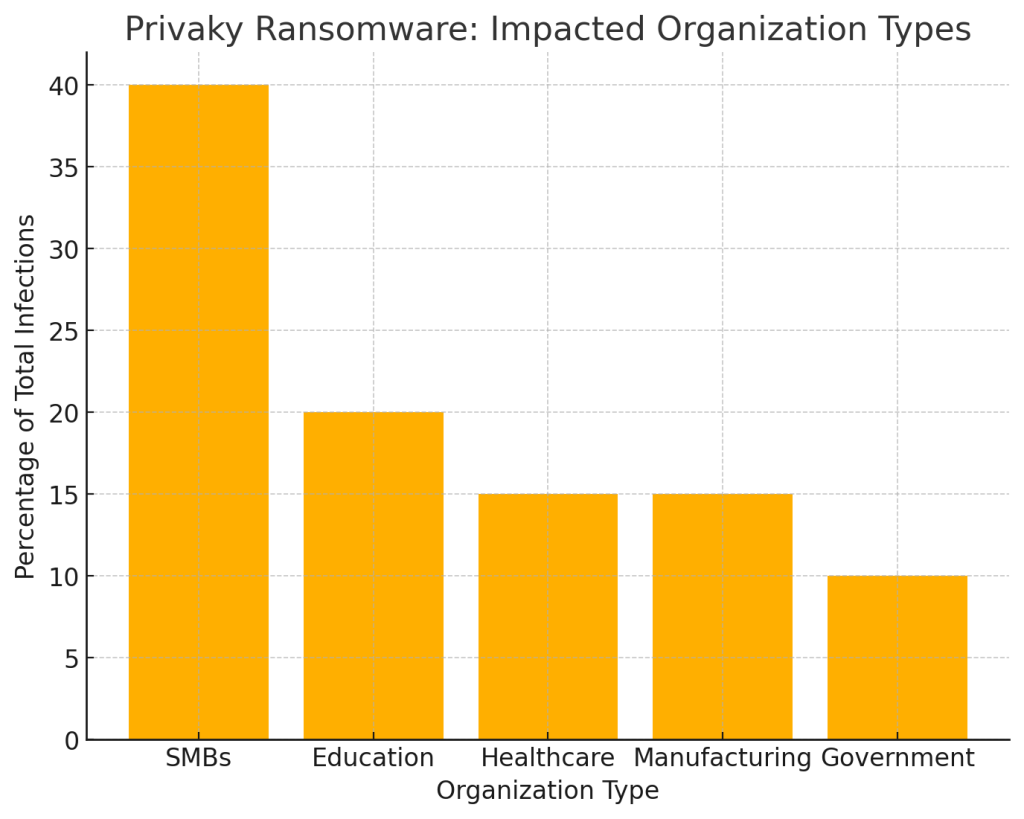
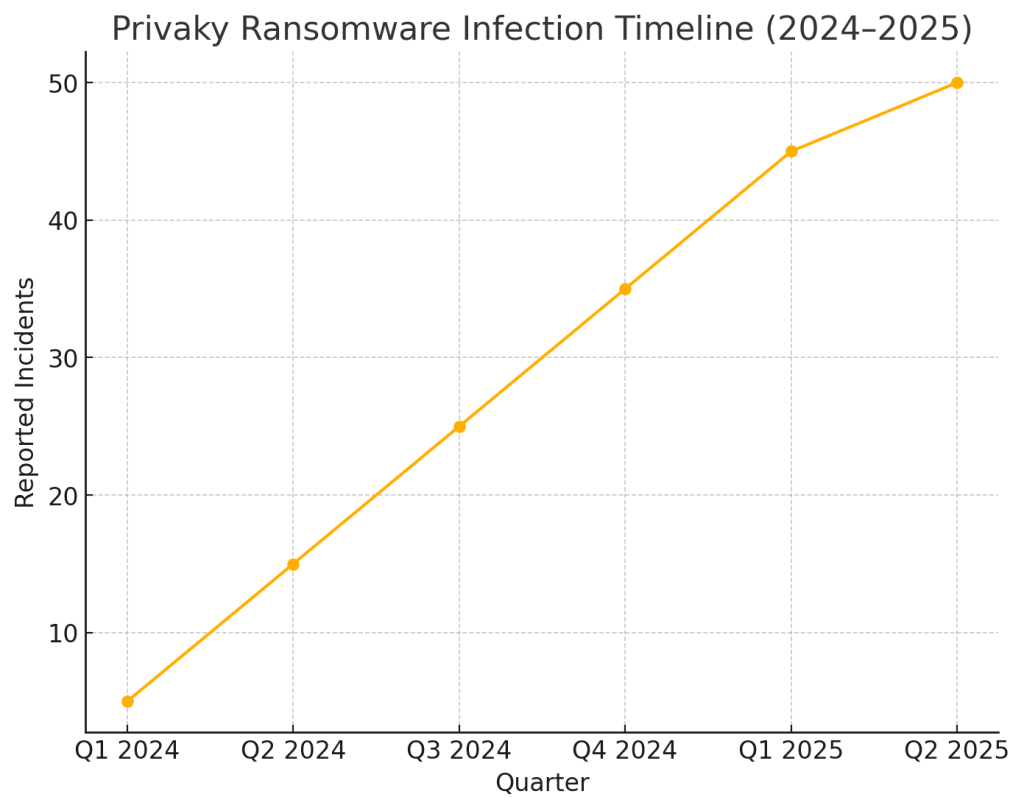
Privaky has caused widespread disruptions across industries, notably in North America, Europe, and Asia-Pacific. Small enterprises, hospitals, and educational institutions remain prime targets due to limited security resources.
Top Affected Countries
Organizations Impacted
Timeline of Privaky Attacks
Security Measures and Hardening Recommendations
- Implement multi-factor authentication (MFA) for all remote access points.
- Regularly patch systems and close vulnerabilities in VPNs, firewalls, and servers.
- Segment your network to prevent lateral movement in case of breach.
- Adopt EDR and real-time monitoring to catch anomalies early.
- Maintain immutable backups, preferably offline or in secure cloud snapshots.
Conclusion
Privaky ransomware exemplifies the growing sophistication of modern encryption-based cyberattacks. Despite its complexity, effective recovery is achievable through professional guidance and structured remediation.
Our Privaky Decryptor has successfully helped numerous victims reclaim encrypted data without paying ransoms. With the right combination of expert tools, swift containment, and proactive defenses, organizations can not only recover but also strengthen their future cybersecurity posture.
MedusaLocker Ransomware Versions We Decrypt